Risk Management: Managing risks in six steps
Cybersecurity starts with understanding risk. Learn the 6-step cloud risk management process, from identifying threats to continuous monitoring, and protect your data while mastering CISSP essentials.
Introduction
My CISSP exam is coming up, so I’m reviewing the most crucial aspects of cybersecurity management.
Risk management is the single most reliable thing an organization owns that turns uncertainty into action. Before frameworks, tools, or compliance checklists, you must answer two questions: what matters and what are we willing to risk to protect it?
This article walks through a practical, repeatable risk-management process you can use for CISSP study and the real world.
Risk management
It all starts with a risk assessment. I don’t think it will be any surprising to you if I tell you that you need to analyze the situation to find out what will be your next steps.
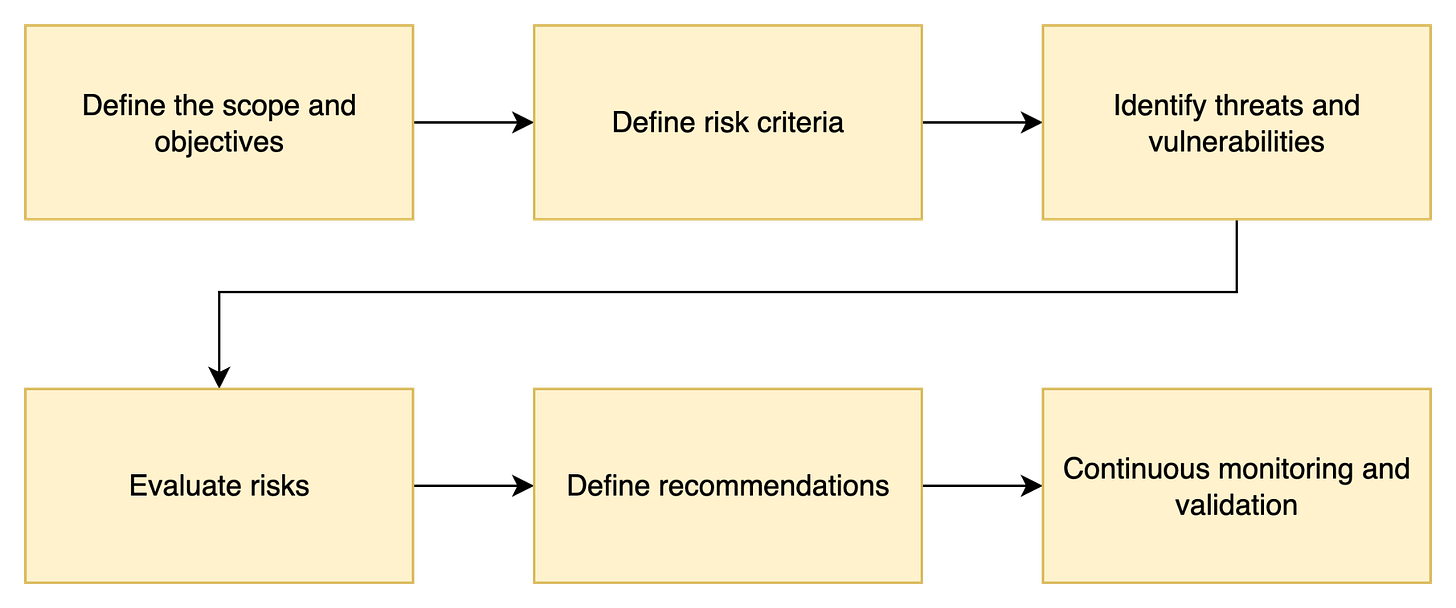
To make it easier to comprehend, I divided the whole process into 6 steps and I would like to walk you through them.
Step 1: Define the scope and objectives
Every risk assessment begins with planning. Before looking at threats or vulnerabilities, you must decide what the assessment is actually about.
Start with the objectives. Are you evaluating:
Operational risks that might disrupt day-to-day business?
Regulatory compliance risks tied to laws or standards?
The effectiveness of existing security controls?
Your scope should then set clear boundaries: which systems, services, or business processes are in play, and just as importantly, which are out. At this stage, identify the key stakeholders who must provide input or approve the results.
Finally, list and classify the assets worth protecting. An asset is anything of value to the organization: data, systems, people, reputation, even physical facilities.
By assigning value, you create the foundation for prioritization: protect what matters most first.
💡 CISSP exam tip: Always tie the first step of risk assessment back to business objectives. Security serves the business, not the other way around.💡
Step 2: Define Risk Criteria
Once you know what you’re assessing, the next step is to decide how you’ll measure and evaluate risks.
Without clear rules, every assessor will use their own judgment, and the results won’t be consistent or defensible.
Start by setting impact categories. Define the types of consequences that matter to your organization, typically:
Financial (loss of revenue, extra costs)
Operational (downtime, productivity loss)
Regulatory (fines, legal penalties)
Reputational (loss of trust, brand damage)
For each category, establish levels of severity (for example: negligible, minor, moderate, major, catastrophic).
Next, set likelihood categories. These describe the probability that a given risk will occur (rare, unlikely, possible, likely, almost certain).
Like impact, these should be scaled and defined so different assessors reach the same conclusion.
Define the organization’s risk tolerance or threshold.
This is the line between acceptable, tolerable, and unacceptable risk. Example: “We accept no risks that could cause regulatory fines above €50,000.”
Finally, establish a clear evaluation methodology.
Will you use a qualitative matrix (e.g., impact × likelihood = risk rating), a quantitative model (e.g., annualized loss expectancy), or a hybrid?
Whatever you choose, document the criteria so that risk is always measured consistently across teams, assessments, and time.
💡 CISSP exam tip: Remember that risk criteria are set by management, not security teams. Your job is to facilitate and apply them, not to decide what the business can or can’t accept.
Step 3: Identify Threats and Vulnerabilities
With scope and criteria in place, the next step is to uncover what could actually go wrong. This is where we connect assets, vulnerabilities, and threats to form the basis of risk.
The process works like this:
Asset → Vulnerability → Threat → Risk
Vulnerabilities are weaknesses in your environment. For example, misconfigured cloud storage, unpatched systems, or weak authentication.
Threats are actors or events that could exploit those weaknesses. A malicious insider, a hacker group, or even a natural disaster.
To structure this analysis, security professionals use threat modeling. Two key frameworks help:
CIA Triad (security objectives)
Start by considering which aspect of security could be at risk:
Confidentiality → Preventing unauthorized access to data.
Integrity → Ensuring data is accurate and unaltered.
Availability → Keeping systems and data accessible when needed.
STRIDE (threat categories)
Next, map specific threats to vulnerabilities using the STRIDE model:
Spoofing Identity → Impersonating users or systems.
Tampering with Data → Unauthorized data modification.
Repudiation → Denying malicious actions without proof.
Information Disclosure → Gaining access to sensitive information.
Denial of Service (DoS) → Disrupting availability of systems/services.
Elevation of Privilege → Gaining higher access than authorized.
For example:
Asset: Customer database
Vulnerability: Weak database access controls
Threat: Unauthorized access (Spoofing Identity, Information Disclosure)
Risk: Confidentiality and regulatory compliance failure
By systematically mapping vulnerabilities to threats and linking them to assets, you ensure no major category of risk is overlooked.
💡 CISSP exam tip: Know that threats exploit vulnerabilities to impact assets — and that frameworks like CIA and STRIDE are complementary tools for structured analysis.
The outcome of this step is a risk register: a structured list that documents each identified risk with its related asset, vulnerability, threat, and potential impact.
Step 4: Analyze and Evaluate Risks
Once threats and vulnerabilities are identified and documented in the risk register, the next step is to analyze each risk and determine its priority. This step turns raw observations into actionable insights.
1. Evaluate Risk Probability
Estimate the likelihood that each threat will exploit a vulnerability. Consider historical data, industry trends, and internal controls. Categories can be qualitative (Rare, Unlikely, Possible, Likely, Almost Certain) or quantitative (0–1 probability).
2. Determine Business Impact
Assess what would happen if the risk materialized. Consider multiple dimensions:
Financial impact → Lost revenue, fines, or remediation costs
Reputational impact → Loss of customer trust or public confidence
Operational disruption → Downtime, decreased productivity
Legal and regulatory implications → Non-compliance fines or lawsuits
3. Calculate Risk Priority
Combine probability and impact to determine which risks need attention first. Two common approaches:
Qualitative assessment: Use a risk matrix to assign ratings like High, Medium, or Low. Example: High likelihood × High impact → High risk.
Quantitative assessment: Multiply probability × impact to produce a numeric risk score for comparison. Example: 0.4 likelihood × $500,000 impact → $200,000 expected loss.
4. Document and Assign Ownership
Update the risk register with each risk’s score, rating, and assessment notes. Assign a risk owner responsible for monitoring and managing that risk. A clear owner ensures accountability and follow-up.
💡 CISSP exam tip: Risk analysis is about prioritization, not perfection. Focus on the risks that could have the biggest impact on the organization, and make sure each one is tracked and assigned.
Step 5: Treat and Mitigate Risks
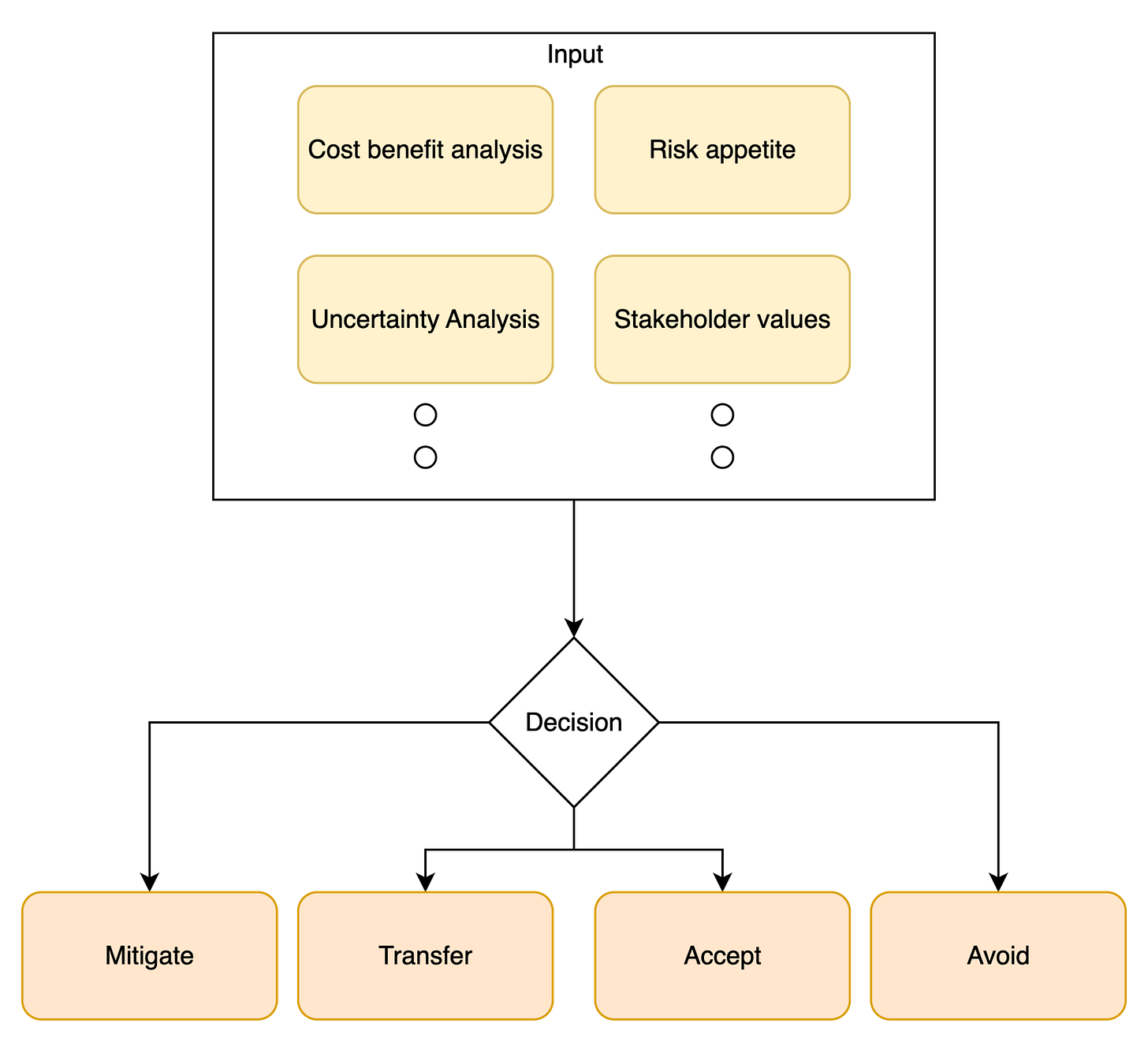
After analyzing and prioritizing risks, the next step is to decide how to respond. That means making a risk treatment decision.
There are four primary options according to ISO standards:
Risk Mitigation → Implement controls to reduce probability or impact. For example, apply encryption, multi-factor authentication, or access controls. Monitor effectiveness continuously.
Risk Transference → Shift risk to a third party, often via insurance or outsourcing.
Risk Acceptance → Do nothing because the risk is within the organization’s tolerance. Document the rationale and review periodically.
Risk Avoidance → Eliminate the risk entirely by discontinuing the risky activity or process.
Control Selection and Implementation
Choose controls that provide maximum risk reduction at acceptable cost. Use cost/benefit analysis to justify each control. After implementation, ensure controls are monitored to verify effectiveness.
Document Decisions
Update the risk register with the chosen treatment, selected controls, ALE calculations, and risk owner. Documentation ensures accountability, auditability, and clarity for future reviews.
💡 CISSP exam tip: Remember the four treatment options (Mitigate, Transfer, Accept, Avoid) and the principle of cost-effective control selection. You’re not aiming for zero risk, but for balanced, justifiable protection.
Step 6: Monitor and Review Risks
Risk management is not a one-time activity. It’s a continuous process. Step 6 ensures that cloud resources, systems, and third-party services operate as intended and that mitigation measures remain effective over time.
Purpose
Ensure systems and cloud services function according to security expectations.
Detect new threats or vulnerabilities as they emerge.
Validate that risk treatment measures continue to be effective.
Key Components
Effectiveness Monitoring
Confirms that mitigation measures actually work.
Example: Track the number and severity of security incidents to see if implemented controls reduce risk.
Change Monitoring
Detects new risks introduced by updates, configuration changes, or new deployments in the cloud environment.
Example: Monitor changes to firewall rules or access policies that could open vulnerabilities.
Compliance Monitoring
Confirms that operations adhere to legal, regulatory, and contractual requirements.
Example: Respond to audit findings, conduct GDPR or ISO 27001 compliance checks.
By regularly monitoring effectiveness, changes, and compliance, organizations can update the risk register, adjust controls, and respond proactively to new threats. This closes the loop in the risk management process, turning a static assessment into a dynamic, living practice.
💡 CISSP exam tip: Think of monitoring as risk validation and continuous improvement. The assessment doesn’t stop once controls are applied.
Example: Risk Management for a Cloud Environment
Let’s demonstrate the full risk management process using a cloud storage and compute environment as an example.
Step 1: Define Scope and Objectives
Scope: Cloud storage and compute environment, including IAM roles and user accounts.
Objective: Identify risks that could compromise the confidentiality, integrity, or availability of sensitive data.
At this stage, we also list the key assets (user accounts, data repositories, virtual machines) and key stakeholders (cloud administrators, security team, business owners). This ensures the assessment focuses on what truly matters.
Step 2: Define Risk Criteria
Impact Categories:
High → Data breach with regulatory fines
Medium → Operational disruption
Low → Minor inconvenience
Likelihood Categories:
High → Vulnerability exists and is easily exploitable
Medium → Exploit requires specific conditions
Low → Rare occurrence
Risk Threshold:
High or Medium → must mitigate
Low → acceptable
Scoring Method:
Qualitative: Risk = Impact × Likelihood → High / Medium / Low
These criteria allow consistent evaluation across all risks in the cloud environment.
Step 3: Identify Threats and Vulnerabilities
Vulnerability: IAM misconfiguration allows a user to escalate privileges.
Threat: Malicious insider or compromised account attempting privilege escalation.
CIA Analysis:
Confidentiality: Sensitive data could be exposed.
Integrity: Sensitive data could be modified by an unauthorized user.
Availability: Unauthorized user could delete resources.
The risk register at this stage captures the asset, vulnerability, threat, and affected CIA dimension.
Step 4: Analyze and Evaluate Risks
Impact: Access to sensitive data → High
Likelihood: Medium → misconfiguration exists but requires internal access
Risk Rating: High → must be mitigated
The risk register is updated with this evaluation, and a risk owner is assigned to ensure follow-up.
Step 5: Treat and Mitigate Risks
Recommended Actions:
Implement least privilege principle for IAM roles
Enforce strong password policies
Conduct regular access reviews
Enable multi-factor authentication
Monitor and audit activity via SIEM
Adopt cloud provider best practices
A cost/benefit analysis supports these treatments by weighing the reduction in expected loss (ALE) against the cost of implementing controls. Each decision is documented in the risk register for accountability.
Step 6: Continuous Monitoring and Validation
Track the number of security incidents by severity to verify effectiveness of IAM controls.
Monitor changes in the cloud environment (new deployments, configuration changes) that could introduce new risks.
Validate compliance with regulatory and contractual requirements (e.g., GDPR, ISO 27001).
This continuous monitoring ensures the risk management process remains dynamic and effective, adapting to new threats and changes in the cloud environment.
Conclusion
Congratulations on making it to the end!
Risk management is a complex topic, and I tried to cover it as clearly and practically as possible. I hope this guide helped you understand not just the steps, but why risk management is so essential in cybersecurity.
I’d love to hear your thoughts, please leave a comment and share your perspective!
If you want to dive deeper into cybersecurity topics and learn how to protect yourself in the digital world, I’d be thrilled to have you join me on this journey. Let’s learn and grow together!
Glossary
Vulnerability: A weakness in a system or process that can be exploited by a threat.
Threat: Any potential event or actor that can cause harm by exploiting a vulnerability.
Risk: The likelihood and impact of a threat exploiting a vulnerability.
Asset: Anything valuable to an organization that needs protection.
ALE (Annualized Loss Expectancy): The expected yearly monetary loss from a specific risk.
SLE (Single Loss Expectancy): The monetary loss expected from a single occurrence of a risk.
ARO (Annual Rate of Occurrence): How often a specific threat is expected to occur in a year.
Total Risk: The overall risk exposure before any controls are applied.
Residual Risk: The remaining risk after security controls are implemented.
CIA Triad: The core principles of security: Confidentiality, Integrity, and Availability.
CVSS: A standardized score that measures the severity of a vulnerability.



Really appreciated how you took “Risk Management” out of the abstract and turned it into a concrete six‑step loop that someone can actually run, especially in a cloud context.
The constant reminder that risk is about business objectives first - and that monitoring keeps the register alive instead of static - is the bit I wish more orgs would absorb.
That was a long one, pheww