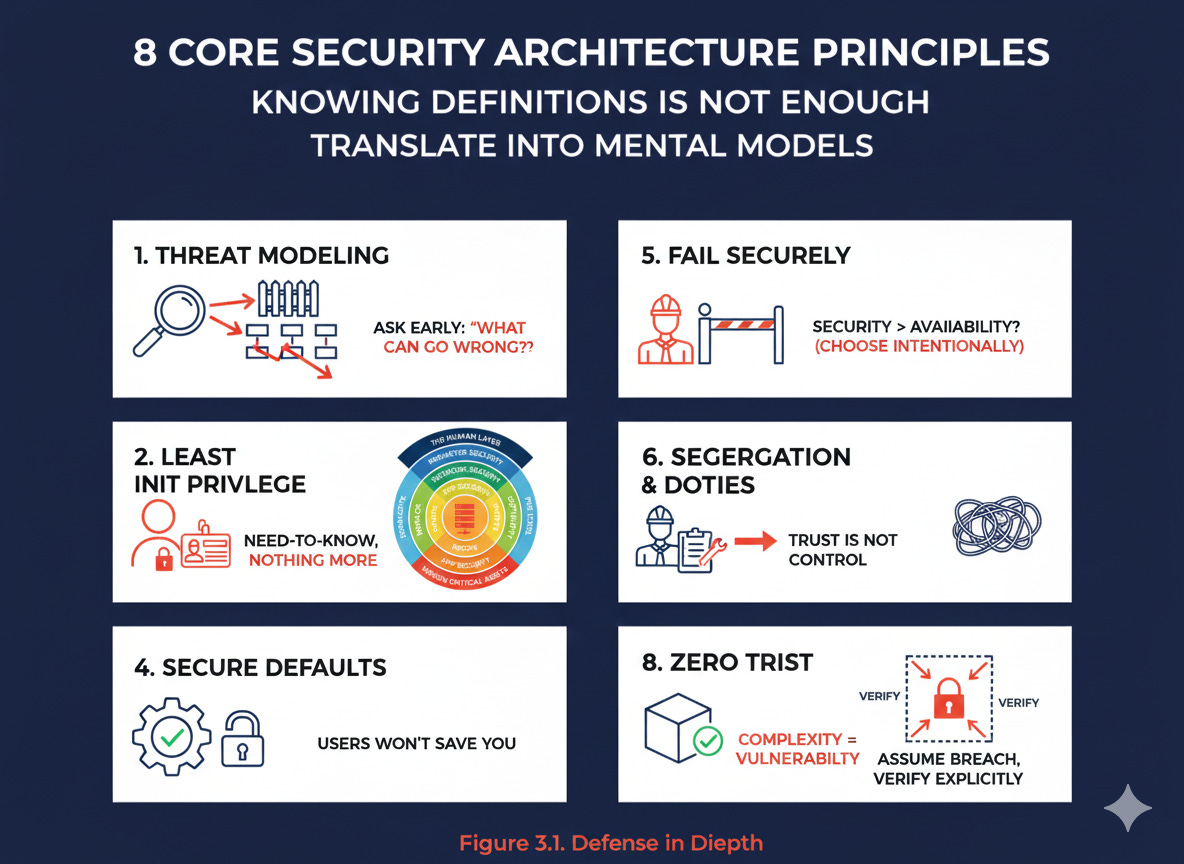
The 8 Security Principles Every CISSP Candidate Thinks They Understand (Until They Don’t)
You know all the principles. So why do your systems still fail? The uncomfortable truth about threat modeling, least privilege, and defense in depth. This is what you need to know.
When I started Domain 3 of my CISSP prep, I thought this part would be easy.
Threat modeling. Least privilege. Defense in depth.
I’ve used these terms for years.
But here’s the uncomfortable truth 👇
Knowing the definition is not the same as designing systems that survive reality.
This post is my attempt not only to introduce you to core security architecture principles but also to translate them from “exam knowledge” into mental models you can actually apply.
This article is for you if:
You’re preparing for the CISSP and want to understand why these principles matter, not just memorize definitions for the exam.
You already work in cybersecurity, IT, or engineering and feel the gap between textbook security and what actually survives in production.
You’re moving (or want to move) from hands-on execution to architectural or managerial thinking.
You’ve seen security controls fail and want mental models that help you design systems that fail less and fail better.
You’re tired of security advice that sounds correct but collapses the moment real constraints appear.
Warning: Crucial topic for the CISSP exam.
Table of Contents
Threat Modeling: The Cheapest Security Control You’ll Ever Buy
Least Privilege: The Principle Everyone Agrees With — and Violates
Defense in Depth: Assume Something Will Fail
Secure Defaults: Users Will Not Save You
Fail Securely: Decide What Matters More — Security or Availability
Segregation of Duties: Trust Is Not a Control
Keep It Simple and Small: Complexity Is a Vulnerability
Zero Trust vs. “Trust but Verify”
Each section reframes a well-known principle into a design decision you’ll actually face in real systems.
1. Threat Modeling: The Cheapest Security Control You’ll Ever Buy
Threat modeling isn’t a document.
It’s a habit of asking the right questions early.
You can do it:
Proactively → during design (cheap, effective)
Reactively → after deployment (expensive, messy)
CISSP expects you to know STRIDE, DREAD, OCTAVE, TRIKE.
Reality expects you to answer one question:
“What can go wrong here, and how bad would it be?”
Real-world example of how to use the STRIDE method!
Lesson learned:
Threat modeling done late is incident response in disguise.
Threat modeling isn’t about predicting every attack. It’s about removing the obvious failures before attackers find them for you.
2. Least Privilege: The Principle Everyone Agrees With and Violates
Least privilege means:
Give people and systems only what they need, and nothing more.
Simple.
Painful in practice.
Why?
“Just give admin, it’s faster.”
“We’ll clean it up later” (you won’t)
Legacy systems
Least privilege:
Reduces the likelihood of incidents
Reduces blast radius when something breaks
Design insight:
Least privilege must exist before users exist.
Every unnecessary permission is a future incident waiting for the right moment.
3. Defense in Depth: Assume Something Will Fail
Defense in depth means layers, not perfection.
If one control fails:
→ another is already waiting.
This applies to:
Physical
Logical
Administrative controls
It’s also why Zero Trust works.
A useful mental image is concentric circles:
Perimeter
Building
Room
Vault
Asset
Each layer has its own security controls.
Design reality:
Single points of failure are not “efficient”, they’re optimistic.
Enjoying reading this article? Let me know in the comments!
4. Secure Defaults: Users Will Not Save You
Secure defaults assume:
Users won’t configure security correctly, and that’s okay.
So you:
Enable encryption by default
Enforce strong passwords
Log everything
Limit access out of the box
This isn’t user-hostile.
It’s user-respectful.
If your system is insecure by default, your security depends on user discipline. That’s not a strategy.
5. Fail Securely: Decide What Matters More - Security or Availability
If a firewall is overwhelmed, should it stop all traffic or forward everything?
The correct answer is: It depends.
Fail securely (fail closed):
Access denied
Traffic blocked
Security preserved
Fail open:
Access allowed
Availability preserved
Security bypassed
Neither is “right”.
The mistake is not choosing intentionally.
CISSP wants you to know:
This is a design decision, not a configuration error.
CISSP Exam Tip: Human life is always the highest priority.
If an exam scenario implies that failing securely (fail closed) could endanger human life, the correct choice is fail open, even though it weakens security.
CISSP tests risk-based thinking, not absolute security.
6. Segregation of Duties: Trust Is Not a Control
Segregation of Duties (SoD) exists because:
People make mistakes, and sometimes bad decisions.
That’s why we need to prevent one person from causing excessive damage to our company.
We need to:
Separate dev/test/prod
Separate approval/execution
Require multiple roles for critical actions
It’s not about mistrust. (Or is it?)
It’s about system resilience.
If one person can break everything alone, your controls are decorative.
7. Keep It Simple and Small: Complexity Is a Vulnerability
KISS exists because:
Every extra component is another failure mode.
Security favors:
Fewer systems
Clear ownership
Understandable flows
This is why best-in-suite often beats best-in-breed.
Not because it’s “better”, but because it’s manageable.
Just because even you can’t figure out how your system works doesn’t mean the attacker won’t.
8. Zero Trust vs. “Trust but Verify”
Trust but verify assumed:
Perimeter = safe
Inside = trusted
That world is gone. You should be familiar with this concept, but do not implement it anywhere.
And trust me, it won’t be a correct answer on the exam!
Zero Trust says:
Assume breach
Verify explicitly
Enforce least privilege
Achieved via:
Microsegmentation
Identity-based access
Policy enforcement
Defense in depth supports Zero Trust.
Perimeter trust undermines it.
Zero Trust isn’t paranoia. It’s how we protect modern systems from modern threats.
The core security principles are just one small piece of the puzzle of the CISSP exam.
If you want a structured way to master Domain 1 of the CISSP exam, I’ve created something for you.
My CISSP Domain 1 Checklist provides clarity and focus on everything that truly matters for the exam and real-world practice.
➡️ Download it here and stop wasting time on scattered study materials.
Conclusion
As always, if you’re reading this, congratulations! You just made another step in becoming a Cybersecurity professional.
Threat modeling, least privilege, defense in depth, zero trust..
These aren’t definitions to recite. They’re design decisions you must defend when systems fail, budgets shrink, users make mistakes, and attackers get lucky.
That’s what the CISSP exam is really testing:
Can you reason under constraints?
Can you balance security, availability, safety, and usability?
Can you choose the least bad option when perfection isn’t possible?
If you take one thing from this article, let it be this:
Good security isn’t rigid. It’s intentional.
And CISSP rewards people who think that way.
Any feedback is greatly appreciated!
If this helped you reframe familiar concepts into practical mental models,
follow Decoded Security!
Ready to level up your cybersecurity skills?
💬Comment below and tell me what your experience with SLAs is
❓Take the quiz to test your understanding: CybersecErich: Quiz Hub
📰Subscribe (free or paid) to get new posts straight to your inbox.
Share this with a friend studying for CISSP, or anyone curious about cybersecurity.