Top 5 most important network protocols for cybersecurity beginners
Most beginners waste months trying to learn networking the wrong way. If you're starting your cybersecurity career, these are the 5 protocols you should focus on first.
Back when I wanted to get into cybersecurity, everybody kept telling me to “learn networking.”
Great. I can do that.
I sat down and started learning.
After a while, I realized there is an infinite number of things that I could be learning and that I had no idea what to focus on.
I was jumping from one topic to another, TCP today, DNS tomorrow, VLANs next week, without really knowing what actually mattered.
It felt like trying to drink from a fire hose.
If this sounds familiar, you’re not alone.
The truth is: you don’t need to learn everything at once!
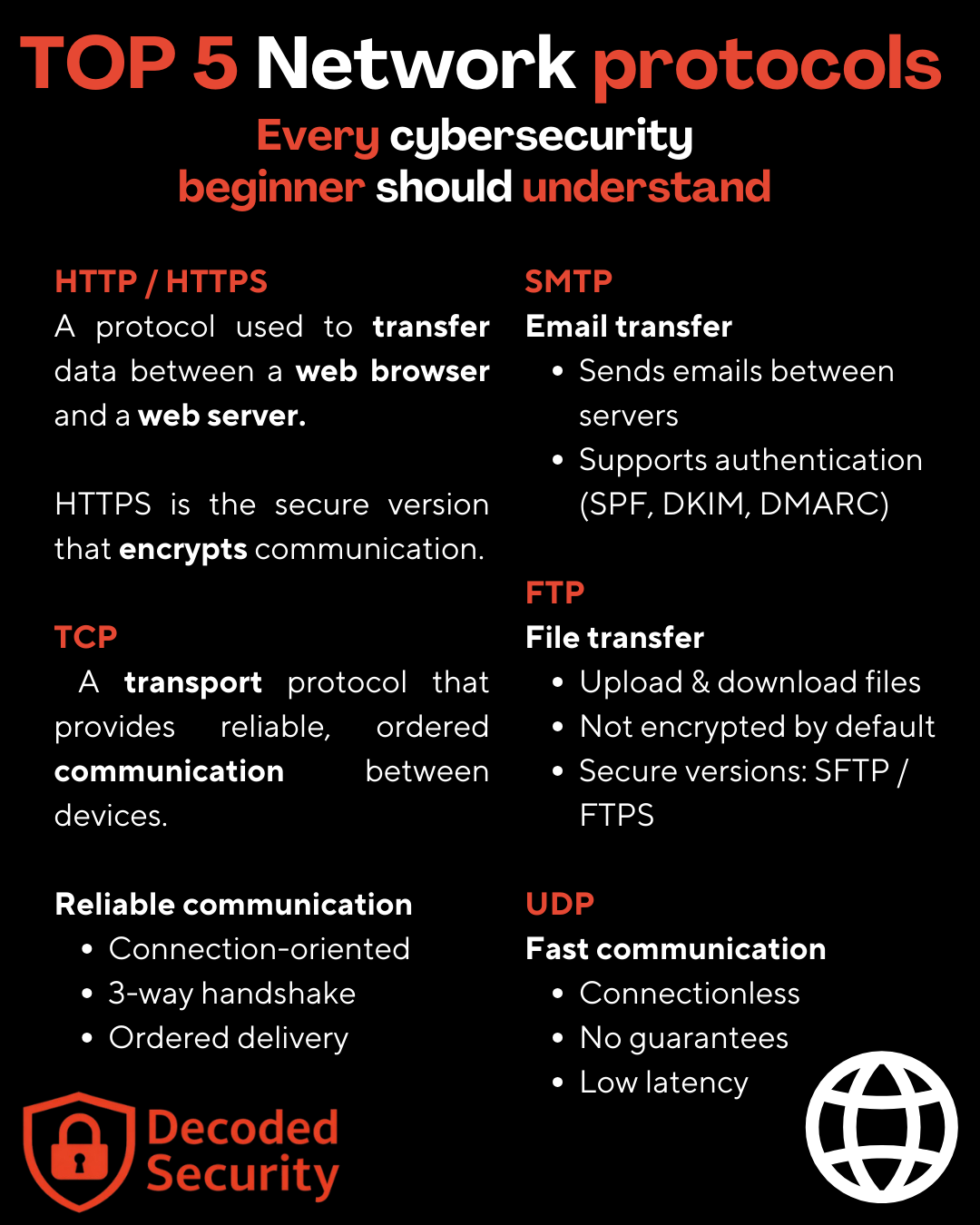
In this article, I’ll show you the 5 most important network protocols every cybersecurity beginner should understand and why they matter in real-world security.
Before we get into that, please make sure you understand the TCP/IP model and its layers.
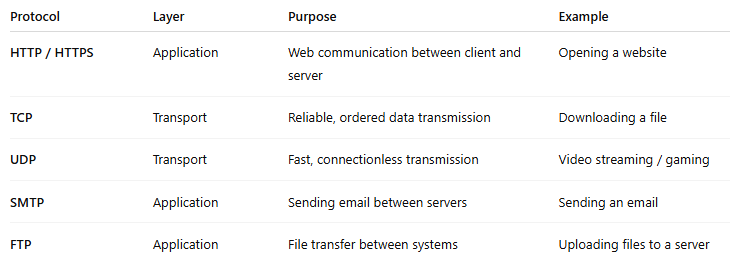
HTTP/HTTPS
Layer: Application Layer (Layer 7 - ISO/OSI model, Layer 4 TCP/IP model)
Function:
Transfers web data between a client and a web server. Typically between user’s browser and a web server.
Process:
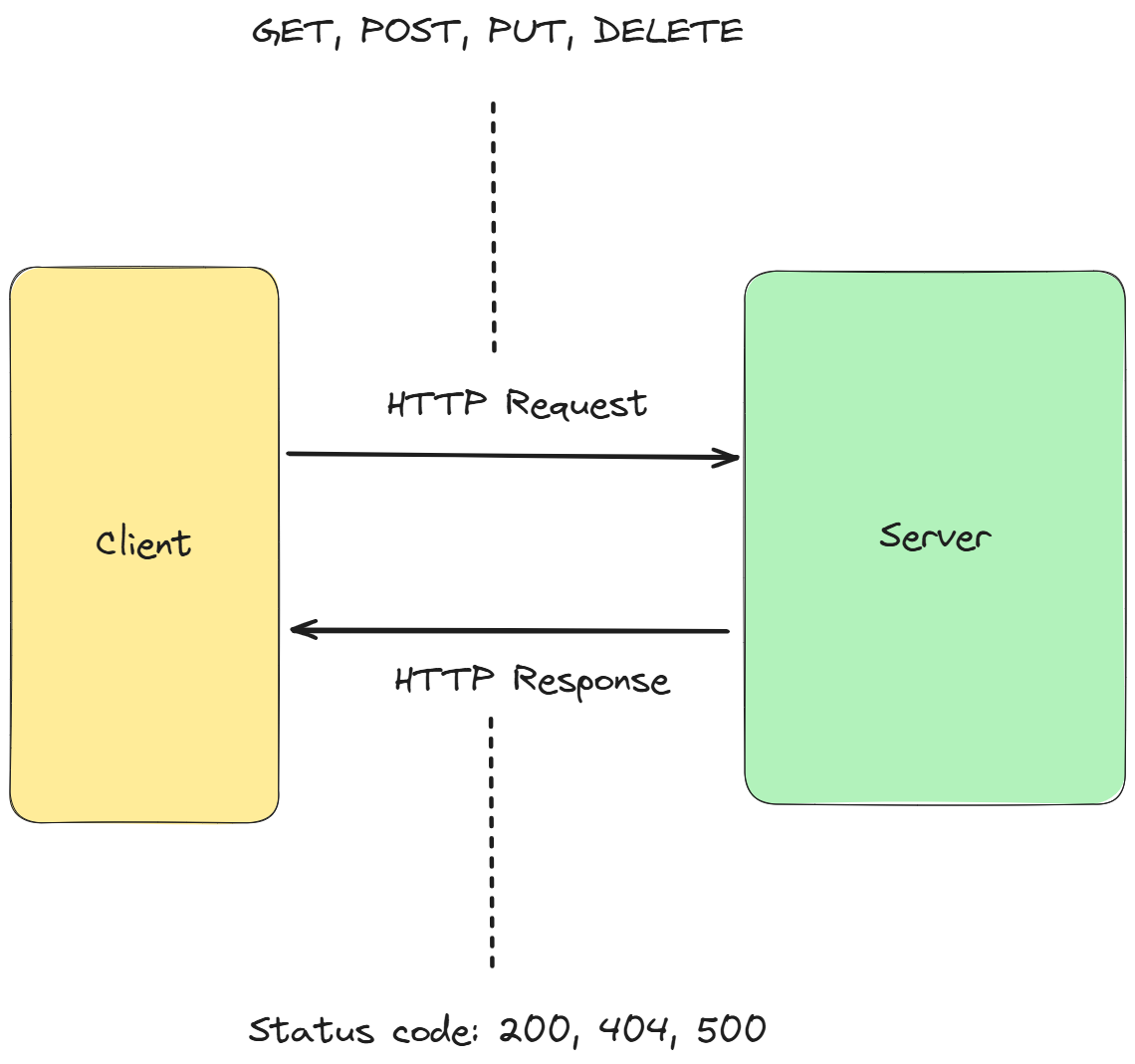
HTTP uses a request–response model. A client (browser) sends an HTTP request to a server, and the server responds with content (HTML, images, API data, etc.).
Not sure what it means? Maybe this picture will help you.
Looking at this picture, two questions might pop in your head.
What are HTTP methods and what are the Status codes?
Let’s take it step by step.
An HTTP method defines the action that a client wants to perform on a resource located on a web server.
There are 4 main methods:
GET (Read) → Retrieve data from a server
POST(Create) → Send data to the server (e.g., login form submission)
PUT(Update) → Update or replace data on the server
DELETE(Delete) → Remove data from the server
HTTP response codes (also called status codes) are messages sent by the server to tell the client what happened with the request.
In simple terms:
Status codes tell you whether your request worked, or why it failed.
Remember that famous Error 404? Yes, that is a response code!
Why it matters to cybersecurity:
Most internet traffic today is web traffic. Many attacks target web communication, including:
Man-in-the-Middle (MitM)
Session hijacking
Credential theft
Web application attacks (XSS, SQL injection)
And if you want to protect your systems agains those attacks, you need to understand this protocol first!
Note: HTTPS works the same way but adds TLS encryption, which protects the communication from interception or tampering.
TCP (Transmission Control Protocol)
Layer: Transport Layer (Layer 4 — ISO/OSI model, Layer 3 — TCP/IP model)
Function:
Provides reliable, ordered, and error-checked delivery of data between devices.
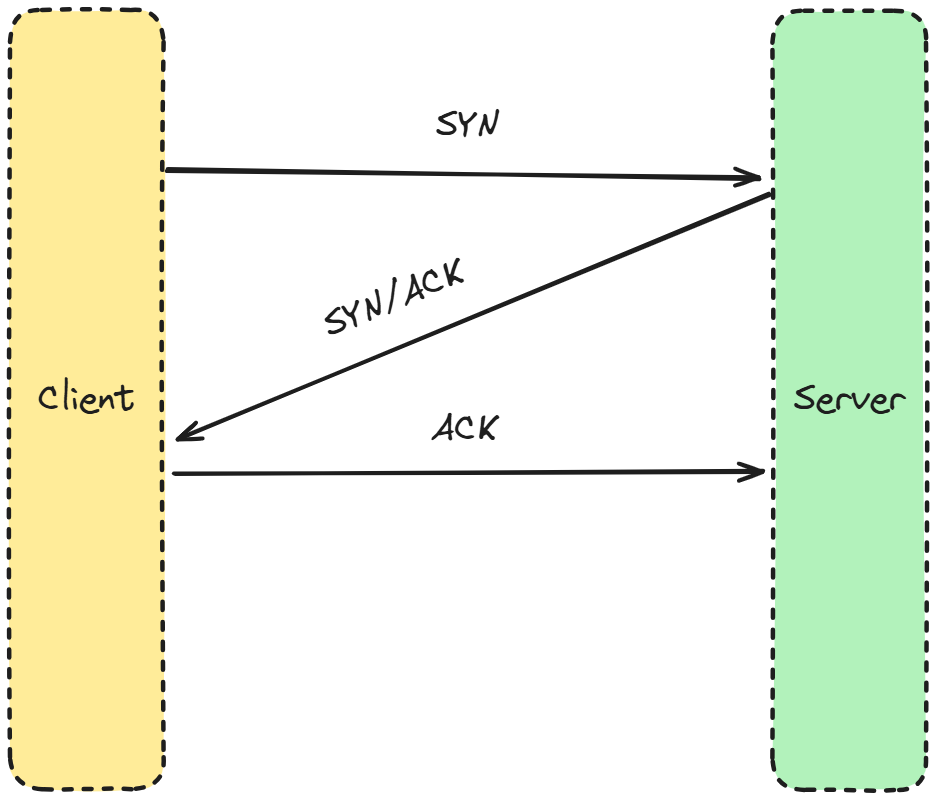
Make sure to understand the three-way handshake!
Process:
Before sending data, TCP establishes a connection between two devices using something called a three-way handshake:
SYN → Client wants to start communication
SYN-ACK → Server acknowledges
ACK → Client confirms
Once the connection is established, data can be transmitted reliably. TCP ensures that:
Packets arrive in the correct order
Missing packets are retransmitted
Communication is stable
Understanding TCP helps you understand:
Port scanning
Network connections
Session hijacking
SYN flood attacks (DoS)
Firewall behavior
If you don’t understand TCP, you don’t really understand how systems communicate.
UDP (User Datagram Protocol)
Layer: Transport Layer (Layer 4 — ISO/OSI model, Layer 3 — TCP/IP model)
Function:
Provides fast, connectionless data transmission without reliability guarantees.
Process:
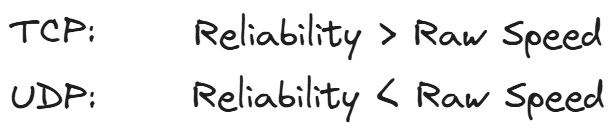
Unlike TCP, UDP does not establish a connection before sending data.
It simply sends packets (called datagrams) to the destination without:
Acknowledgments
Retransmissions
Ordering guarantees
This makes UDP much faster, but less reliable. (SEND AND HOPE)
Why it matters to cybersecurity:
UDP is commonly used in:
DNS
Video streaming
Online gaming
VoIP
It is also heavily abused in DDoS amplification attacks because attackers can send large volumes of traffic quickly.
Understanding UDP explains why some attacks can generate massive traffic and overwhelm systems.
If you want know more about differences between UDP and TCP, let me know in the comments!
SMTP (Simple Mail Transfer Protocol)
Layer: Application Layer (Layer 7 — ISO/OSI model, Layer 4 — TCP/IP model)
Function:
Used to send emails between mail servers and from clients to servers.
SMTP is curerntly a standard for transferring email messages.
Process:
A user sends an email from their email client.
The email is transferred to a mail server using SMTP.
The server forwards the message to the recipient’s mail server.
The recipient retrieves it using another protocol (like IMAP or POP3). - DIFFERENT PROTOCOL
SMTP was originally designed without strong security, which is why additional protections were later added (SPF, DKIM, DMARC).
Why it matters to cybersecurity:
Email is the number one attack vector in cybersecurity.
Understanding SMTP helps you understand:
Phishing attacks
Email spoofing
Malware delivery
Business Email Compromise (BEC)
Email authentication mechanisms
If you work in security, you will deal with email threats constantly.
Example:
Sending an email from Gmail or Outlook.
FTP (File Transfer Protocol)
Layer: Application Layer (Layer 7 — ISO/OSI model, Layer 4 — TCP/IP model)
Function:
FTP allows efficient uploading and downloading of files between hosts.
Process:
FTP uses two separate connections:
A control connection (commands)
A data connection (file transfer)
Traditional FTP does not encrypt communication, meaning:
Usernames
Passwords
Files
can be intercepted.
Because of this, secure alternatives were created:
SFTP (SSH File Transfer Protocol)
FTPS (FTP over TLS)
Why it matters to cybersecurity:
FTP is a classic example of an insecure legacy protocol still found in many environments.
Security professionals need to understand it because:
Credentials can be captured easily
Servers are often misconfigured
Attackers frequently scan for exposed FTP services
It teaches an important lesson:
Just because a protocol exists doesn’t mean it is secure.
Example:
Uploading files to a web hosting server.
Great! Let’s sum it all up now.
What now?
If you’re reading this, congratulations.
Understanding these protocols is a great start and absolutely crucial for certification exams such as CC, Security+, or CISSP.
More importantly, it means you’re beginning to understand how systems actually communicate, and that’s the foundation of cybersecurity.
I know it can feel overwhelming at times, so here are the key takeaways I want you to remember:
You don’t need to learn everything at once. Focus on the fundamentals first.
Most cyber attacks exploit communication between systems, networking knowledge gives you visibility into that.
TCP and UDP are crucial transport layer protocols. Make sure to understand the differences between them.
Make sure to understand at which ISO/OSI layer the protocol operates
If you master these basics, you’re already ahead of most people!
Keep going.
Let’s connect
If you want to collaborate, discuss, or just geek out over virtualization and cloud security, reach out to me:
Email: erich.winkler@decodedsecurity.com
LinkedIn: Erich Winkler
Gumroad community: Decoded Security
Enjoyed this article? Like it or drop a comment. I’d love to hear your thoughts and questions!
Let’s learn and grow together!


Can you please post windows internals.
I need to understand it ,
Cuz am a newbie into cyber security industry