How Risk Management Frameworks Keep Systems Secure
NIST or ISO? Learn the frameworks that keep systems secure and boost your CISSP knowledge.
Introduction
A big part of Cybersecurity is about managing risks. That’s no big surprise.
But how do we do that? What is the line between “managed” and “unmanaged” risk?
How do professionals systematically identify, assess, and respond to these risks?
The answer is simple, we don’t reinvent a wheel but we rely on one of the well established Risk Management Frameworks (RMFs).
Warning:
If you’re interested in passing the CISSP certification exam, I would read this post 5 times and ask questions. Because this is truly one of the core topics of information security.
Risk Management Frameworks
Let’s start from the beginning, shall we?
A Risk Management Framework is defined as a structured process that allows an organization to identify and assess risk, reduce it to an acceptable level, and ensure that it remains at that level.
As you can imagine, there are many RMFs out there. However, there are very few of them that are widely accepted, so let’s focus on those.
As a Cybersecurity professional, you should be at least aware of the following frameworks and be able to choose the one that fit your organization’s particular needs.
Put your knowledge to the test: Try my cybersecurity quizzes and see how well you understand risk management frameworks in practice: CybersecErich: Quiz Hub
NIST Risk Management Framework
The National Institute of Standards and Technology (NIST) defines the RMF in three key Special Publications: SP800-37, SP800-39, and SP800-30.
This framework incorporates the essential elements of risk management that every cybersecurity professional should understand.
One caveat: it was originally designed for federal government entities, so in practice, you may need to adapt it to fit your organization’s specific needs.
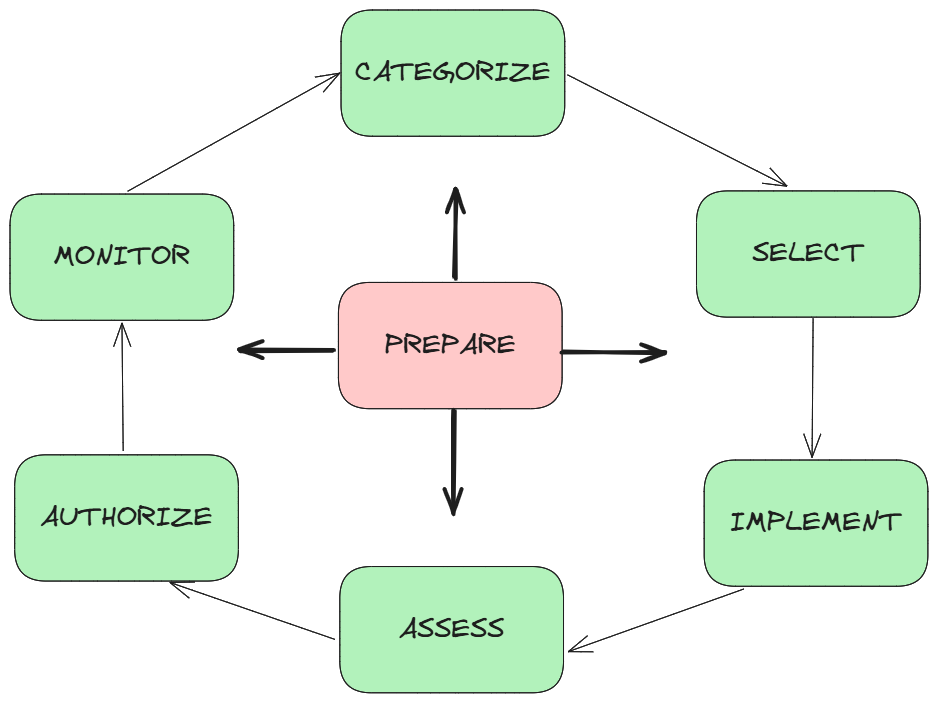
At its core, the RMF follows a seven-step process (see picture below).
The first thing to know is that it’s a continuous cycle — our information systems are always evolving, and risk management never really stops.
With that in mind, let’s break down each step.
Prepare
Set the stage for effective risk management. Identify your organization’s mission, critical assets, and resources, then define the overall risk management strategy. Think of this as deciding the rules of the game before playing.Categorize
Determine the impact level of the system you’re protecting. Ask: What happens if this system is compromised? Systems can be low, moderate, or high impact depending on confidentiality, integrity, and availability requirements. This step guides how strict your controls need to be.Select
Choose appropriate security controls to address identified risks. Use guidelines like NIST SP800-53 to select controls that balance security, cost, and operational impact. This step is about planning how to protect your system effectively.Implement
Apply the selected controls in practice. This can include technical measures (firewalls, encryption), administrative processes (policies, training), and physical safeguards (locks, monitoring). Implementation turns planning into action.Assess
Test and evaluate whether the controls work as intended. Conduct audits, penetration tests, and reviews to confirm effectiveness. This step identifies gaps or weaknesses before the system goes live.Authorize
Decision-makers review all assessment results and authorize the system to operate. They weigh the residual risk against organizational tolerance. Authorization is essentially giving the green light while acknowledging remaining risks.Monitor
Risk management is continuous. Track system performance, new threats, and control effectiveness. Regular updates, incident reports, and audits ensure the system remains secure over time.
And that’s it! Not so bad, right?
Just one seven-step, never-ending cycle, simple in concept. Of course, the real challenges appear when you actually try to implement the steps.
The good news? At a conceptual level, the NIST RMF is easy to understand. So let’s leave the tricky parts for next time.
ISO/IEC 270005
While NIST RMF gives you a structured, step-by-step process, ISO/IEC 27005 takes a slightly different approach. It focuses on decision-making and risk treatment options rather than rigid processes.
This standard is part of the ISO/IEC 27000 family and provides guidance for information security risk management, helping organizations identify, assess, and respond to risks in a systematic way.
The core idea?
Every risk has a possible treatment strategy. ISO/IEC 27005 highlights four main options:
Mitigate – Reduce the likelihood or impact of the risk. Think of installing firewalls or updating software.
Accept – Acknowledge the risk without taking further action, often because it’s minor or cost-prohibitive to address.
Transfer – Shift the risk to another party, like buying cybersecurity insurance or outsourcing a service.
Avoid – Eliminate the risk completely, for example by discontinuing a vulnerable process.
Unlike NIST, ISO/IEC 27005 is less prescriptive and more about understanding your options and making informed decisions. It’s flexible, and can be adapted to fit any organization, whether a small business or a global enterprise.
And that’s it!
It’s really straightforward conceptually.
You identify your risks, decide what to do about each one, and monitor them over time. The tricky part comes when you try to implement these strategies in real-life situations, but that’s a story for another post.
Key Takeaways: Risk Management Frameworks
If you’re reading this, congratulations! It would mean a lot to me if you could let me know how you liked this post in the comments: I read every single one of them.
And before you go, let’s review the key takeaways you should remember:
Risk management is continuous. Every system changes, so RMFs are never “done.”
NIST RMF = process-focused. Seven steps (Prepare, Categorize, Select, Implement, Assess, Authorize, Monitor) guide you from planning to continuous monitoring. Think of it as a structured roadmap.
ISO/IEC 27005 = decision-focused. Four treatment strategies (Mitigate, Accept, Transfer, Avoid) help you choose how to respond to each risk. Flexibility is key.
Both frameworks matter for CISSP. You don’t just memorize steps — you understand why each step or decision matters.
Concept ≠ Implementation. Understanding frameworks conceptually is easy; the real challenge is applying them in practice.
That will be all for today, and I’ll see you next week!
Ready to level up your cybersecurity skills?
Comment below and tell me what you think about risk management frameworks.
Take the quiz to test your understanding: CybersecErich: Quiz Hub
Subscribe (free or paid) to get new posts straight to your inbox.
Share this with a friend studying for CISSP, or anyone curious about cybersecurity.
💡 Pro tip: Your questions might show up in the next post, so don’t hold back!


Great post!
I would add that : one of the toughest parts is making sure these frameworks actually line up with real business goals. At the end of the day, risk management isn’t just about avoiding threatsit’s about helping the organization take smart risks without holding it back.