What are the things that keep our networks alive?
Good network security starts with understanding the devices behind it from repeaters to multilayer switches, routers, gateways, and proxies. Let’s take a closer look!
This probably won’t be the most entertaining article you’ve ever read. So why am I writing it?
The reason is actually very simple.
If someone wants to understand complex security topics, it can’t be done without understanding the basic terms.
And even then I know it isn’t fun to go through definitions and basics, I’ll try to make it fun, alright?
Shall we?
Network security is one of the biggest pillars of organizational security, and of the CISSP exam.
But before we get into firewalls, intrusion detection, and all the advanced controls, we need to zoom out and look at something simpler: the devices that make a network possible in the first place.
Every packet of data, every protocol, every service runs on top of physical devices that connect our computers together.
Routers, switches, firewalls, these are not just “boxes with blinking lights.” They’re the core of the digital world.
And here’s the catch: you can’t really understand the security controls if you don’t first understand the devices themselves.
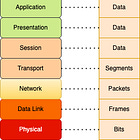
The crucial framework here is the OSI model.
I’ve covered it in a previous post, so if it’s not fresh in your mind, I’d recommend pausing here and reading that first. Because everything in network security builds on it.
Network devices
Repeaters
A repeater is the simplest of all network devices.
It operates at the Physical layer, meaning it doesn’t understand addresses, packets, or frames. Its only job is to take a weak electrical/optical signal and regenerate it, so the data can travel further..
No filtering, no traffic decisions, no awareness of what’s being transmitted.
Today, mostly replaced by more advanced devices like switches and wireless extenders.
Security relevance: minimal
Bridges
A bridge connects two network segments and makes forwarding decisions based on MAC addresses at the Data Link layer (Layer 2). It learns where devices are located by examining source MAC addresses and builds a forwarding table.
If the destination MAC is known, the frame is sent only to the right segment, if unknown, it’s flooded. This reduces traffic compared to hubs but still keeps all devices in the same broadcast domain.
Weaknesses:
Vulnerable to MAC flooding attacks.
Susceptible to broadcast storms if loops exist, since broadcasts can circulate endlessly. This led to the creation of the Spanning Tree Protocol (STP).
Bridges are mostly obsolete today, but their legacy lives on in switches, which are essentially multi-port bridges with more intelligence.
Switches
A switch is essentially a multi-port bridge that forwards frames based on MAC addresses at the Data Link layer (Layer 2). Unlike hubs, each port on a switch has its own collision domain, which greatly improves efficiency.
Modern switches often support:
VLANs for logical segmentation.
Port security to limit devices per port.
Layer 3 switching, adding limited routing functions.
Weaknesses:
Vulnerable to MAC flooding
Can suffer from broadcast storms in networks with loops, which is why Spanning Tree Protocol (STP) is critical.
Prone to VLAN hopping attacks if misconfigured.
Here is the catch with switches. There are no longer just layer devices. Modern switches can do much more that that!
Layer 3 Switches (Multilayer Switches):
Operate at Network layer (Layer 3) in addition to Layer 2.
Can route traffic between VLANs internally, reducing the need for a separate router.
Forward packets based on IP addresses, but much faster than traditional routers.
Useful for large LANs where inter-VLAN routing is frequent.
Layer 4 Switches:
Operate at Transport layer (Layer 4).
Can make forwarding decisions based on TCP/UDP port numbers, not just IP.
Often used for load balancing and directing traffic to different servers based on application type.
Adds basic application-level intelligence without full application inspection.
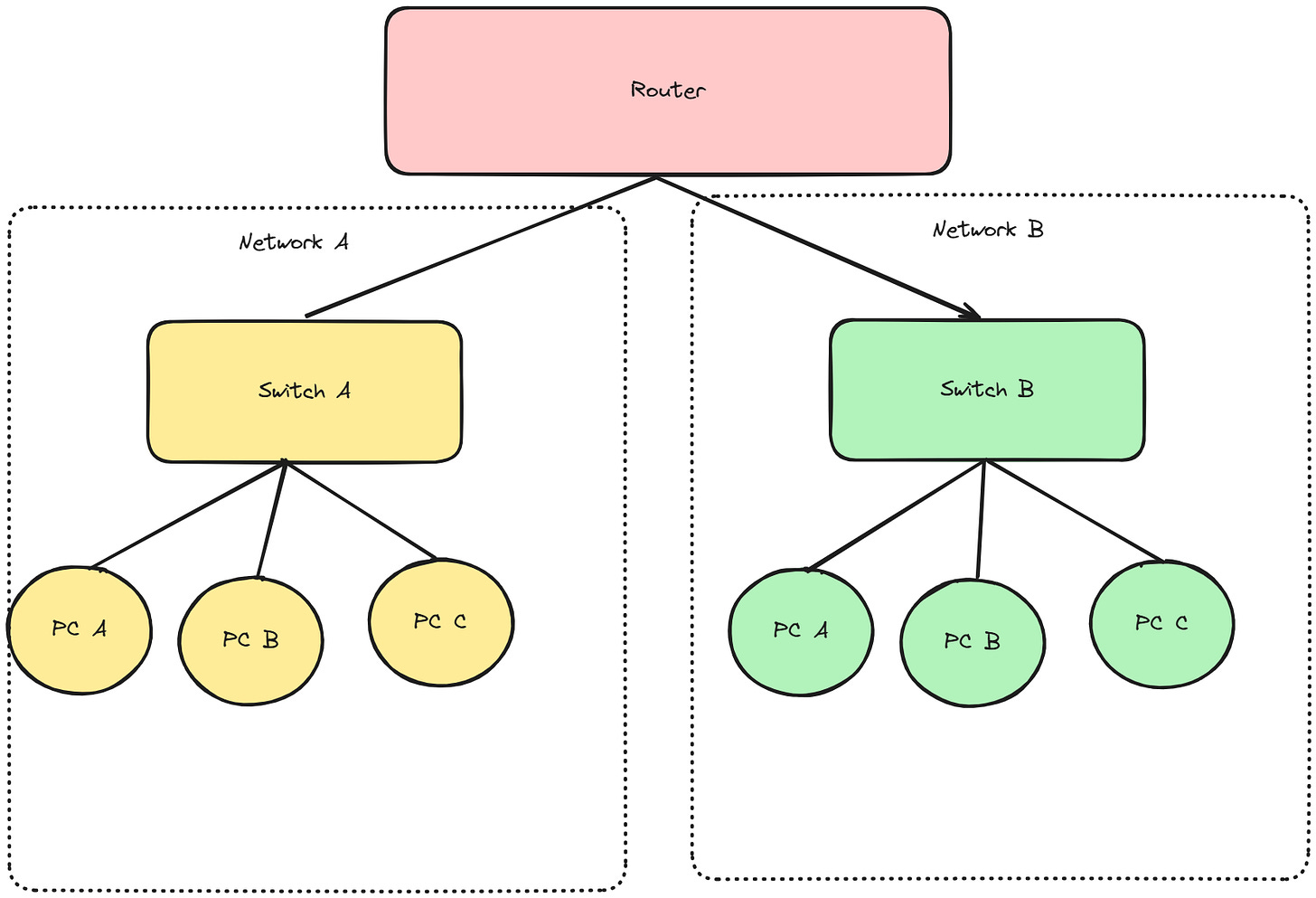
Routers
A router operates at the Network layer (Layer 3) and is responsible for directing traffic between different networks. Unlike switches, which forward frames within a LAN, routers make decisions based on IP addresses, not MAC addresses.
How routers work:
Maintain a routing table to determine the best path for each packet.
Forward traffic between networks, including LAN-to-LAN and LAN-to-WAN connections.
Can implement Access Control Lists (ACLs) to filter traffic, block unauthorized communication, and enforce basic security policies.
Support NAT (Network Address Translation) to map internal addresses to public IPs, protecting internal devices from direct exposure.
Security perspective (CISSP relevance):
Routers define the perimeter of network segments and are the first line of defense for inter-network traffic.
Misconfigurations can expose sensitive internal networks to attackers.
Proper ACLs, secure management interfaces, and monitoring are crucial to prevent unauthorized access.
They contribute directly to the Confidentiality, Integrity, and Availability of network data.
Additional points:
Routers are typically slower than switches because they examine Layer 3 headers, but modern hardware has improved performance.
Redundancy is important for maintaining availability.
Gateways
A gateway is a device that connects networks using different protocols or architectures, acting as a translator between them. Unlike routers, which operate strictly at Layer 3, gateways often work at higher layers, commonly the Application layer.
How gateways work:
Translate between protocols (e.g., IP to non-IP networks, or IPv4 to IPv6).
Enable communication between networks that otherwise could not understand each other.
Can include security functions such as filtering, logging, or encryption.
Security perspective (CISSP relevance):
Gateways are critical for protocol-level security, ensuring that incompatible systems can communicate safely.
Misconfigurations can create vulnerabilities, exposing sensitive systems to attacks.
They are often the bridge between internal and external networks, so securing them is crucial for defense in depth.
Examples:
Email gateways (translate between internal mail system and Internet SMTP).
VoIP gateways (connect IP telephony to traditional phone networks).
API gateways in modern microservice architectures.
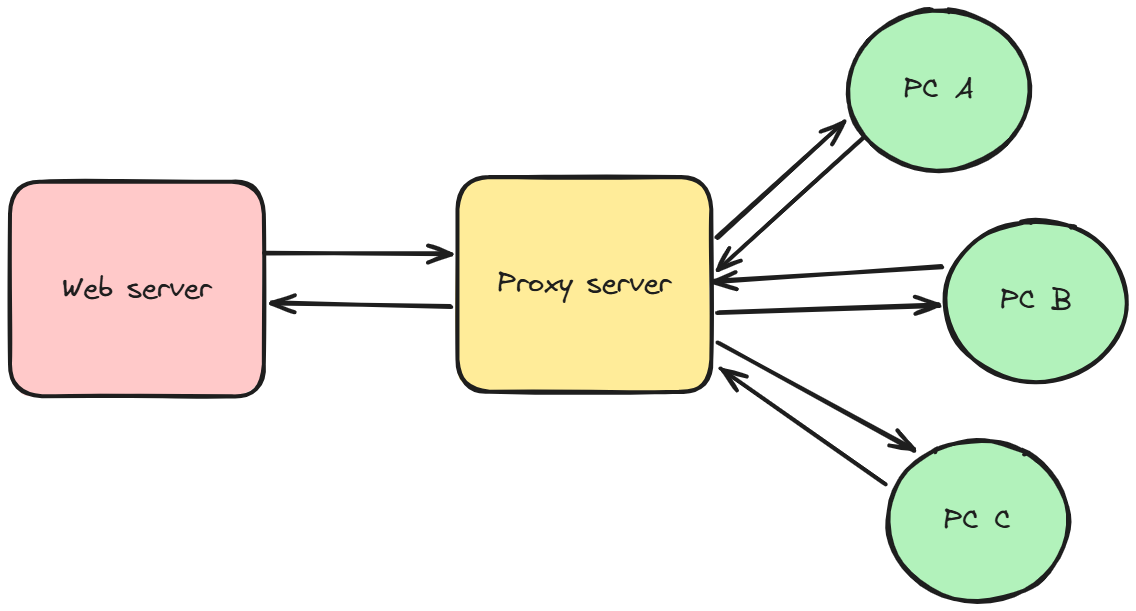
Proxy Servers
A proxy server is an intermediary between a client and a destination server, operating at the Application layer (Layer 7). It can filter traffic, provide caching, enforce security policies, and sometimes anonymize requests.
Types of proxy servers:
Forward Proxy:
Sits between clients and the Internet.
Controls and filters outbound traffic from internal users.
Can enforce policies, block malicious sites, or cache content for efficiency.
Reverse Proxy:
Sits between the Internet and internal servers.
Protects backend servers by hiding their IP addresses.
Can perform load balancing, SSL termination, or web application firewall functions.
Open Proxy:
A proxy accessible by anyone on the Internet.
Often misconfigured or intentionally public.
Security risk: can be abused for anonymizing attacks, spamming, or bypassing restrictions.
Security perspective (CISSP relevance):
Proxies are essential for defense in depth: they can filter malicious traffic, enforce access policies, and shield internal resources.
Misconfigured proxies (especially open proxies) can become a liability, allowing attackers to bypass security or abuse the network.
Understanding forward vs. reverse proxies is critical for designing secure architectures and exam scenarios.
Key takeaway:
Proxy servers are more than intermediaries, they are control points for traffic flow, security enforcement, and anonymity, making them a vital tool in both practical networks and CISSP knowledge.
Summary
If you’ve made it this far, congratulations! I’d love to hear your thoughts, leave a comment and let me know what you think about this article.
By now, it should be clear that network security isn’t just about firewalls, intrusion detection, or access controls.
It all starts with understanding the devices that form the foundation of networks themselves from simple repeaters to complex multilayer switches, routers, gateways, and proxy servers.
Each device operates at specific layers of the OSI model, has unique functions, and introduces potential security risks. Knowing how these devices work, their weaknesses, and how they interact is essential for both CISSP preparation and real-world cybersecurity.
Trust me, it really is.
Next time, we’ll dive into something even more exciting, now that we have a solid foundation to build on!


Loved it.