3 Things You Need To Know For Your First Cybersecurity Interview
Breaking into cybersecurity? These three concepts show up in interviews again and again. Master them, understand how hiring managers think, and avoid the mistakes that end interviews early.
Struggling to figure out what actually matters for a cybersecurity interview?
Here’s a hard truth from the hiring side:
You don’t fail interviews because you don’t know enough.
You fail because you focus on the wrong things.
I can’t teach you everything in one post, but I can give you three topics that come up again and again in real interviews.
Knowing the rules won’t get you the job.
Not knowing them will almost certainly cost you the interview.
That’s why this article focuses on what interviewers expect you to understand
📘 Essential also for anyone preparing for the ISC2 CC exam.
Are you searching for a job in cybersecurity? Let me know in the comments, and let’s connect!
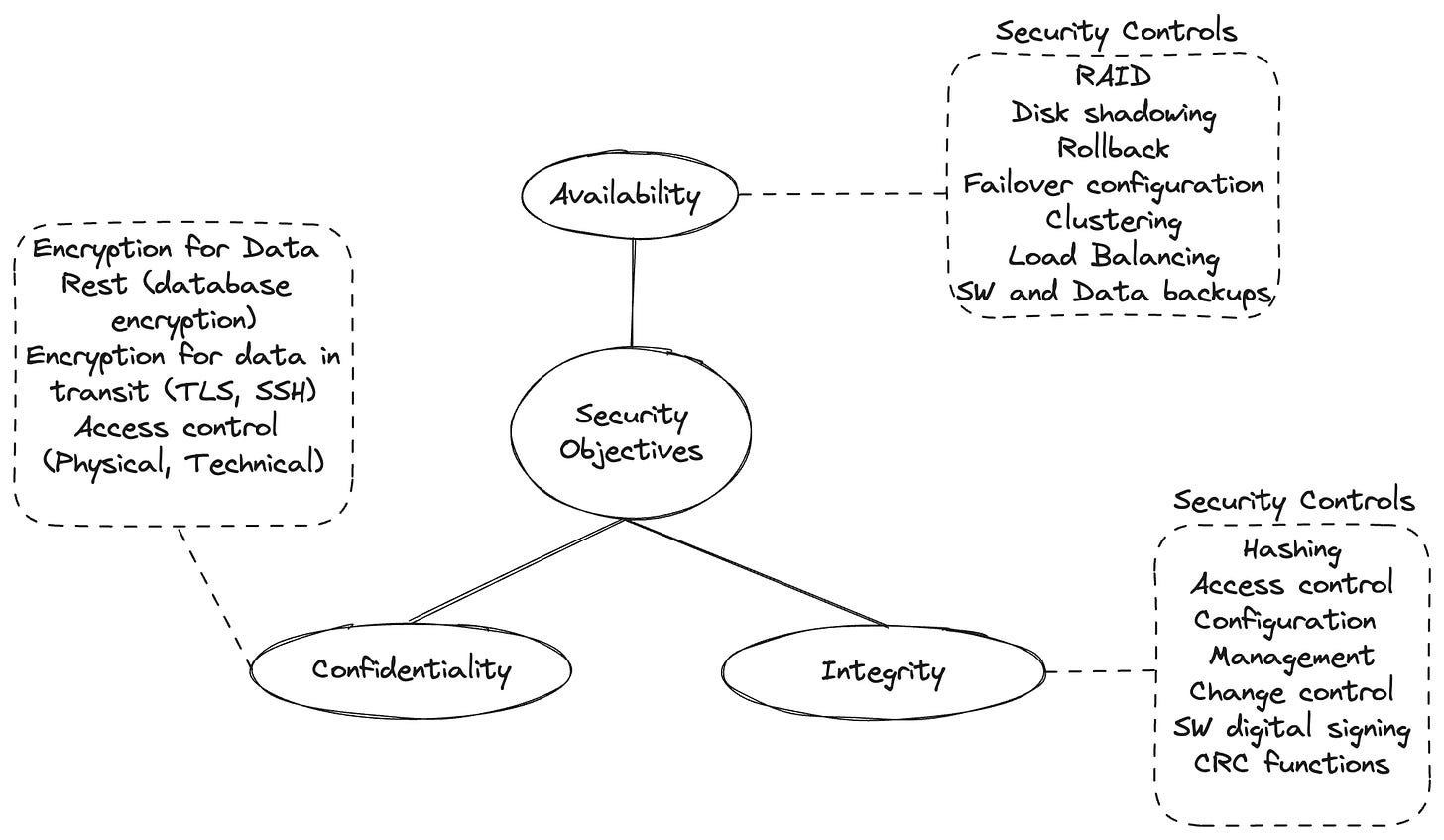
1. The CIA Triad
“What are the core security objectives in any system?”
3 letters, crucial concept.
The CIA Triad defines the three core objectives of information security:
Confidentiality – making sure information is only accessible to those who are authorized.
Integrity – ensuring that data hasn’t been tampered with or altered without permission.
Availability – making sure systems and data are accessible when needed.
Why does it matter so much?
Protecting information systems means ensuring the CIA (Confidentiality, Integrity, Availability) of all assets in our information systems.
Every control, every procedure should exist in order to support one of the core objectives.
The good news is, the concept is quite easy, and all you need is one picture!
However, if you’d like to know more about it, make sure to check one of my previous articles: CIA Triad - Introduction.
There is no quicker way to learn then connecting with people who are already where you want to be!
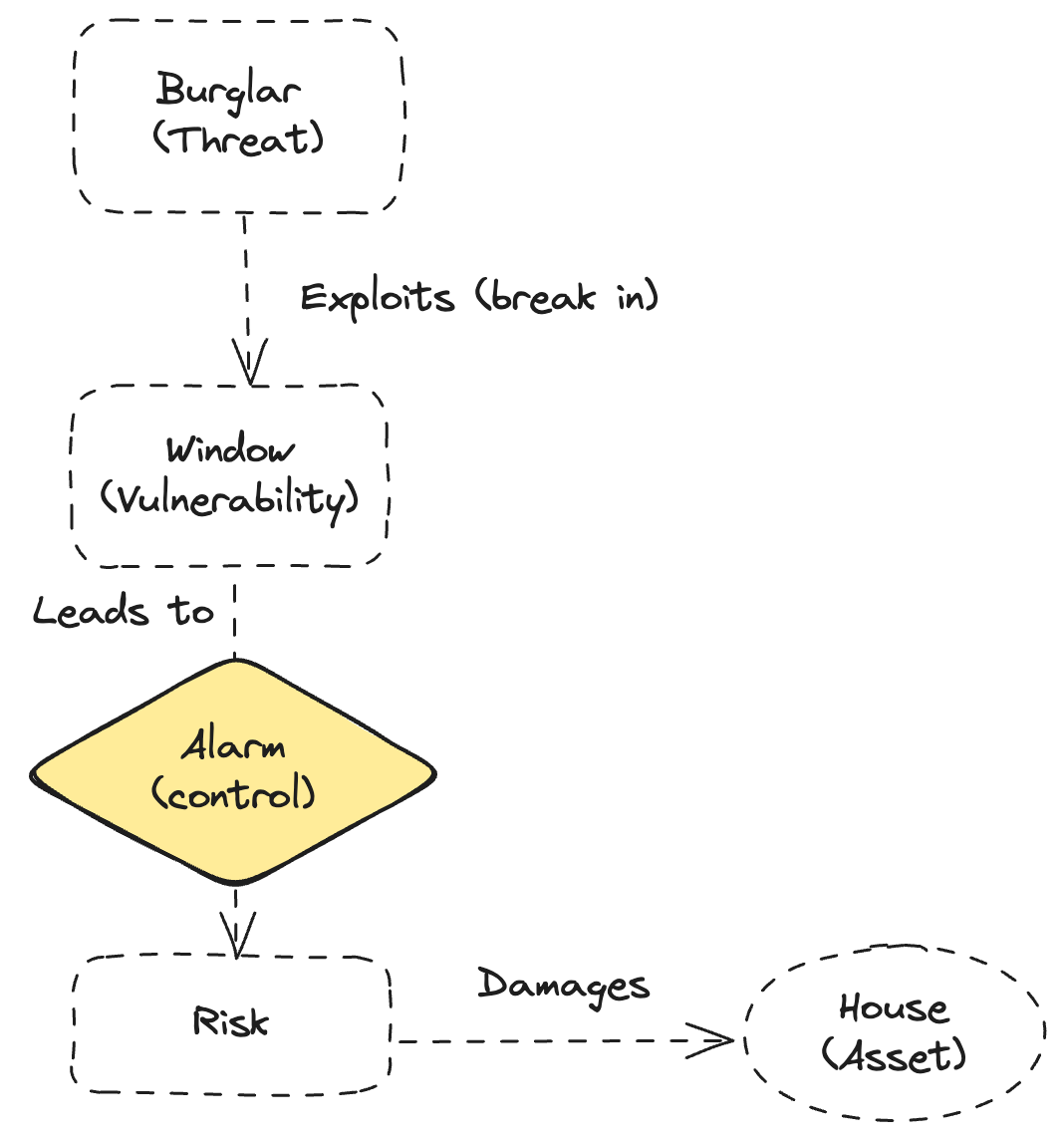
Threat ≠ Risk ≠ Vulnerability
“Could you please explain the difference between Threat, Risk and Vulnerability to me?”
I hear people use these terms interchangibly all the time.
In reality, there is a huge difference. And knowing this difference shows that you are aware how risk management works.
Let me give you a definition of each term:
A threat is any potential danger that is associated with the exploitation of a vulnerability.
A vulnerability is a weakness in a system that allows a threat source to compromise its security.
A risk is the likelihood of a threat source exploiting a vulnerability and the corresponding business impact.
Still confused about the difference?
Let me show the relationship between the terms in one simple example.
Imagine a house with a broken window (vulnerability). There’s a burglar in the neighborhood (threat). The risk is that the burglar might notice the window and break in.
Now, installing a camera or alarm system won’t stop the burglar from existing. It won’t fix the window either. But it might discourage the burglar or notify you quickly if something goes wrong.
That’s it! All you need is one very simple example, and you already look like a pro!
If you’re interested in more details about this topic, I recommend reading one of my previous articles: Threat ≠ Risk ≠ Vulnerability.
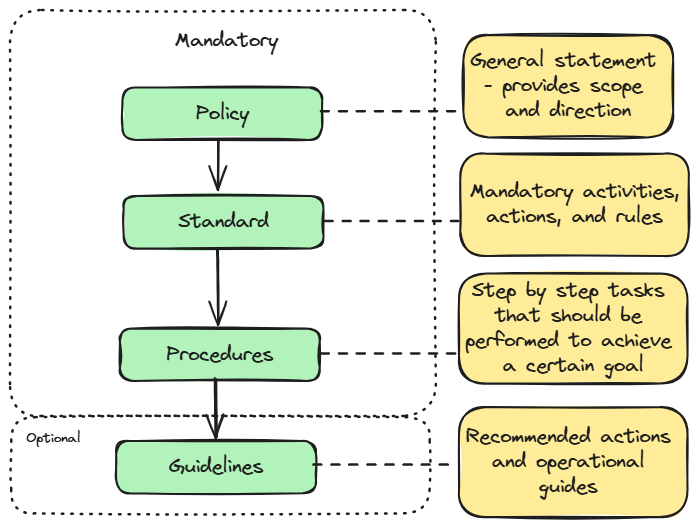
Security Policies, Standards, and Procedures
This might sound boring to you, especially if you’re a technically oriented person, but like it or not, even as a cybersecurity specialist, you are still part of an organization, and you need to understand the bigger picture of what you are doing.
That’s why hiring managers often want to make sure you are willing to learn the basics of cybersecurity governance.
Again, let me give you definitions first:
Policy:
A high-level statement that defines what must be done and why. It reflects management’s intent and direction.
Standard:
A mandatory rule that defines what exactly must be used or followed — tools, technologies, or configurations.
Procedure:
A detailed set of steps that explain how to implement a policy or standard in practice.
Guideline:
An optional recommendation or best practice. They help us to cover the grey areas and provide the necessary flexibility.
It didn’t hurt that bad, did it?
The whole concept is actually pretty easy, and I will give you one simple picture that will help you to remember it.
Make sure you can understand the difference and prepare real-world examples of each.
Not sure where to start? Well, I got you covered again.
If you want a practical scenario + quiz, read: Security Policies, Standards, and Procedures: The Boring Stuff That Actually Saves You.
You can find a real world scenario there and a quiz that will help you determine if you’re ready for the interview!
Conclusion
If you’re reading this, congratulations! You just made another step on your cybersecurity journey!
Of course, simply knowing these topics isn’t enough to land a job in the field, but it is a great start!
I know interviews are stressful, but from my experience, knowing what to focus on not only increases your chances of getting hired but also gives you more confidence.
And confidence is often the key ingredient in the mix!
And if you want a complete guide on how to prepare for your first interview and land a job in cybersecurity I got you covered again: The 90-Day Cybersecurity Job Blueprint.
Thank you for reading Decoded Security, and I am looking forward to your comments!
Let’s connect
If you want to collaborate, discuss, or just geek out over virtualization and cloud security, reach out to me:
Email: erich.winkler@decodedsecurity.com
LinkedIn: Erich Winkler
Enjoyed this article? Like it or drop a comment. I’d love to hear your thoughts and questions!
Let’s learn and grow together!
Ready to level up your cybersecurity skills?
💬Comment below and tell me what your experience with SLAs is
❓Take the quiz to test your understanding: CybersecErich: Quiz Hub
📰Subscribe (free or paid) to get new posts straight to your inbox.
Share this with a friend studying for CISSP, or anyone curious about cybersecurity



This was very helpful, thank you! The CIA Triad and the threat–risk–vulnerability explanation finally clicked for me. Interview prep can feel overwhelming, and this post makes it much clearer what to focus on.