🔐 Hashing: What It Is and Why It’s Not the Same as Encryption
Want to understand one of the key concepts in cybersecurity? In this post, we break down the basics of hashing and take a look why it matters in today's world.
Now that you've become an expert on encryption in the previous articles, it's time to take a look at another crucial concept used in cybersecurity.
At first glance, hashing might look similar to encryption — both transform data into a different format but serve very different purposes.
🧩 What is Hashing?
Hashing is a one-way process that turns any input (a message, file, or password) into a fixed-length output called a hash. Unlike encryption, you can’t reverse a hash back to the original input. It’s meant to be irreversible.
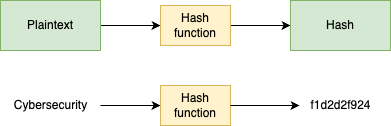
Example:
1. Plaintext = Cybersecurity. Plaintext is an input for the hash function.
2. Hash = f1d2d2f929. No matter what input you'll give to the hash function it will always be the same length.
Hash function
A good cryptographic hash function has these essential properties:
🔁 Deterministic – Same input = always the same output.
📏 Fixed Length Output – No matter the input size, the hash is always the same length.
🧩 Pre-Image Resistance – You can’t figure out the original input from the hash.
🧨 Collision Resistance – It’s very hard to find two different inputs that produce the same hash.
🔀 Avalanche Effect – A tiny change in input = a totally different hash output.
🔒 So, What Is It Used For?
Great, if you’re new to cybersecurity, you’re probably confused right now. I just told you a bunch of definitions that don’t make any sense to you. And that’s okay; let me help you out by giving you real-life use cases for which hashing is crucial.
✅ Password Storage – Instead of storing your actual password, websites store its hash. Even if hackers get access, they don't have the real passwords.
✅ Data Integrity Checks – You can hash a file before and after transmission. If the hash is the same, the file wasn’t tampered with.
✅ Digital Signatures – Hashing plays a key role in ensuring that data hasn’t changed.
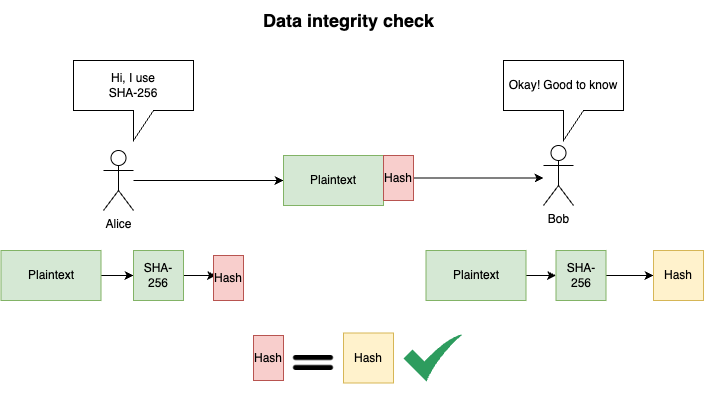
🧪 Example: Verifying Message Integrity with Hashing
Alice wants to send a message to Bob and make sure no one modifies it during transmission.
Alice tells Bob which hash function she will use (e.g., SHA-256).
She generates a hash of her message.
Alice sends both the message and the hash to Bob.
Bob receives the message and uses the same hash function to generate a hash from the message he received.
He compares his hash to Alice’s hash.
✅ If the hashes match, the message wasn’t changed.
❌ If they don’t match, the message was tampered with during transmission.
🧠 Hashing vs Encryption — What’s the Difference?
Let’s summarize the biggest differences between encryption and hashing:
Reversibility
Encryption is reversible — if you have the correct key, you can decrypt the data and get back the original.
Hashing is one-way — once data is hashed, you can’t turn it back into its original form.
Purpose
Encryption is used to protect the confidentiality of data.
Hashing is used to ensure integrity — making sure data hasn’t been altered.
Use of Keys
Encryption requires keys (for both encryption and decryption).
Hashing doesn’t use keys — the same input always gives the same output.
Output
Encryption outputs ciphertext — it looks like gibberish but can be decrypted.
Hashing outputs a fixed-length string (the “hash”) that uniquely represents the input.
Common Use Cases
Encryption: Secure communication, encrypted files, VPNs.
Hashing: Password storage, file integrity checks, digital signatures
Conclusion
Understanding both hashing and encryption is crucial for any Cybersecurity specialist. I hope this post helped you to understand the basics of hashing and what it is used for.
And if you’ve made it this far — congratulations! 🎉 You now know enough to tackle many questions in entry-level cybersecurity certifications.
But there’s still more to learn — and I’ve got you covered.
👉 Make sure to follow me so you don’t miss the next posts in this series!
📩 Subscribe to my Patreon for free so you won’t miss the next posts — especially if you’re just starting your journey into cybersecurity!