I have watched people waste €4,000 on the wrong certification. Here is how to make sure you are not next.
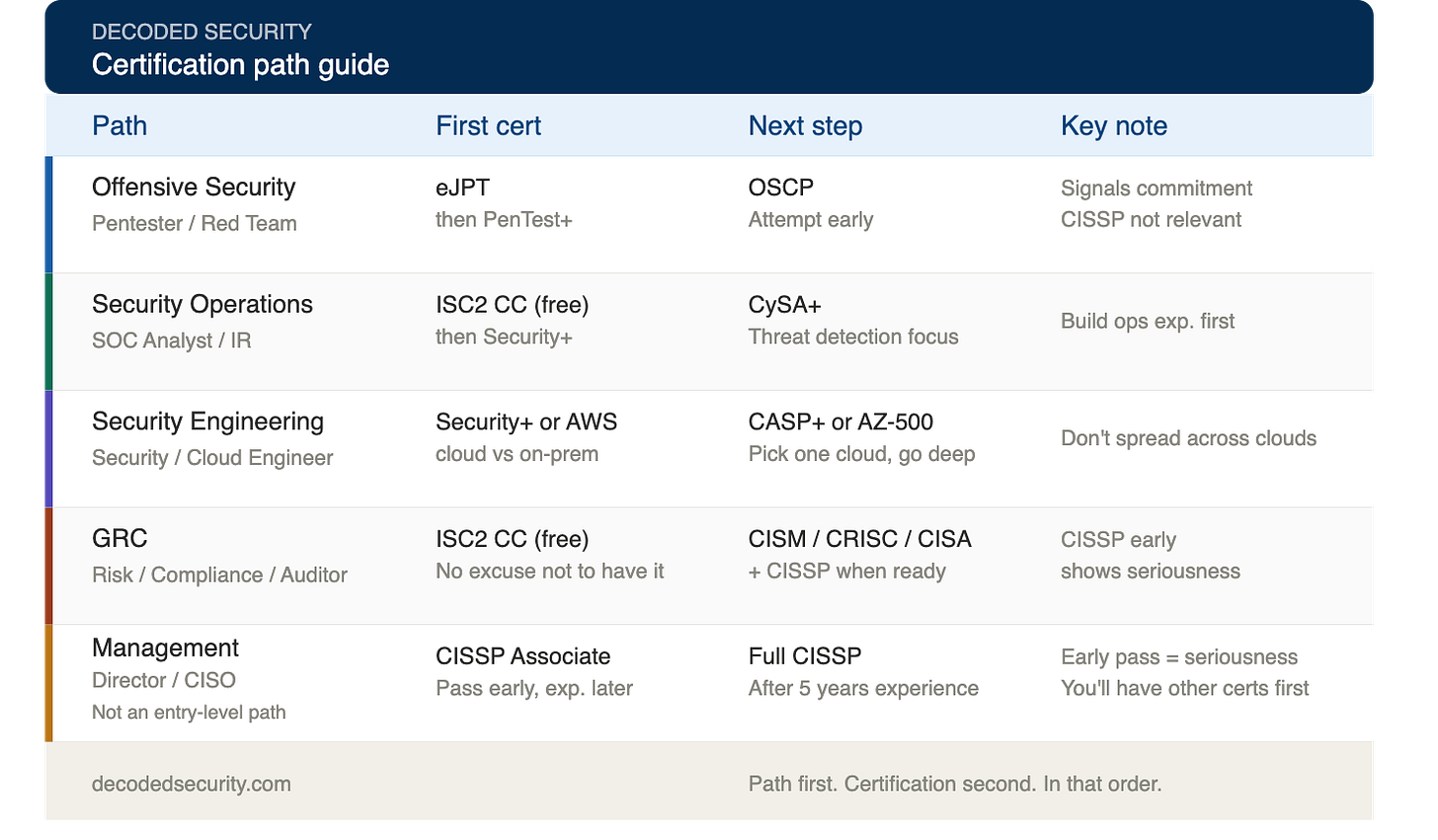
Most people pick certifications based on job postings, Reddit threads, or what looks impressive on LinkedIn. Here is a path-by-path guide to the only certifications that will actually move you forward
I have watched people spend €4,000 on CISSP prep and other materials before they had a single year of experience.
I have seen SOC analysts study for penetration testing certs because they looked impressive on LinkedIn.
I have spoken to GRC professionals who spent six months on Security+ when they didn’t need it for a single job they applied for.
None of them made a bad decision because they were careless. They made a bad decision because nobody told them the truth:
The certification doesn’t matter. The path does.
So, Path first. Certification second. In that order.
If you are not sure yet which of the five paths fits your background, go back and read the previous article first. Choosing the wrong path makes every certification decision harder.
Before we start - comment below using this format:
[Target role | Current level | Certifications you already have]
I will personally send you a customized study plan. Not generic advice. Something built for your specific situation.
I did this for 28 people last month. Every single one got a response.
Path 1: Offensive Security
Target roles: Penetration Tester, Red Team Engineer
This is the path most people romanticize and the one with the steepest entry requirements. Offensive security is not beginner-friendly. Anyone who tells you otherwise is selling you something.
Start here:
eJPT (eLearnSecurity Junior Penetration Tester) is the most realistic first cert for this path. It’s practical, affordable, and actually tests whether you can do the work - not just whether you memorized definitions. It teaches you to think like an attacker on real systems, which is the entire point.
After eJPT, CompTIA PenTest+ is a solid intermediate step that many employers recognize.
Then comes OSCP. The conventional advice is to wait until you have extensive hands-on experience. My take is different.
Attempting OSCP early - even before you feel ready - signals something no other cert on this path does: that you are serious enough to attempt the hardest practical exam in offensive security before you need to.
Passing it early separates you from the hundreds of people who say they want to be a pentester but never commit.
It will be harder without experience. But that difficulty is the point.
What to avoid: CISSP on this path is largely irrelevant until you move into management. Security+ is useful for foundational knowledge but won’t differentiate you for offensive roles.
Targeting offensive security? Comment below: [Target role | Current level | Certifications you already have] I'll tell you exactly what to focus on next.
Path 2: Security Operations (SOC)
Target roles: Security Analyst, Incident Responder
SOC is the most accessible entry point into cybersecurity for people without a deeply technical background. It’s also the path where Security+ actually earns its reputation.
Start here:
CompTIA Security+ is the right first cert for this path. It’s widely recognized, required or preferred in many SOC job postings, and covers the foundational knowledge you need to understand what you’re monitoring. It’s also DoD-approved, which matters if you’re targeting government or defense-adjacent roles.
After Security+, CompTIA CySA+ is the natural next step. It focuses on threat detection, behavioral analytics, and incident response - exactly what SOC analysts do day to day.
ISC2 CC is worth considering before Security+ if you want a free way to prove foundational knowledge while you prepare. It costs nothing to sit and covers the same core concepts.
What to avoid: Jumping to CISSP as a junior SOC analyst is putting the cart before the horse. Build your operational experience first.
On the SOC path? Drop your details below: [Target role | Current level | Certifications you already have] I’ll send you a personalized study plan.
Path 3: Security Architecture and Engineering
Target roles: Security Engineer, Cloud Security Engineer, Security Architect
This path splits depending on where you want to specialize - cloud or on-premise. Choose based on where the companies you want to work for actually operate.
If your target is cloud:
AWS Security Specialty or Microsoft SC-900 / AZ-500 are the right starting points, depending on which platform dominates your target market. Cloud security roles are growing fast, and cloud-specific certs signal something generic security certs don’t: That you understand the specific environment where most modern security work actually happens.
If your target is general engineering:
CompTIA Security+ gives you the baseline, then CompTIA CASP+ signals you can operate at a senior level.
For software developers moving into security engineering: look at the CSSLP (Certified Secure Software Lifecycle Professional). It’s underused and directly relevant to your background.
What to avoid: Don’t collect cloud certs across multiple providers before going deep on one. Pick AWS or Azure based on your target companies and commit.
Engineering or cloud security your direction? Comment below: [Target role | Current level | Certifications you already have] I’ll point you to the right next step.
Path 4: Governance, Risk, and Compliance (GRC)
Target roles: Security Auditor, Risk Manager, Compliance Specialist
This is the path I know best. And it’s the path where the certification advice you’ll find online is most consistently wrong.
Start here:
ISC2 CC is free to sit, covers the fundamentals you need, and is backed by the same organization that owns CISSP. For someone with no prior cybersecurity certification, this is your starting point. It costs nothing except study time.
After CC, the path splits based on your specialization:
Risk management: CRISC is the gold standard. Target it after your first GRC role.
Governance and management: CISM is the right target for mid-career.
Compliance and auditing: CISA is what auditors and compliance teams respect most.
CompTIA Security+ works here, too, for beginners who want to validate foundational cybersecurity literacy that GRC employers want to see.
What about CISSP on the GRC path?
Consider attempting it early - even before you feel fully ready. GRC is the path most directly aligned with how CISSP thinks.
The exam is built around risk management, governance, policy, and business decision-making.
That is exactly what GRC professionals do every day.
Passing the CISSP exam early signals that you think at a strategic level before you are even required to. Combined with CC and your first GRC role, it separates you from every other candidate who is still waiting until they feel ready.
What to avoid: Attempting CISSP before you have CC and a good understanding of the fundamentals. Build the foundation first. Then go for it.
On the GRC path? Drop your details below: [Target role | Current level | Certifications you already have] I'll build you a personalized study plan.
Path 5: Management and Leadership
Target roles: Security Program Manager, Security Director, CISO
One cert dominates this path: CISSP.
The conventional advice is to wait until you have five years of experience. My advice is different.
Consider passing it early anyway.
CISSP Associate means you’ve passed the exam before fulfilling the experience requirement. You have six years to complete it afterward.
When a hiring manager sees CISSP Associate on a resume from someone with two years of experience, they don’t think “this person jumped ahead.” They think “this person is serious.”
It won’t replace experience. But it will open doors that a generic technical cert never will.
What to focus on while you build that experience: understanding how security decisions connect to business goals. The exam tests judgment, not just knowledge. Study accordingly.
Thinking about the management path? Comment below: [Target role | Current level | Certifications you already have] I’ll tell you if your timing makes sense and what to focus on first.
The honest truth about certifications
A certification will not get you hired on its own.
It opens the door. You still have to walk through it.
What actually gets you hired is showing up to interviews knowing how to think, not just what to memorize. It’s having a resume that tells a coherent story. It’s being able to explain your reasoning clearly when a hiring manager puts a scenario in front of you.
The right certification for your path removes one barrier. It proves you took it seriously enough to invest time and money into a credential that matters for the direction you chose.
That’s it. One barrier removed.
The rest is on you.
Pick your path. Pick your cert. Start this week.
The Certification Tells You What to Study. The Blueprint Tells You What to Do.
Knowing which certification fits your path is only half the answer.
The other half is knowing what to actually do in the next 90 days. Which skills to build first. How to position your background for cybersecurity roles. How to build a resume that gets read. How to walk into interviews and explain your thinking clearly.
That’s what the 90-Day Cybersecurity Job Blueprint covers.
4.8 stars. 45 people have used it. 14-day money-back guarantee.
💬 Comment below with your details, and I'll tell you if you're on the right track: [Target role | Current level | Certifications you already have]