Symmetric vs Asymmetric Encryption: What's the Difference?
Hello everyone,
Let’s follow up on a previous article about encryption basics and look deeper at two main encryption types: asymmetric and symmetric.
Let’s take a look at each of them!
🔁 Symmetric Encryption
One key is used to encrypt and decrypt data.
Both the sender and receiver use the same secret key.
Fast and efficient — but secure key exchange is usually problematic.
📦 Example:
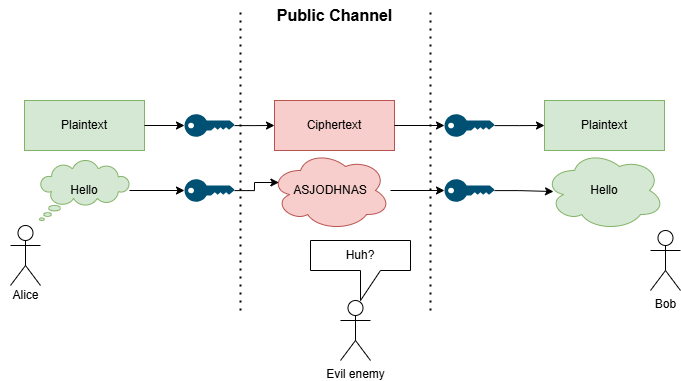
Alice wants to send a message to Bob
But Alice doesn’t want her evil enemy to see the content of the message.
Alice encrypts the message and shares the key with Bob so only he can decrypt it.
🕵️♂️ The evil enemy tries to read the message — but all he sees is gibberish.
The issue is to securely share the key with Bob
But what if we want to avoid the problem of sharing a secret key altogether?
That’s where asymmetric encryption comes in.
🔐 Asymmetric Encryption
This solution completely avoids the key exchange by using a key pair - one key that’s meant to be public and one always private - securely stored and never shared.
Here is what you need to know:
It uses a pair of keys: a public key and a private key
It solves the key exchange problem — you don’t need to share anything securely
Anyone can encrypt the message using the public key, but only the private key can decrypt it.
Way slower than symmetric encryption - It isn’t convenient for everything, despite its benefits.
Example:
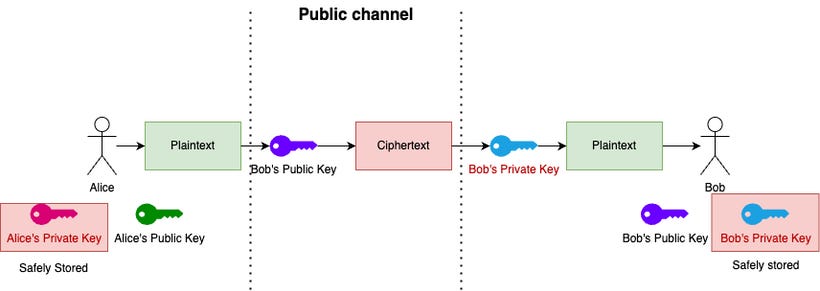
Alice wants to send a secret message to Bob.
She encrypts it using Bob’s public key, which anyone can access.
Only Bob, who holds the matching private key, can decrypt the message.
No one can decrypt it without a private key.
✅ Conclusion
Both symmetric and asymmetric encryption have their benefits.
Symmetric encryption is fast and efficient, perfect for encrypting large amounts of data.
Asymmetric encryption solves the key-sharing problem and adds extra layers of security, especially for identity verification and secure communication.
In practice, these two are often used together. For example, asymmetric encryption is used to securely exchange a symmetric key — and then symmetric encryption takes over to handle the actual data transfer.
👉 What’s next?
Now that you understand the main difference between symmetric and asymmetric encryption, the next step is to take a look at Hashing.
📩 Subscribe to my Patreon for free so you won’t miss the next posts — especially if you’re just starting your journey into cybersecurity!


I try to imagine the size of a prime number that is 2048 bits think about a computers processing , poor thing no wonder we only use asymetric for key exchange. The other thing I was told years is how much it bloats a tcp packet, it can almost clog a network.
I remember learning about Diffie-Hellman from Computerphile on YouTube : D