Threat ≠ Risk ≠ Vulnerability: Why CISSP Basics Matter More Than You Think
In my first week of CISSP prep, I went back to the basics, simply because I know how easily they’re misunderstood. This post is about the four terms everyone thinks they know… until they don’t.
Last time, I focused on the CIA Triad — the fundamental objectives of information security: Confidentiality, Integrity, and Availability.
If you missed it, stop reading and go check it out HERE! You’ll need it
The first week of my journey is almost over, and it was all about terms.
Well, no surprise there!
As I’ve said before, if you don’t fully understand the basics, everything else gets shaky at best.
And that’s why I’d like to take a closer look at four basic terms.
Why do I dedicate a whole post to those only FOUR basic terms?
Glad you asked!
Because they’re often misunderstood, misused, or worse, used interchangeably when they absolutely shouldn't be.
These concepts are the building blocks for understanding risk, strategy, and technical controls.
Let’s dive in.
Threat
Let’s start with the one that sounds the scariest.
But before we do! Let me know in the comments how you would define a threat!
A threat is any potential danger that is associated with the exploitation of a vulnerability.
Let me repeat it one more time: a threat exploits vulnerability.
And here is the catch, a threat always exists. You can’t control them. It’s beyond your reach.
What you can control are the vulnerabilities of your system.
Confusing?
No worries, I was once too.
Let’s go ahead and define vulnerability, and I’ll show you the difference with an example.
Vulnerability
A vulnerability is a weakness in a system that allows a threat source to compromise its security.
It might be:
A misconfigured firewall
An unpatched system
Weak access controls
Or even poor training of the company’s employees
No vulnerability? The threat has no entry point.
But combine a threat and a vulnerability, and suddenly you have a real problem.
Risk
A risk is the likelihood of a threat source exploiting a vulnerability and the corresponding business impact.
See the problem?
Risk isn’t an event.
It’s not a cyberattack.
It’s not a data breach.
Risk is a possibility. A chance of something (negative) happening.
Control
A control is put in place to mitigate the potential risk.
It reduces potential risk. Which means it reduces the potential likelihood of an event. It doesn’t eliminate the threat, but it might remove a vulnerability or reduce the likelihood of its exploitation.
Wrap up
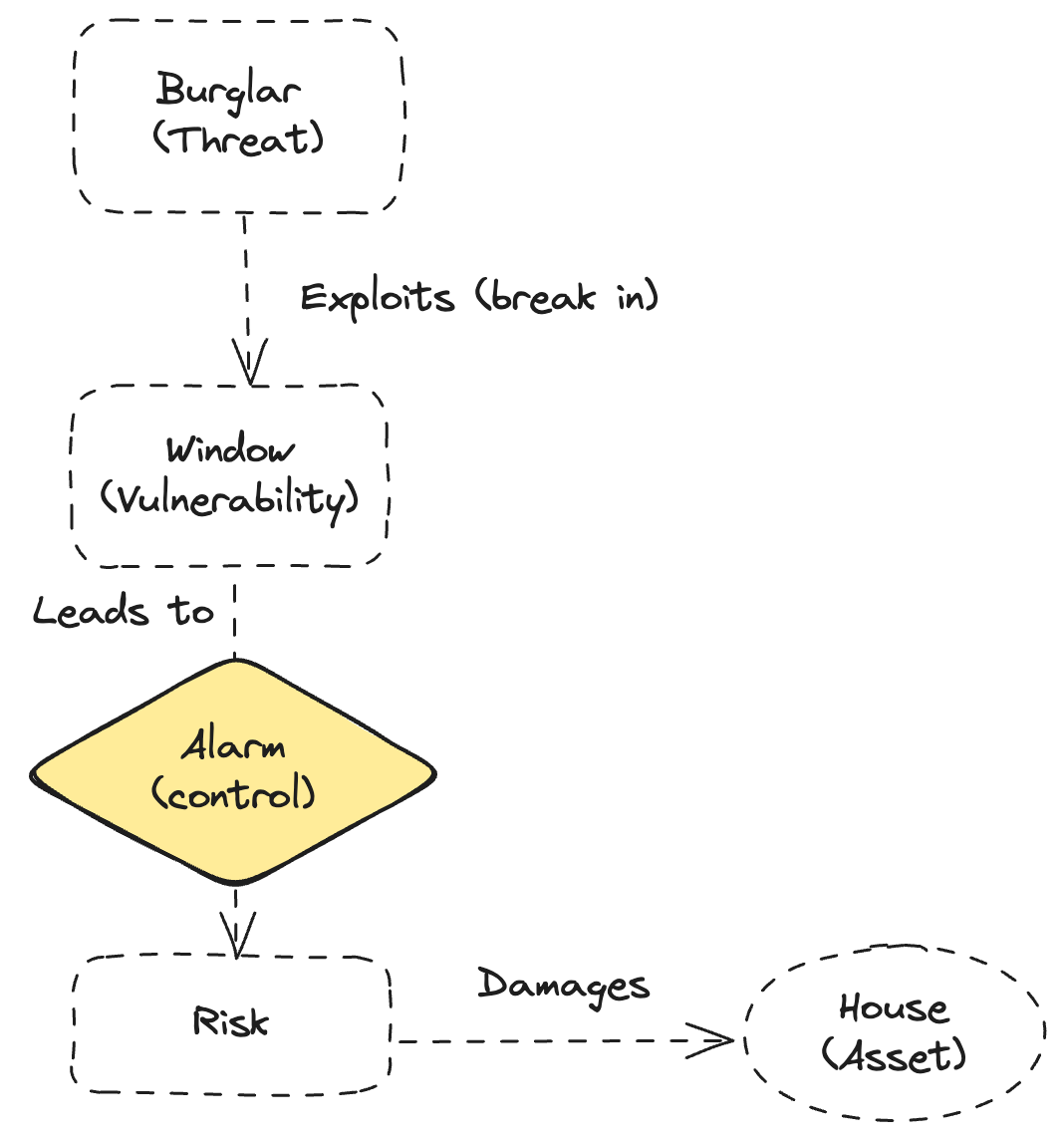
Enough with boring definitions! Let’s me show the relationship between the terms in one simple example.
Imagine a house with a broken window (vulnerability). There’s a burglar in the neighborhood (threat). The risk is that the burglar might notice the window and break in.
Now, installing a camera or alarm system won’t stop the burglar from existing. It won’t fix the window either. But it might discourage the burglar or notify you quickly if something goes wrong.
Key takeaways
Controls don’t exist in a vacuum — they exist to support the security objectives (CIA) and to reduce the risk that threats will exploit vulnerabilities.
Threats exist whether you like it or not.
You can’t eliminate them — but you can prepare for them.Risk is not an event — it’s the probability of an event.
Controls mitigate risk, not threats
Everything ties back to the CIA Triad.
If a control doesn’t support Confidentiality, Integrity, or Availability, ask yourself why it exists.
Study tips
Use analogies - If you’re struggling with definitions like risk, threat, or vulnerability — try to create your own real-life metaphors.
Write definitions in your own words. Don't just memorize what's in the book. Rewrite each term in a way you'd explain it to someone else. Kind of what I am doing here!
Quiz yourself in both directions. Instead of just “What is a threat?” also ask: “Is this example a threat, vulnerability, or control?”
Draw connections. Use simple diagrams or mindmaps (like the one I made this week) to see how terms relate. And since you’re still reading this, I’ll always share my mindmaps with you!
What’s Next
I know this isn’t a post that would be exciting and easy to read. But Cybersecurity isn’t just fun. To build secure and holistic systems, there needs to be a clear understanding of the basic terms and concepts we are building on.
So if you’re still reading this, congratulations! You’re on a good path to fully understand what cybersecurity is all about!
And next time?
Next time, we’ll take a look at organizational roles and responsibilities!
Because Cybersecurity isn’t just for Cybersecurity engineers, but you know that by now!
Let me know in the comments if you’ve known these terms before!
If you're interested in following my journey (or just want to steal a few insights for your own CISSP prep), feel free to subscribe — I’d love to have you onboard.