The AAA Framework: Can Your Cowoker’s Account Get You Fired?
Can you really get fired because your coworker deleted an important file? It wasn’t your fault, but here’s the catch: He claims it was you. What do you do? GO!
How does Instagram know that it is really you who posted that story?
How does any app know that it is you in today’s world?
How can anyone be sure that it is really you?
How do we build that trust on the internet and other networks?
Let me show you one of the fundamental frameworks that helps us build trust in digital systems.
AAA stands for Authentication, Authorization, and Accounting.
What do these things have in common?
You might think you know all that, but I don’t think you see the whole picture!
Warning: Crucial topic for the CISSP exam.
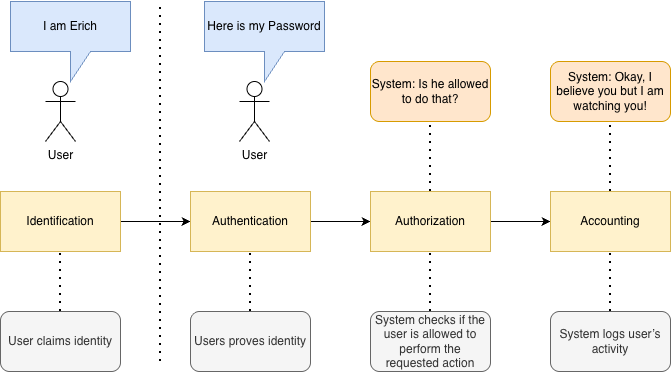
The AAA process
The process consists of 4 activities, which are actually very easy to follow.
AAA is important because it ensures only the right people get in, they can only do what they’re supposed to do, and every action they take is recorded.
Do you think you really know AAA?
Let’s find out. I’ve put together a 10-question quiz.
Can you score at least 8/10?
👉 Take the Quiz!
The hidden “I”
You don’t see this activity in the acronym. There is no IAAA. But it is an important prerequisite for what’s going to happen next.
The “I” stands for Identification, and it is the act of a user presenting something that claims their identity. This
could be a username, an email address, or even a physical badge.
This is where you say: Hi, I am [name].
Enjoying reading this article? Let me know in the comments!
Authentication - Oh, really? Show me
Of course, anyone can say it’s you.
So this is where we define how you prove to the system that it is really you.
The system checks your claim against something it trusts:
Passwords
MFA
Biometrics
Identity provider database
This is where weak passwords die, and MFA saves careers. Imagine your coworker logs into your work account and performs an action that gets you fired.
It is your account, everything is on you.
Note: Turn that 2FA on!
And if you’re studying for the CISSP?
This topic will appear in your exam, and understanding these distinctions isn’t something you can avoid.
If you found this helpful, consider joining our fast-growing community of over 500 people.
Authorization - Okay, it is you! But can you do that?
Definition: Authorization determines what the AUTHENTICATED user can access by checking the user’s permissions based on pre-defined policies.
Once you’re authenticated and the system is sured it is really you, it is time for a second question:
“What can this identity do?”
This is authorization.
And it’s based on policies, permissions, and the principle of least privilege.
Examples:
Marketing can access CRM → Yes
Marketing can access financial database → Absolutely not
Interns can access production systems → If they can, you have bigger problems
Mistakes here are what lead to the infamous:
“User had admin rights for no reason.”
Accounting: Did You Do It? Let’s Take a Look
Definition: Accounting means tracking and recording user activity and making sure that no one can deny their actions!
It tracks:
What the user accessed
When they accessed it
What they did
For how long
This data becomes your audit trail, the single most underrated security control in existence.
Why?
Because you can’t defend what you can’t see.
That’s accountability: Identity + Logs = Proof
AAA or AAAA? (The Debate No One Asked For But Actually Matters)
Definition: Auditing is the tracking of activities on systems through logging.
Some sources add a fourth “A”: Auditing.
So instead of:
Identification → Authentication → Authorization → Accounting
you get:
Identification + Authentication + Authorization + Auditing = Accounting
Is the fourth A necessary?
YES!
I like the expanded version because it highlights something that is absolutely crucial in practice:
You can’t have accountability without auditing.
And without accountability, your security policy is just a suggestion.
If you don’t have that audit trail, you are not able to prove that someone violated your security policy.
If you are not able to prove it, you are probably not able to enforce the policy.
And if you are not able to enforce it, it doesn’t need to exist in the first place.
So what is the key takeaway here?
Design your systems to log the activity of their users and create an audit trail. That’s how you hold everyone accountable for their actions.
The AAA framework is just one small piece of the puzzle of the CISSP exam.
If you want a structured way to master Domain 1 of the CISSP exam, I’ve created something for you.
My CISSP Domain 1 Checklist provides clarity and focus on everything that truly matters for the exam and real-world practice.
➡️ Download it here and stop wasting time on scattered study materials.
Conclusion
If you’re reading this, congratulations! You just got familiar with a crucial security concept that not only security professional needs to be aware of.
It doesn’t matter if you’re preparing for the CISSP exam or you simply want to learn the core cybersecurity concepts. This is something you need to know.
Key Takeaways:
Identification is the first step: You must present a claim of who you are. Without this, nothing else works.
Authentication proves it: Passwords, MFA, biometrics. These mechanisms confirm your identity. Turn on 2FA, it really matters.
Authorization limits what you can do: Permissions and policies define your access. The principle of least privilege prevents mistakes that can cost organizations millions.
Accounting and Auditing ensure accountability: Logs and audit trails let you track actions, detect violations, and enforce policies. Without them, security is just a suggestion.
Trust in digital systems isn’t automatic: It’s designed, enforced, and recorded. AAA provides the blueprint.
Thank you for reading Decoded Security!
Any feedback is greatly appreciated!
Have you taken the quiz?
Circle back to the top and see how many questions you nailed. If you scored 8/10 or more, you’re on solid ground.
And if you didn’t, now you know exactly what to review.
Ready to level up your cybersecurity skills?
💬Comment below and tell me what your experience with SLAs is
❓Take the quiz to test your understanding: CybersecErich: Quiz Hub
📰Subscribe (free or paid) to get new posts straight to your inbox.
Share this with a friend studying for CISSP, or anyone curious about cybersecurity.


Thanks Erich for another excellent post. Thanks also for highlighting the importance of auditing. This is something that also gets completely overlooked sometimes in qualitative research, but without that, basically, how can we have any reliability on the work that we've done? Thanks again for this insightful post.