This Is How I Explain The Man-in-the-Middle Attacks To a Beginner
Most people can define a Man-in-the-Middle attack. Almost no one understands how it actually works. In this guide, you’ll simulate it yourself, capture a real session, and see how attackers work!
For years, I was given one question that I thought I could answer perfectly.
It was the CISSP exam that made me realize that what I know isn’t enough.
The question was quite simple: What is a Man-in-the-Middle attack?
And I got a very simple answer: It is a type of attack where an attacker positions himself between two parties who believe they are interacting directly.
Easy and correct answer, right?
Well, it is. But if you believe this is enough to pass cybersecurity exams and interviews, you’re wrong.
After reading this article, you will know everything you need to know about this attack for CC, Security+, CISSP exams, and in actual real-world scenarios.
Warning: CC, CISSP, and Security+ relevant topic!
What is a MitM Attack?
Let’s start from the beginning and describe what this term means.
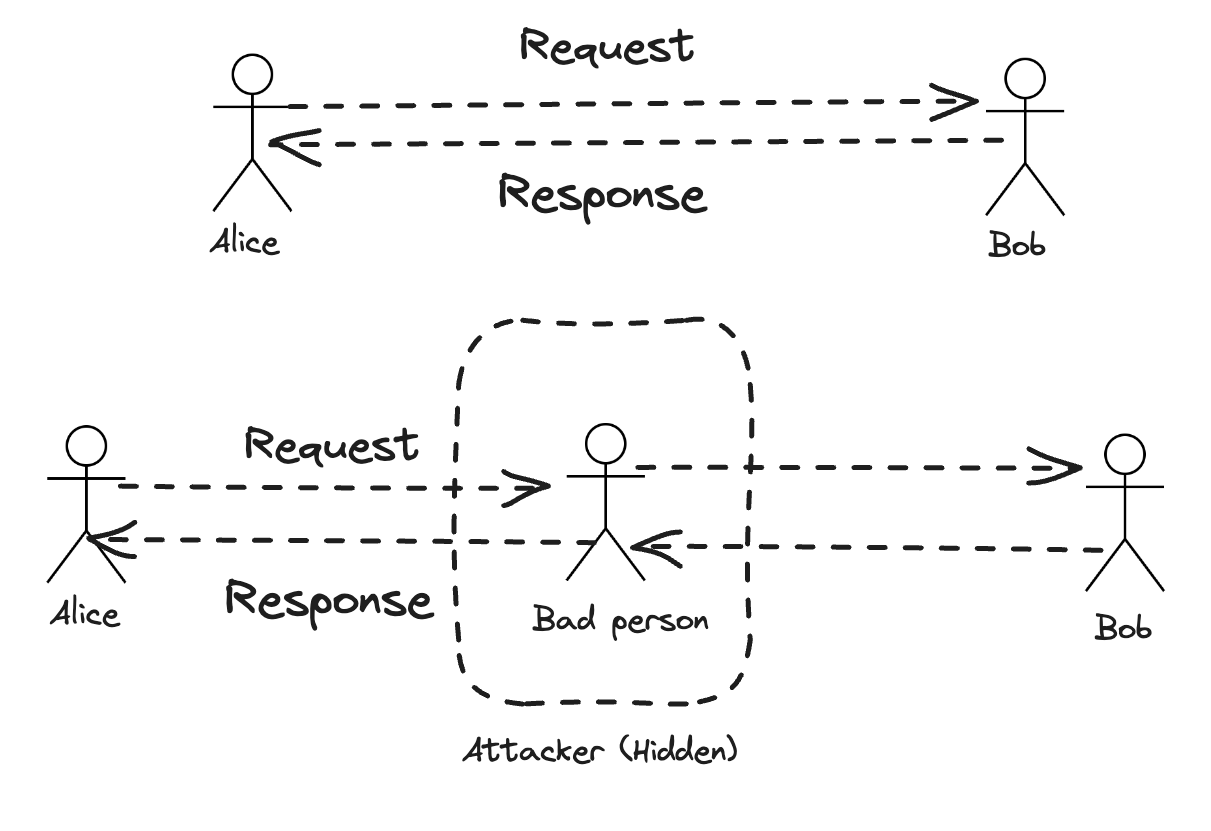
The MitM Attack is a TYPE of attack where an attacker positions themselves between two parties communicating.
Instead of:
Client → Server
It becomes:
Client → Attacker → Server
And what is so dangerous about it?
The client probably won’t even recognize it. Everything works as usual. You open any website, check your emails, and watch YouTube videos.
But the attacker can now:
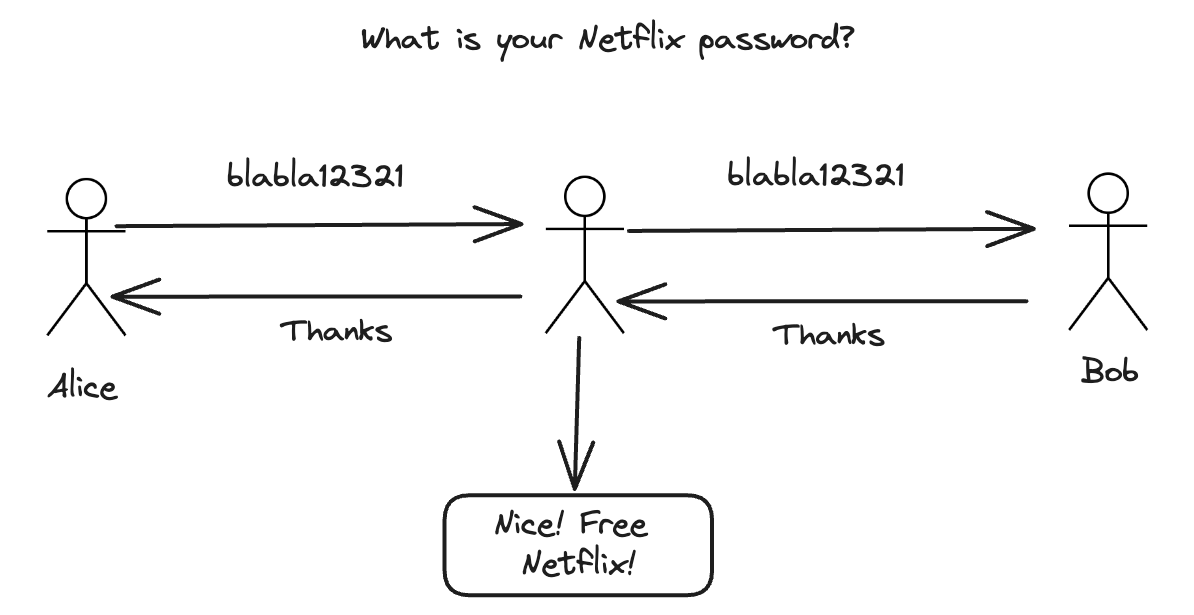
Read the traffic
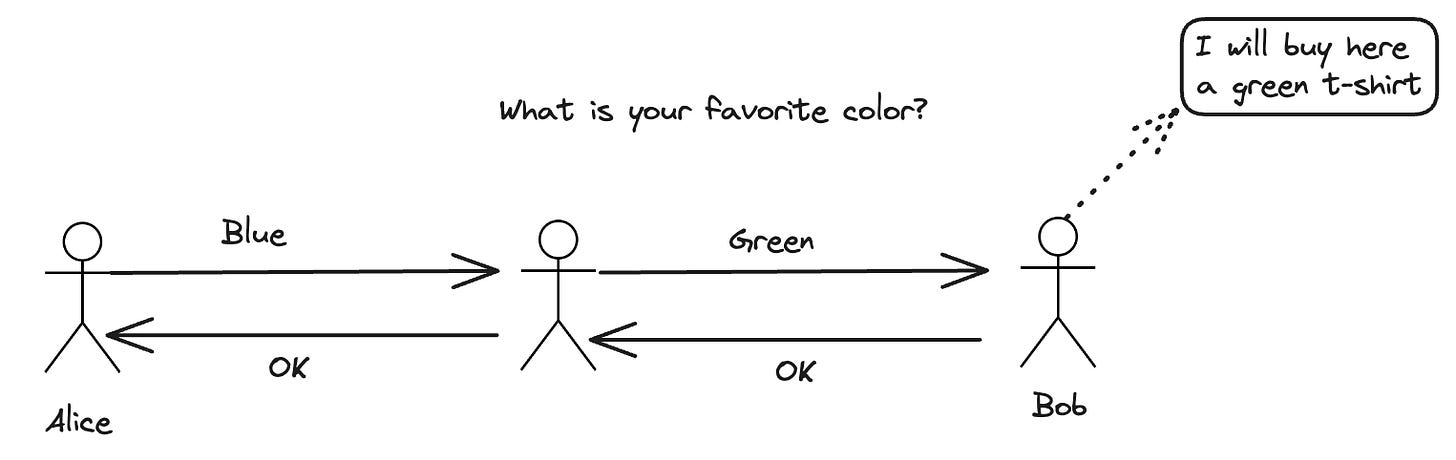
Modify it
Steal sensitive data
In other words, all core Cybersecurity objectives of the CIA triad are threatened.
And yes, you guessed it right, that’s no good.
Before we go through a specific example, let’s answer one more question that is frequently asked in both exams and interviews.
Question: How does a MitM attack affect the core cybersecurity objectives?
Answer:
CIA Triad
Confidentiality - Broken
Compromised
Without further security controls, the attacker can intercept sensitive data (passwords, emails, tokens)
Integrity
Compromised
An attacker can modify messages in transit
→ Data arrives altered without the sender/receiver knowing
Availability
Usually unaffected (but can be impacted)
MitM is primarily passive/stealthy
→ In some cases, an attacker may drop or delay packets (DoS-like behavior)
So, if you ever get this question, and if you’re serious about cybersecurity, you probably will, make sure to understand which core cybersecurity objectives are typically the most affected by this type of attack.
Great! Enough theory!
Now it’s time to get some hands-on experience and try this attack by yourself.
Because that’s what differentiates people who know just theory, and who actually understand the concept. You can’t replace hands-on experience with hours of reading.
And that’s why I prepared a simple Docker Lab, which will guide you step by step on how to simulate this attack.
Let’s get to it!
Are you preparing for the CC, Security+, or CISSP exam?
Comment “CYBERSECURITY” and I will send you a free guide focusing on Top 10 Cybersecurity Fundamentals.
Hands-On Docker Lab: Man-in-the-Middle Attack
How the attack actually happens
Let’s do something most cybersecurity content never shows you:
Instead of just reading about a Man-in-the-Middle attack, you’ll simulate one yourself.
What you’re about to build
You will simulate this exact scenario:
Victim (Browser) → Attacker (MitM Proxy) → Web ServerThe attacker will sit in the middle and capture session data in real time.