Why We Need to Be Lawyers: Intellectual Property & Compliance in Cybersecurity
Think cybersecurity is just about tech? Think again. To truly protect your organization, you need a lawyer’s mindset too. Understanding intellectual property, licensing, and legal risks is essential.
I think it’s time to show you why cybersecurity isn’t just about setting up firewalls.
While preparing for my CISSP, I reached chapters that have nothing to do with access controls or guarding physical assets and everything to do with compliance and protecting something far more fragile: intellectual property (IP).
Here’s how we’ll approach it:
We’ll start with the “boring” part, the definitions. Without them, nothing else really makes sense.
Then we’ll look at how organizations can get into trouble here, and the risks that come with it.
Finally, we’ll sum it all up and finish with a quick quiz to see if it all clicks.
Sounds good?
Let’s roll
What Is Intellectual Property?
To be honest, this whole topic revolves around one crucial term — intellectual property.
So, what is it? And what’s so special about it?
Intellectual property (IP) is a type of property created by human intellect. It includes ideas, inventions, and expressions that are uniquely created and can be legally protected from unauthorised use by others.
Now we know what we’re protecting — that’s a good start.
But you might still have one big question: Who decides what counts as “unauthorised use”?
Is it the government? The law? The person who created the IP?
Let’s find out in the next section.
Licensing and IP laws
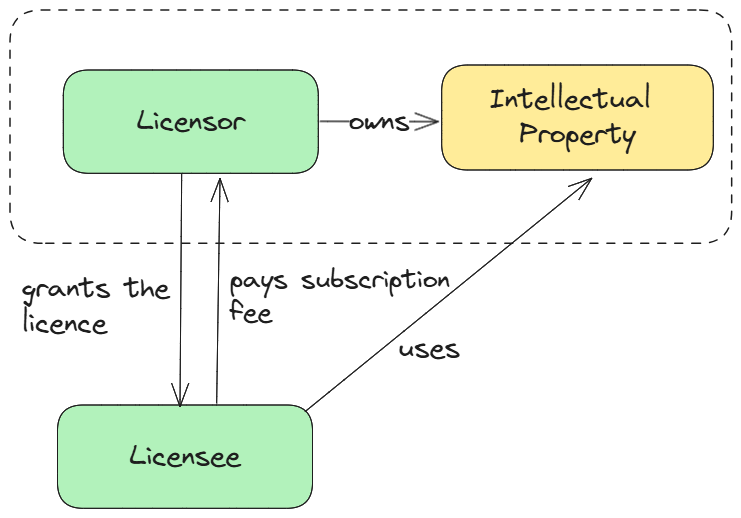
The answer is, of course, the owner of the IP. And how is it implemented?
By granting licenses.
A license is nothing else than an agreement between the IP owner and somebody else, granting that party the right to use the IP under specified conditions.
If those conditions are broken, it’s considered unauthorised use, and that’s where legal action comes in.
But here’s the catch: not all IP is protected the same way. The laws and licensing rules depend on what kind of IP we’re talking about.
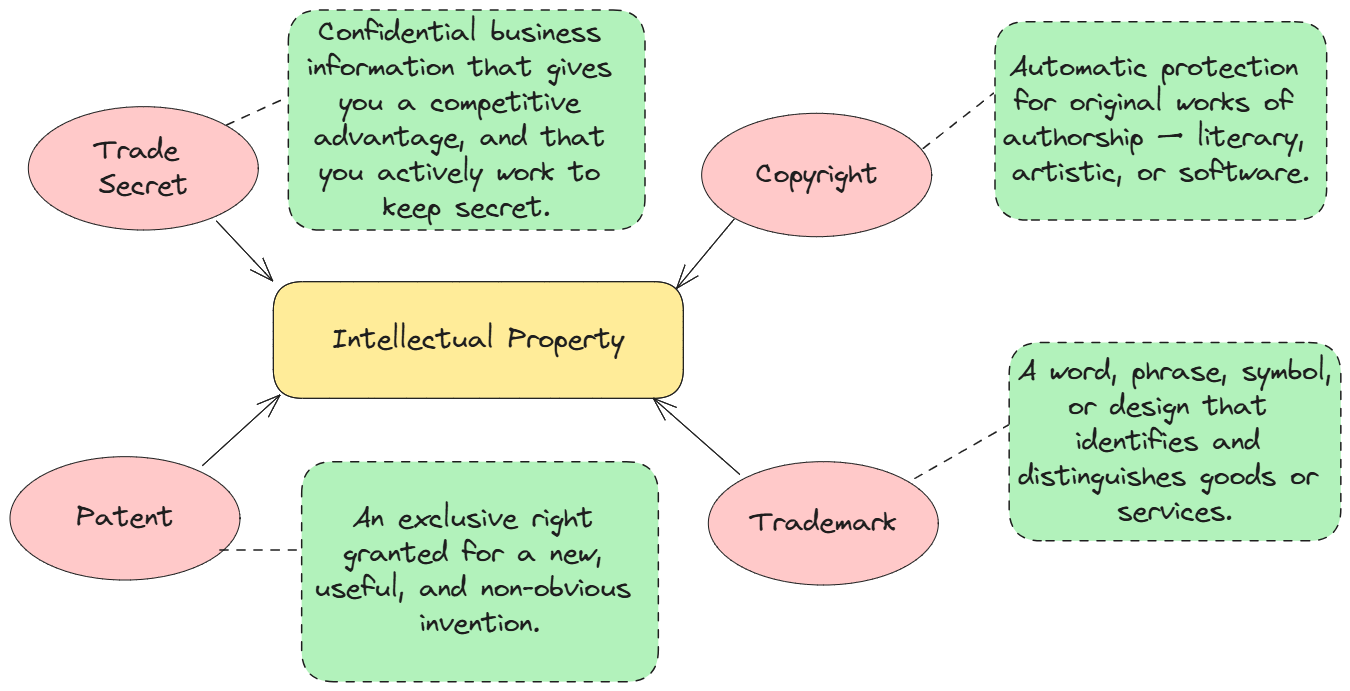
In cybersecurity (and in the CISSP exam), you need to know the four main categories:
Trade Secret
A trade secret is valuable business information that gains its advantage from being kept confidential, and it only stays protected as long as it remains a secret.
Examples: Coca-Cola’s recipe, Google’s search algorithm, a confidential client list, your company’s internal product roadmap.
Security angle: If it’s leaked, the legal protection is gone forever. That’s why measures like encryption, access control, NDAs, and insider threat programs are critical.
Organizational best practice: Enforce strong access controls, require NDAs, and regularly train employees on safeguarding confidential information.
Copyright ©
Copyright automatically protects original works of authorship, creative expressions fixed in a tangible form. It covers the expression of an idea, not the idea itself.
Examples: A novel, a painting, a piece of music, your company’s proprietary software source code, training videos.
Duration: Protection typically lasts for the life of the creator plus 70 years (in most jurisdictions).
Security angle: Mishandling licensed software, violating open-source licenses, or allowing piracy can lead to lawsuits and loss of reputation.
Organizational best practice: Use license management tools, conduct regular code audits, and ensure compliance with all software and content licenses.
Trademark
A trademark is a word, phrase, symbol, or design that identifies the source of goods or services and distinguishes them from others. It represents brand identity.
Examples: Apple logo, Nike’s swoosh, “Just Do It” slogan, the shape of a Coca-Cola bottle.
Security angle: Cybercriminals often abuse trademarks in phishing campaigns, counterfeit websites, or fake apps to trick customers. Brand monitoring tools and takedown processes help fight this.
Organizational best practice: Continuously monitor brand use online and respond quickly to abuses or impersonations.
Patent
A patent is an exclusive right granted for an invention that is new, useful, and non-obvious. It protects the invention itself, not just its expression.
Examples: A new type of encryption algorithm, a unique piece of security hardware, a chemical formula for a new drug.
Security angle: If details of a patentable invention are leaked before filing, patent rights can be lost. Preventing pre-disclosure through strong information security is essential.
Organizational best practice: Secure R&D data with strict access controls and limit disclosure until patents are properly filed.
Using Others’ Intellectual Property
Don’t forget it isn’t just about protecting your IP. Using someone else’s intellectual property without proper permission can cause serious legal and security problems.
Unlicensed software, patented technology, or trademarked material used without a valid license can lead to hefty fines, lawsuits, and damaged reputation.
To stay safe, organizations must maintain clear license management, ensure open-source compliance, and carefully monitor vendor security practices.
But we will focus on all that some other time.
Key Takeaways
I started this newsletter to help people understand what cybersecurity is all about and to create study materials for certification exams such as CISSP.
So maybe I should stop making it so hard for you to decode what’s crucial about each topic and sum it all up for you.
So here is what I think you should know after reading this article:
Cybersecurity is about much more than firewalls, protecting intellectual property (IP), and knowing the IP/compliance laws is part of the job.
Intellectual property includes four main types: trade secrets, copyrights, trademarks, and patents - each with different protections and risks.
Trade secrets must be kept confidential at all times; once leaked, protection is lost forever.
Copyright © protects creative works for the life of the creator plus 70 years (typically).
Patents protect inventions but can be invalidated if information is leaked before filing, making strong security essential during R&D.
Using others’ IP without permission carries serious legal and security risks. Any organization must manage licenses, ensure open-source compliance, and monitor vendors carefully.
Don’t expect to pass the CISSP certification exam without understanding the IP laws
Conclusion
Nobody expects you to be a lawyer, but understanding how intellectual property works is part of the job. You need to anticipate all the risks your organization faces, and if a lawsuit hits because of poor license management, guess who takes the blame.
To make sure that doesn’t happen, let’s see how well you understand these topics. Take the quiz below and share your score in the comments!
Did you take the quiz yet?
Circle back to the top and see how many questions you nailed. If you scored 8/10 or more, you're on solid ground.
And if you didn’t, now you know exactly what to review.


What a fantastic CISSP review material. This is one I had literal flash cards for!
Great stuff as always. ✅
I like this article. I was seeing a post that claimed a software dev idea for an education management system was used and the dev didn't get anything in return . The 'robber ' is a Kenyan gov't ministry