Diffie-Hellman Explained Like You’re 12 (And Why Interviewers Love Asking About It)
“How do two strangers create a secret… without ever sharing the secret?” That question confused cryptographers for centuries. Today, the answer protects almost everything you do online.
One of the most common cybersecurity interview questions, especially for entry-level roles, is:
“Can you explain Diffie-Hellman?”
It also appears in major certifications like CC (Certified in Cybersecurity) and CISSP.
Not because you need to calculate the math…
…but because it tests whether you understand a core security concept: secure key exchange over an insecure channel.
And there is a good reason for that!
Note: If this article helped you understand Diffie-Hellman, drop a like so more people can find it too. Thank you!
What problem does it solve?
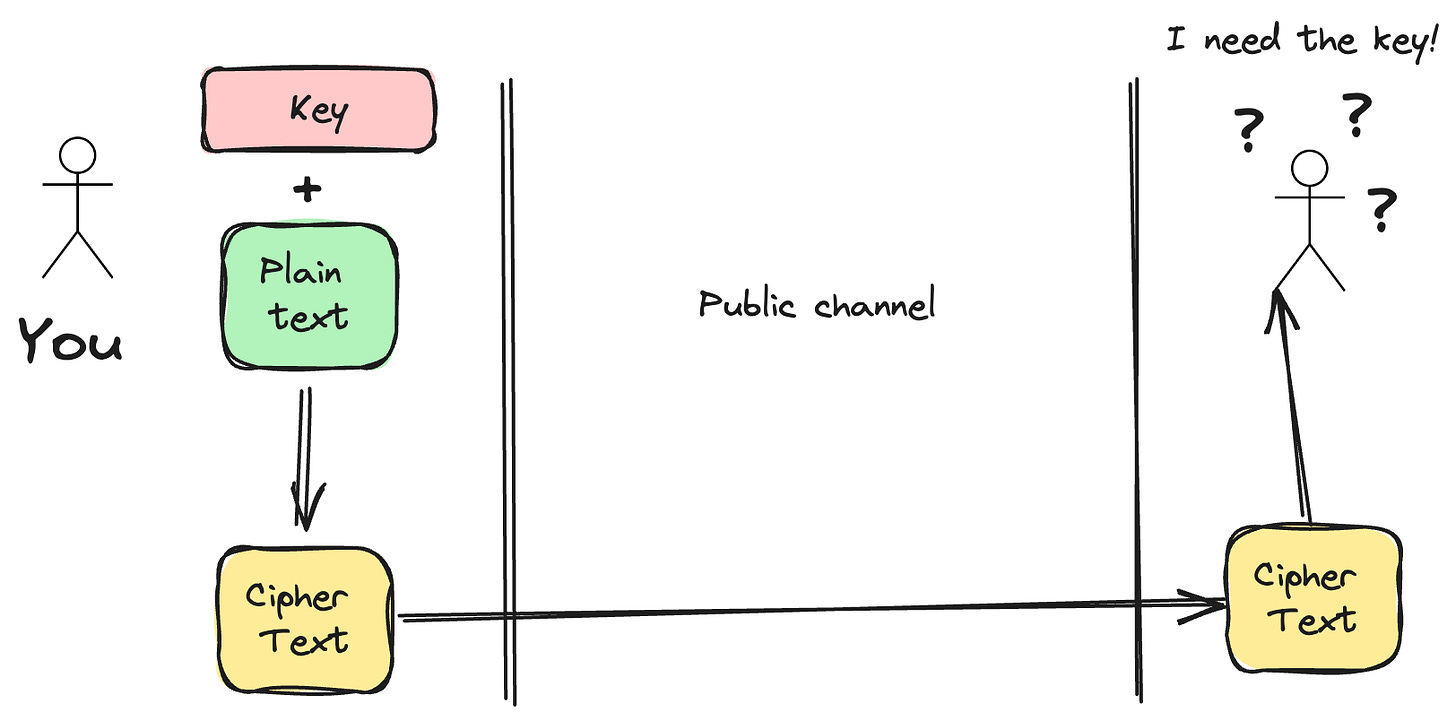
Imagine you want to send a secret message to someone.
So, you generate a key and use a secure algorithm to encrypt your message.
Great!
But there’s a problem.
How do you share the key with the other party?
They need to decrypt the message somehow, and everyone can see your communication channel.
Hackers. Governments. Your ISP. Anyone.
So how do you create a shared secret without ever meeting in person, and without anyone else discovering it?
Warning: If you’re not sure how symmetric encryption works. I got you covered!
Symmetric vs Asymmetric Encryption: What’s the Difference?
The solution is called Diffie-Hellman key exchange.
And today, it protects almost everything you do online.
Are you preparing for any cybersecurity certification exam? Let us know in the comments!
What Is the Purpose?
The purpose of Diffie-Hellman is simple:
Create a shared secret between two parties without transmitting the secret itself.
(REMEMBER THIS)
That shared secret can then be used for:
Encryption keys (TLS / HTTPS)
VPN tunnels
Secure messaging
Authentication protocols
Important: Diffie-Hellman does not encrypt data itself.
It only creates the secret key.
Encryption algorithms (like AES) use that key afterward.
Okay, now that you know the purpose, let’s take a look at how it works!
Principle: The Colored Water Example
I will explain this algorithm without using complicated mathematical formulas. That isn’t the point here. So instead of a discrete logarithm problem, I am going to use colors!
Let’s imagine the following scenario:
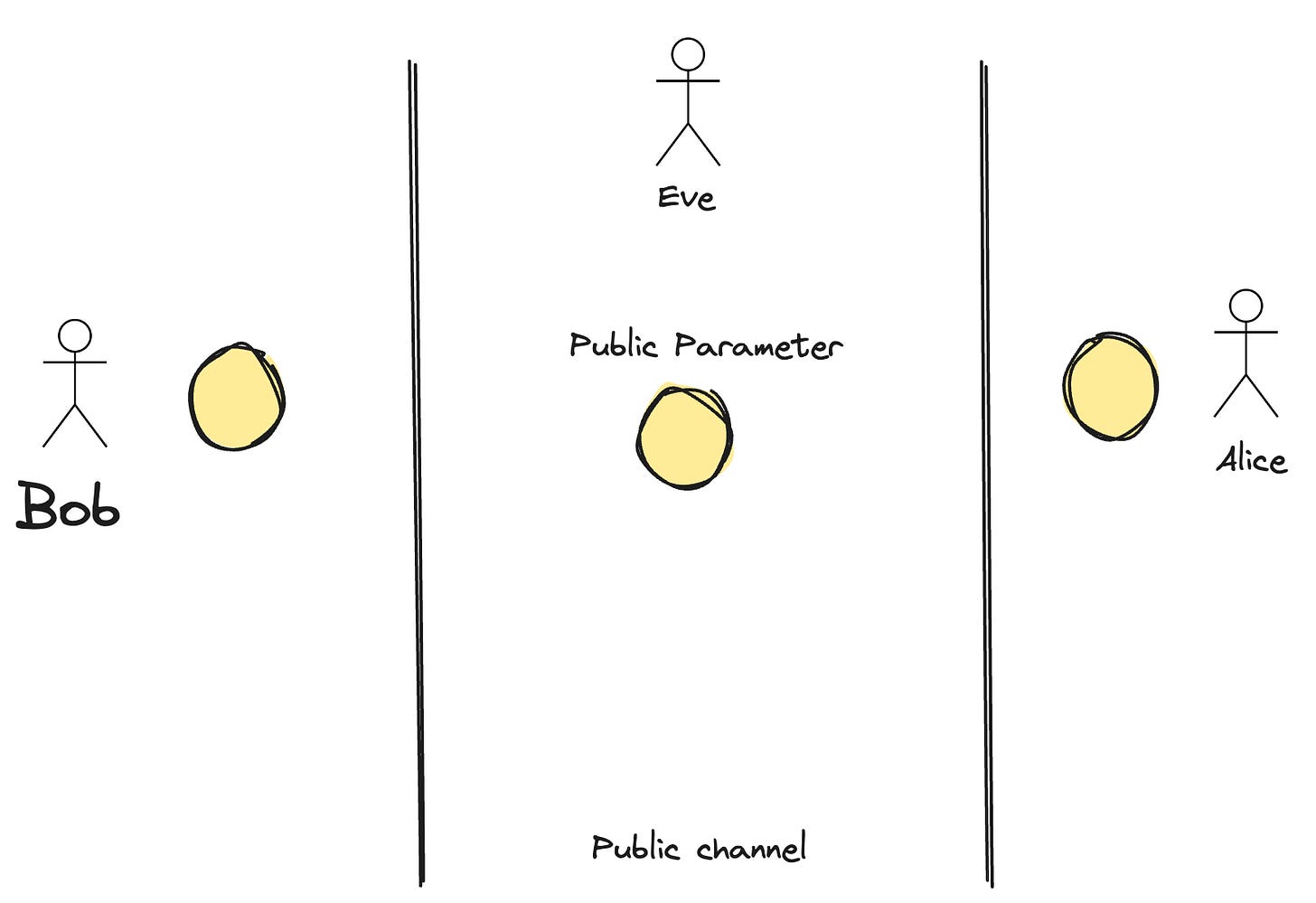
You have two people who want to communicate securely: Alice and Bob.
They want to create a secret color mixture (shared secret).
But an attacker (Eve) is watching everything on the public channel.
So what should they do?
Do you find this analogy convenient? Let me know in the comments!
Step 1: Alice and Bob should agree on public parameters
In our example, this could be the color yellow.
This is called a public parameter.
Everyone can see it:
Alice sees it
Bob sees it
Eve (the attacker) also sees it
And that’s completely fine.
There is no secrecy yet.
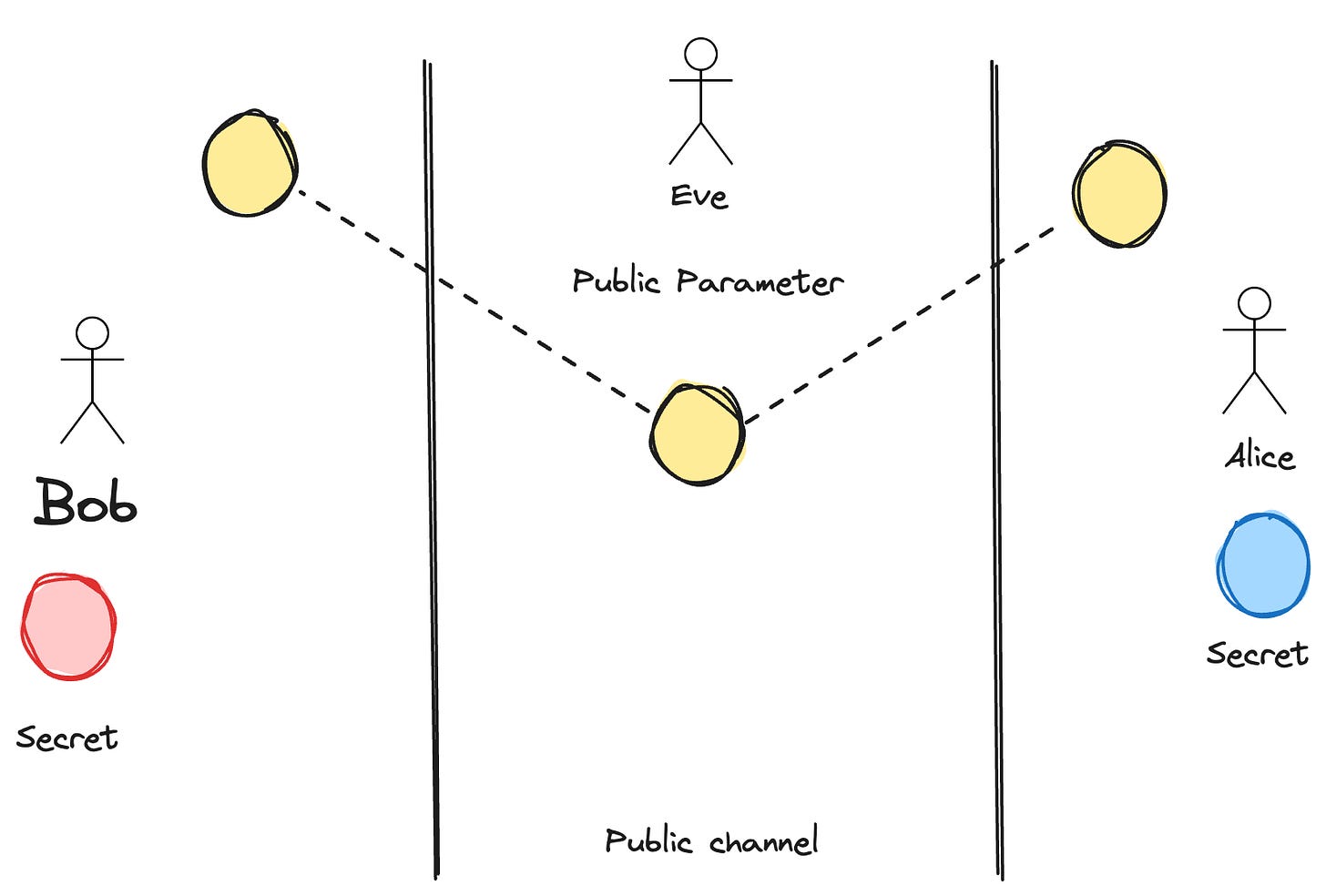
Step 2: Private Secret Colors
Now it gets interesting. Both Alice and Bob choose a secret private color that they don’t share with anyone.
Let’s say that Alice chooses blue and Bob chooses red.
Once they have their own secret color, take a glass of yellow water (public) and add their secret-colored water to the glass.
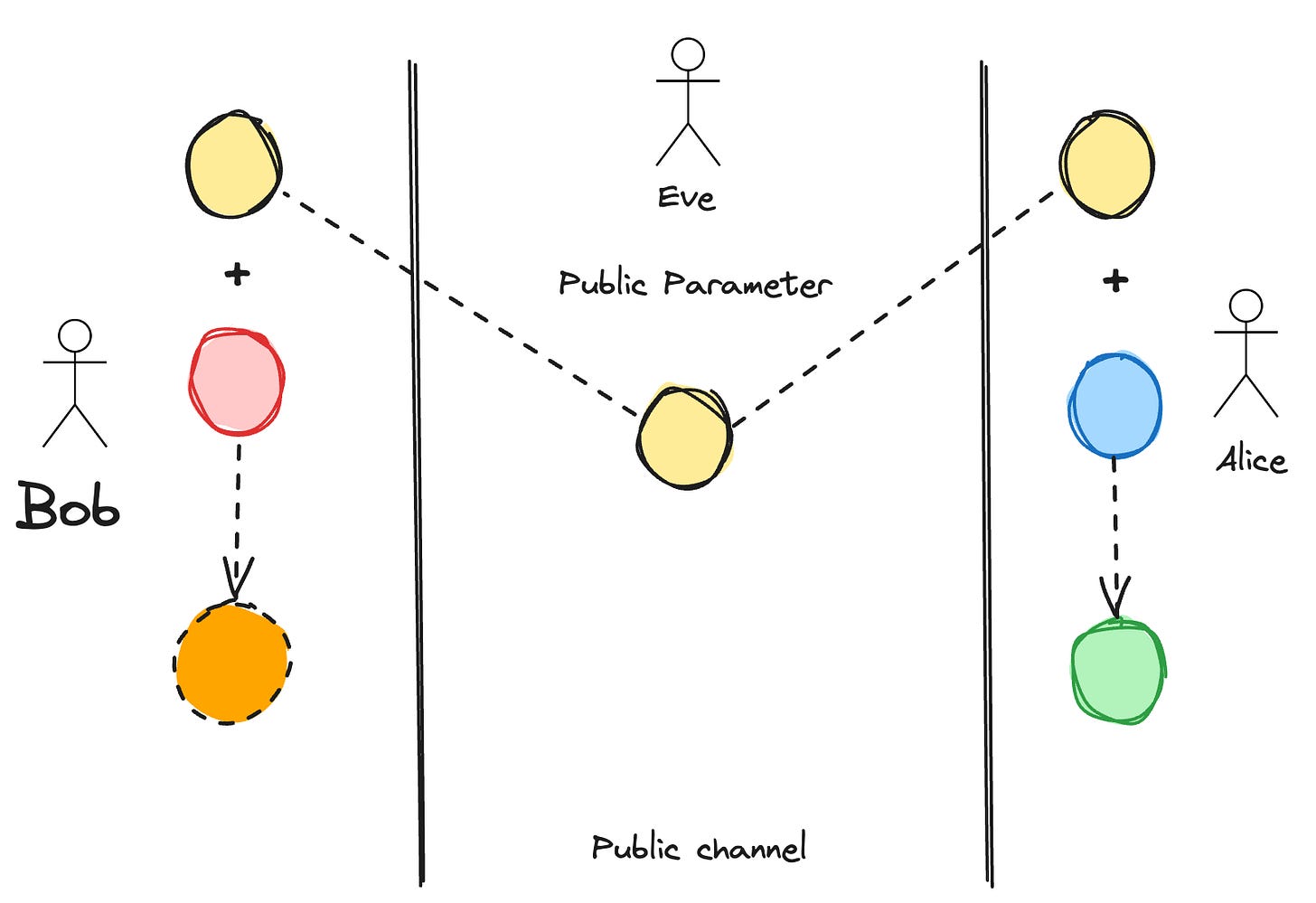
Step 3: Exchange the Mixed Colors
They exchange their mixtures publicly again.
So now:
Alice receives Bob’s mixture
Bob receives Alice’s mixture
Eve still sees everything. She has both Bob’s mixture and Alice’s mixture. But it is impossible for her to separate the two individual colors from the mix.
So the information is useless for her.
Step 4: Final Secret
Now, both add their own secret color again.
Both end up with the same final color.
But Eve cannot reproduce it.
And that’s it! Bot and Alice now have their shared secret and can easily communicate securely!
If this article helped you understand the concept of the Diffie-Hellman algorithm, drop a like and help more people understand it!
Conclusion
If you’re reading this, congratulations.
Understanding Diffie-Hellman is a huge step forward and absolutely crucial for certification exams such as CC, Security+, or CISSP.
More importantly, it means you’re beginning to understand how secure communication actually starts, and that’s one of the foundations of cybersecurity.
I know cryptography can feel intimidating at first, so here are the key takeaways I want you to remember:
You don’t need to understand the math. Focus on the concept first.
Diffie-Hellman is about creating a shared secret over an insecure channel.
It does not encrypt data, it creates the key that encryption uses later.
Public parameters can be visible to everyone. Security comes from private values.
Modern protocols like TLS, VPNs, and secure messaging use Diffie-Hellman (or its variants) in the handshake phase.
If you understand this principle, you’re already ahead of many beginners, and you’ll recognize one of the most common cybersecurity interview questions instantly.
Keep going.
Let’s connect
If you want to collaborate, discuss, or just geek out over virtualization and cloud security, reach out to me:
Email: erich.winkler@decodedsecurity.com
LinkedIn: Erich Winkler
Gumroad community: Decoded Security
Enjoyed this article? Like it or drop a comment. I’d love to hear your thoughts and questions!
Let’s learn and grow together!