The Complete Guide to Firewall Types: From Packet Filters to Next-Gen
You know how, when you say the word cybersecurity, the first thing people think of is firewalls? Well, it’s finally time to take a closer look at them.
No matter how much you try to convince people that Cybersecurity isn’t about firewalls, you probably won’t.
But that doesn’t make them any less important.
It is a crucial part of network security that plays a crucial role in today’s systems.
What I want to show you today are different types of firewalls that exist.
Each type is convenient for different usage, and understanding how they work is essential for making good decisions. And that’s what Cybersecurity is really all about.
Types of Firewalls
Different firewalls serve different purposes.
Here’s how they evolved and what makes each type unique.
1. Packet Filtering Firewall
The earliest and simplest type is often referred to as a first-generation firewall.
They make access decisions based on basic network information, such as:
Source and destination IP addresses
Source and destination port numbers
Protocol type
Traffic direction (inbound/outbound)
They operate statelessly, meaning they don’t track the state or context of a connection.
Think of them as a security guard who only checks IDs, but doesn’t remember who’s already inside.
Weaknesses:
Can’t detect attacks using application-layer vulnerabilities
Limited logging capabilities
Lacks advanced authentication support
Struggle with packet fragmentation attacks
2. Stateful Firewall
A stateful firewall is like a nosy neighbor, it keeps track of ongoing conversations and knows who said what to whom.
It maintains a state table, recording the details of every active connection.
By tracking TCP sessions, it can make smarter decisions and block traffic that doesn’t belong to a valid session.
This adds significant protection over packet filtering, especially against spoofing and session hijacking attempts.
3. Proxy Firewalls
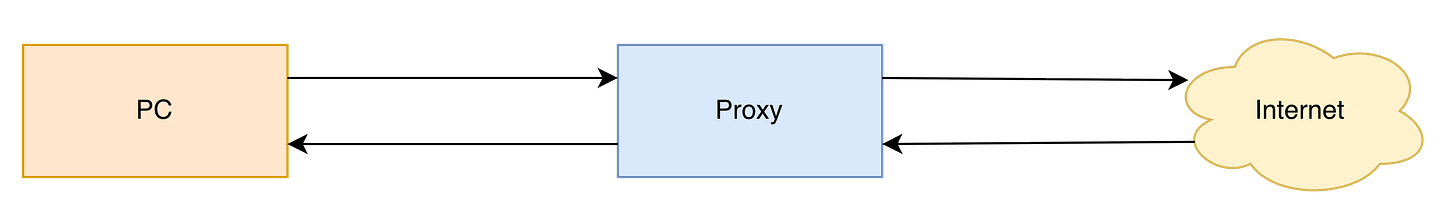
Proxy firewalls go one step further. Instead of allowing direct connections between systems, they act as intermediaries, essentially creating two separate connections.
They come in two main forms:
Circuit-Level Proxy
Operates at the session layer
Establishes a virtual “circuit” between the client and the destination
Makes decisions based on session information rather than packet headers
Used for secure channeling (e.g., SOCKS proxies)
Application-Level Proxy
Inspects traffic all the way up to the application layer
Understands application-specific protocols like HTTP, FTP, or SMTP
Provides deep inspection and extensive logging
Can directly authenticate users
Offers strong protection against spoofing and advanced attacks
However, these come with trade-offs:
Each protocol requires its own proxy module
Higher processing overhead → slower performance
Not ideal for high-bandwidth or real-time applications
In short:
Application-level proxies offer deeper inspection and more security, while circuit-level proxies provide broader compatibility with less processing overhead.
4. Next-Generation Firewalls (NGFW)
Modern firewalls combine all the best features of earlier generations and then add intelligence.
Next-Generation Firewalls include:
Integrated Intrusion Prevention Systems (IPS) using signature-based and behavioral analysis
Context-aware filtering (e.g., user identity from Active Directory)
Integration with external data sources such as whitelists, blacklists, and policy servers
Application awareness - understanding traffic beyond ports and protocols
They deliver unmatched visibility and control, but at a cost:
They’re complex and expensive, requiring proper configuration and ongoing maintenance.
Conclusion
You can’t build a secure network without firewalls. But not all firewalls are created equal.
Even a basic understanding of the different types gives you a real advantage.
Remember, simply blocking malicious traffic isn’t the whole story.
Use the wrong type of firewall, and you might block legitimate traffic or break your entire network.
So how do you know which firewall is right for you?
You start with your network architecture and requirements.
And that’s exactly what we’ll look at next time, so make sure to subscribe and don’t miss it!
Key Takeaways for CISSP
Packet filtering firewalls are fast but stateless. It is good for simple environments.
Stateful firewalls track active sessions, providing context-aware decisions.
Proxy firewalls (application or circuit-level) act as intermediaries, providing strong isolation and inspection capabilities.
Next-Generation Firewalls combine traditional filtering with IPS, identity, and application awareness.
Real security comes from understanding how and why these technologies work, not just deploying them.