Stop Memorizing Security Models: Use This 2-Question CISSP Filter
Most CISSP candidates try to memorize every security model. This simple filter helps you understand what each model protects and how to answer exam questions faster.
📚 Essential CISSP topic
If you’re preparing for the CISSP exam or are serious about your cybersecurity career, make sure to read this.
Because this is one of the topics that distinguishes juniors from senior professionals.
When I hit security models in Domain 3, my instinct was the same as most candidates:
Open the book. Highlight every name. Make flashcards. Hope my brain hangs on until exam day.
Bell-LaPadula. Biba. Clark-Wilson. Brewer-Nash. Graham-Denning. Take-Grant.
Eight names. Multiple rules each. Some protect confidentiality, some protect integrity, and some have weird rules that I don’t understand.
And here’s the uncomfortable truth 👇
The candidates who fail this section aren’t the ones who forgot a definition. They’re the ones who memorized all eight and still couldn’t answer the question.
This article isn’t a textbook dump. It’s a way to compress 30 pages of CISSP content into a mental shortcut you can actually use on exam day.
And it's something that helped me pass the CISSP exam in 3 months!
Warning: This is one of the most tested topics in CISSP Domain 3.
What is a security model?
A security model is just a formal representation of a security policy. It defines:
Who (Subject) can access what (Object)
Under what conditions
Which kind of protection it enforces (confidentiality, integrity, or both)
Note: If you’re not familiar with terms such as Subject and Object, read this first: Access Controls: Who Gets the Keys?
I know, it all sounds boring.
That’s why most candidates default to rote memorization. (Luckily I have a very bad memory, so that wasn’t an option for me)
Then the exam hits them with a question like this:
“A defense contractor needs to prevent classified intelligence from leaking to lower clearance levels. Which model best supports this requirement?”
Notice what the question is not asking:
It’s not asking for the definition
It’s not asking who invented it
It’s not asking which government uses it
It’s asking: What goal needs to be protected, and which model was built for that exact goal?
That’s the whole game.
Security models are just answers to specific real-world problems. Once you know the problem, the model picks itself.
Not sure what to learn next? Get a personalized study plan based on your background and goals: Start the quiz
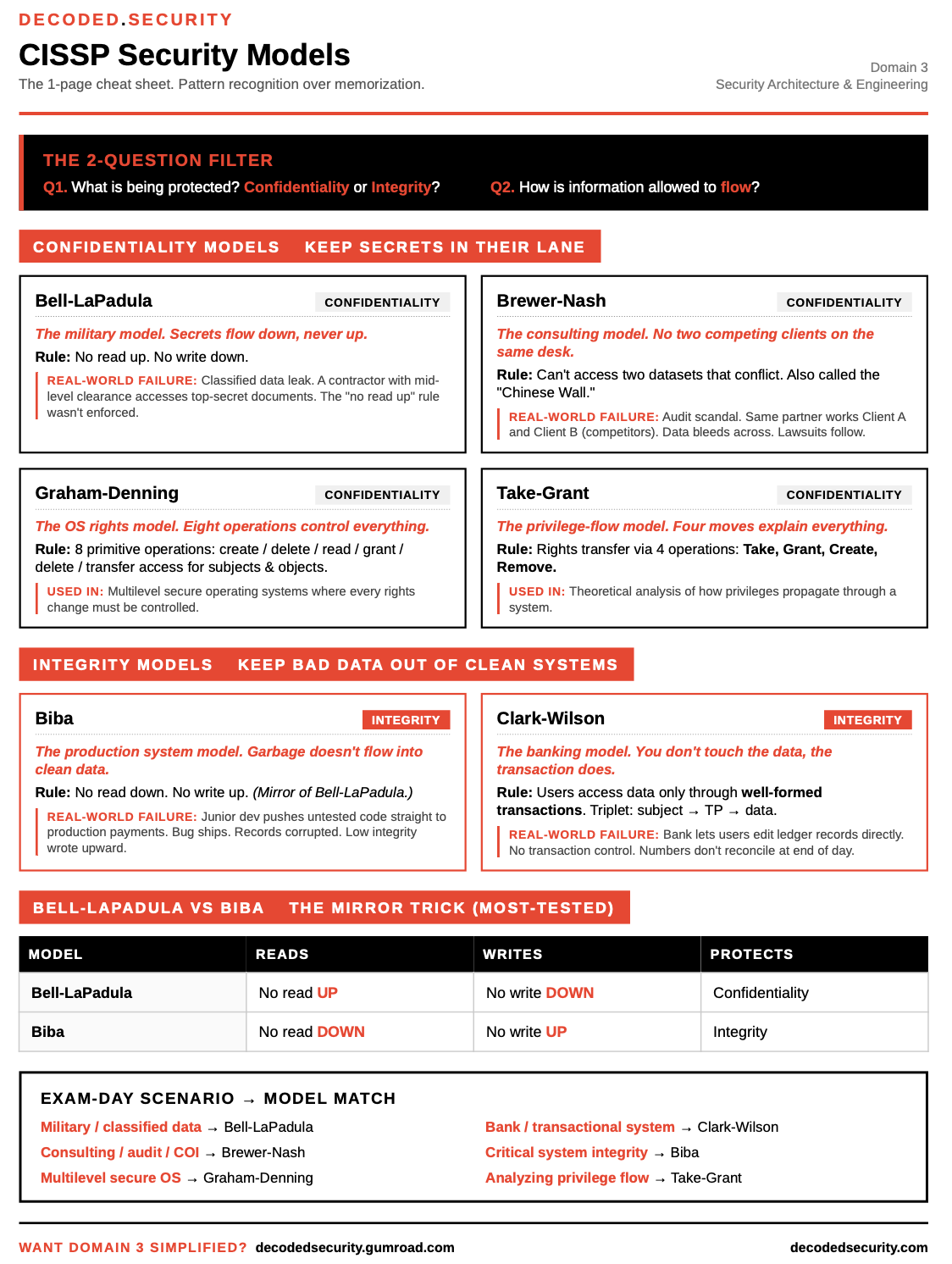
The 2-Question Filter
As I have mentioned, I have a terrible memory. That’s why I created my personal Decoded Security framework to make sure I can choose the right model in any situation.
For every security model question on the exam, I ask:
Q1: What is being protected? Confidentiality or integrity?
Q2: How is information allowed to flow?
If you can answer those two, you’ll get more than 80% of model questions right without remembering a single rule by heart.
Here’s the map.
Models That Protect CONFIDENTIALITY
These models exist for one reason: To ensure confidentiality.
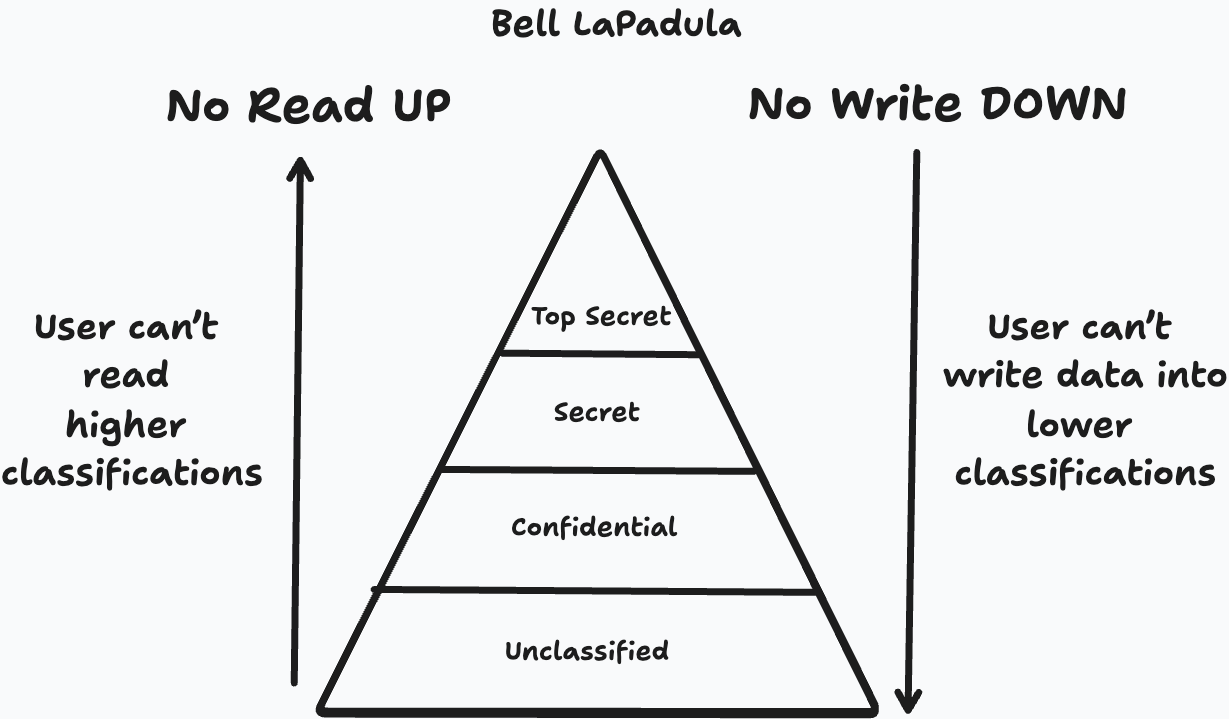
Bell-LaPadula
Rules:
No read up (The simple security rule)
No write down (The * property rule).
The strong property rule: Subject's clearance and objects classification needs to be equal
A junior analyst can’t read top secret. A general can’t write classified info into an unclassified channel.
Built for: U.S. Department of Defense. Multilevel military systems.
Memory hook: BLP = Block Leakage of secrets properly.
Brewer-Nash (Chinese Wall)
This particular security model is really interesting. Basically, it is a set of rules that say: If you can access A, you can’t access B. And this all happens within one company.
Rule: You can’t access two datasets that conflict.
A consultant working with Bank A can’t suddenly access Bank B’s files.
Built for: Financial firms, law firms, audit firms.
Memory hook: Brewer = Builds walls between conflicting clients.
Graham-Denning
Note: Not that important for the exam.
Rule: 8 primitive operations control the creation, deletion, and granting of rights for subjects and objects.
Built for: Multilevel secure operating systems.
Take-Grant
Note: Not that important for the exam.
Rule: Rights transfer between subjects via 4 operations: Take, Grant, Create, Remove.
Built for: Theoretical analysis of how privileges propagate through a system.
Models That Protect INTEGRITY
These flip the script. They don’t care if you read something. They care that you don’t write garbage into critical systems.
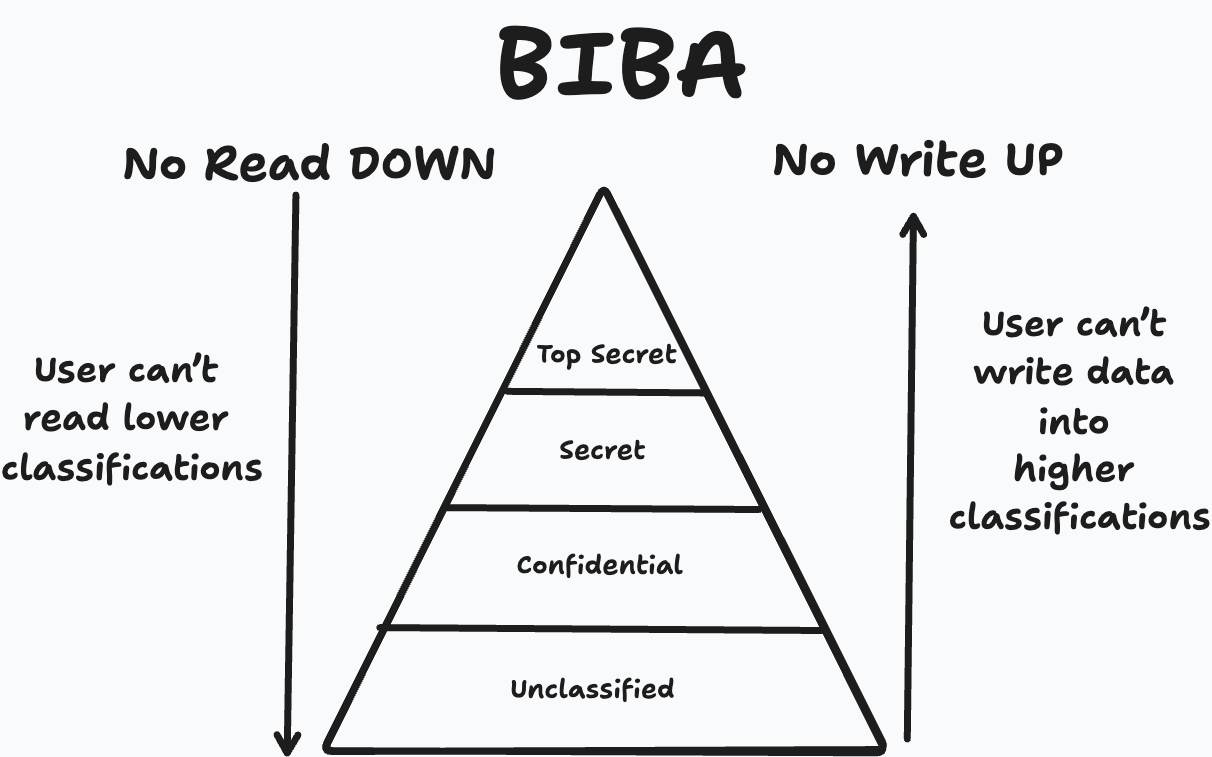
Biba
Rule: No read down (simple integrity axiom). No write-up (*-integrity axiom).
A low-integrity process can’t pollute high-integrity data. A junior dev can’t push untested code directly into production payments.
Built for: Systems where data corruption is worse than data exposure.
Memory hook: Biba = Block Bad data going UP.
Clark-Wilson
Rule: Users don’t touch data directly. They access it through well-formed transactions.
Just remember here that the user does not access the data directly, but only through predefined procedures.
You might get a question about what the “access control triplet” is:
It is the relationship between a user and a set of programs that operate on a set of data items.
Subjects → transformation procedures (programs) → data (Data items)
Built for: Banking, accounting, transactional databases.
This is the model behind every system where you can’t edit a record without a controlled workflow.
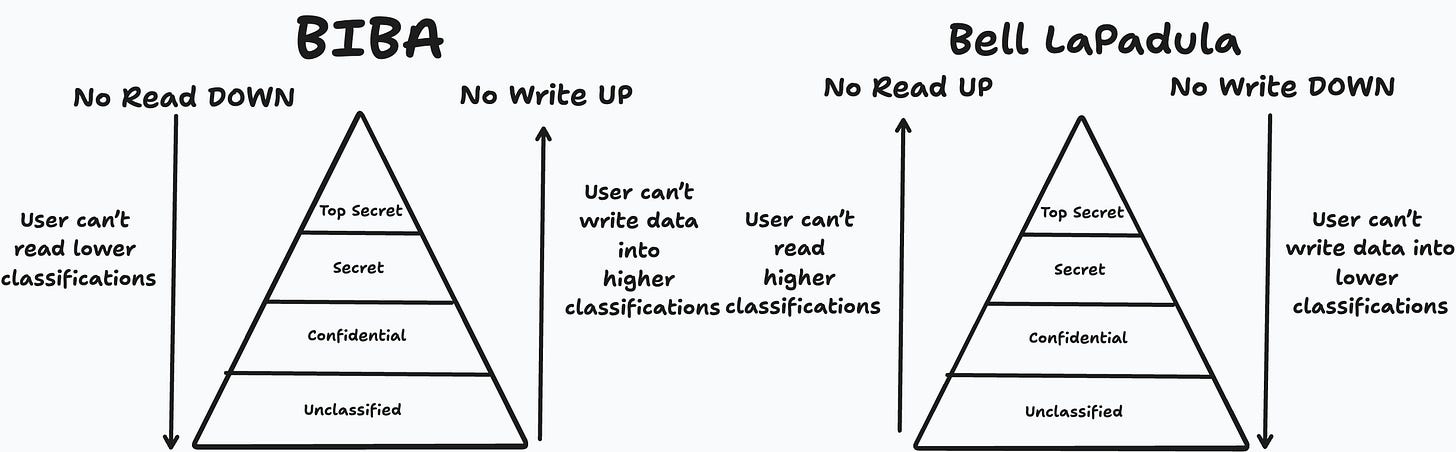
Bell-LaPadula vs Biba: The mirror trick
These two are the most tested models on the exam.
The simplest way to keep them straight:
They are literal mirrors of each other.
If you remember one, you can derive the other by flipping the arrows.
I’ll include a clean mirror diagram in the published version. If you want a printable cheat sheet, comment “Cheatsheet” and I’ll send it to you!
How to apply this on exam day
Read the scenario. Identify two things:
What is the threat? Leakage = confidentiality model. Corruption = integrity model.
What environment?
Military / classified data → Bell-LaPadula
Bank / transactional system → Clark-Wilson
Consulting / audit / conflict of interest → Brewer-Nash
Critical system integrity → Biba
That’s it.
Most questions don’t require you to recite the “star property” or the “discretionary property.” They require you to match a real-world problem to the model that was designed for it.
If you want the deeper foundation behind these models, my earlier article on the 8 Security Principles every CISSP candidate thinks they understand covers the design thinking these models came from.
Key Takeaways
Don’t memorize models. Memorize what they protect.
Group them: confidentiality vs integrity.
Bell-LaPadula and Biba are mirrors. Learn one, and you get both for free.
Clark-Wilson is the banking model. Brewer-Nash is the consultant model. Bell-LaPadula is the military model.
Exam questions reward pattern recognition, not definitions.
Conclusion
I know that Security models can sound very abstract at first, but there is a reason the CISSP tests as much as it does.
It allows security professionals to create a general framework and design systems based on the business needs, not the other way around!
I have spent days trying to figure this all out, and I truly hope this will help you get it in under 90 minutes!
Good luck, and thank you for reading Decoded Security!
PS: Here is a printable cheatsheet to make it all easier for you!
Not sure what to learn next? Get a personalized study plan based on your background and goals: Start the quiz
Want the rest of Domain 3 simplified?
Security models are one piece. Domain 3 also covers cryptography, secure design principles, system architecture, and security capabilities of information systems. It’s the heaviest, most technical domain on the exam.
If you want a structured way to master it without losing your mind, I have something just for you:
👉 CISSP Domain 3: Complete Guide
Built the same way: pattern recognition over memorization.
Let’s Connect
If you want to collaborate, discuss, or just geek out over networking and cybersecurity, reach out:
Email: erich.winkler@decodedsecurity.com
LinkedIn: Erich Winkler
Gumroad community: Decoded Security
Start Here: Decoded Security Roadmap
Enjoyed this article? Like it or drop a comment. I’d love to hear your thoughts and questions!
Let’s learn and grow together!