[Guest Post] You Passed the CISSP. Now What? What If the Real Test Starts Now?
Three questions the exam didn’t cover. AI just made them mandatory. Expert Insights from ToxSec: AI Security Engineer at Amazon, ex-NSA, USMC, M.S. Cybersecurity, and CISSP.
Hello everyone,
Today’s post is special, it is the very first guest post on this platform.
And I couldn’t think of a better person to start with than ToxSec .
I’ve followed his work since his early Substack days, and I always look forward to his articles and his Podcast episodes.
And there is no doubt why. He’s one of the rare voices who truly understands both AI and cybersecurity, given his impressive background. AI Security Engineer at Amazon, ex-NSA, USMC, holding both M.S. Cybersecurity and the CISSP certificate, which is how we connected in the first place.
This article is a perfect fit for anyone who just passed the CISSP, is studying for it, or already works in security but feels the ground shifting under their feet.
It asks the questions the exam doesn’t, the ones AI just made unavoidable.
If you want to see more collaborations like this, let us know in the comments.
So let’s listen to an expert:
You Passed the CISSP. Now What?
Three questions the exam didn’t cover. AI just made them mandatory.
TL;DR: You learned the frameworks. Now AI is rewriting the rules faster than any exam can keep up. Here are three questions worth asking yourself. The cert got you here. Now here’s the work.
“The exam tested what you know. Now it’s on you to figure out what you’d do when the model can’t explain itself.”
Who Owns the Risk When Nobody Understands the Decision?
You know risk assessment. Quantitative, qualitative, asset value times probability times impact. You can calculate this in your sleep.
Cool. Now let’s try doing it for a black box.
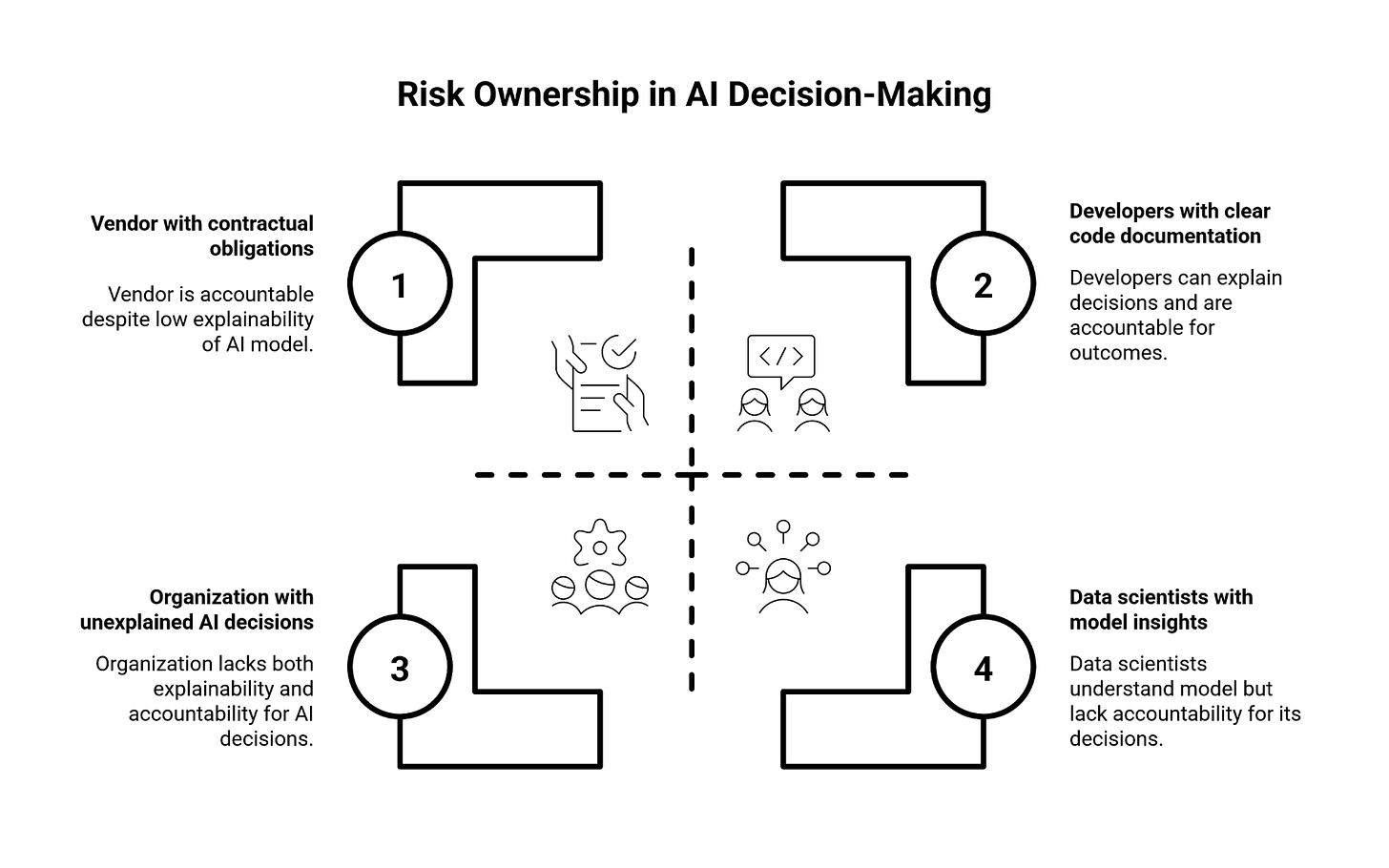
An AI model makes a lending decision, flags a transaction, or grants access. Something breaks. Data leaks. Money disappears. So whose fault is it?
The developers? They shipped working code. The vendor? They sold you exactly what they promised. Your team? They followed the deployment checklist to the letter.
Here’s the problem: the model worked exactly as designed, but nobody can explain why it made that call. Not the engineers. Not the data scientists. And definitely not you.
The Bank for International Settlements already warned that poorly governed AI models could trigger systemic risk. A major bank got fined this year for an AI credit model that produced biased approvals. The model did its job. The humans couldn’t explain the job it did.
Your CISSP taught you to assess risk. Now it’s on you to figure out what to do when the risk assessment itself is impossible.
So. Who owns it?
What’s Your Response Time When the Attacker Never Stops?
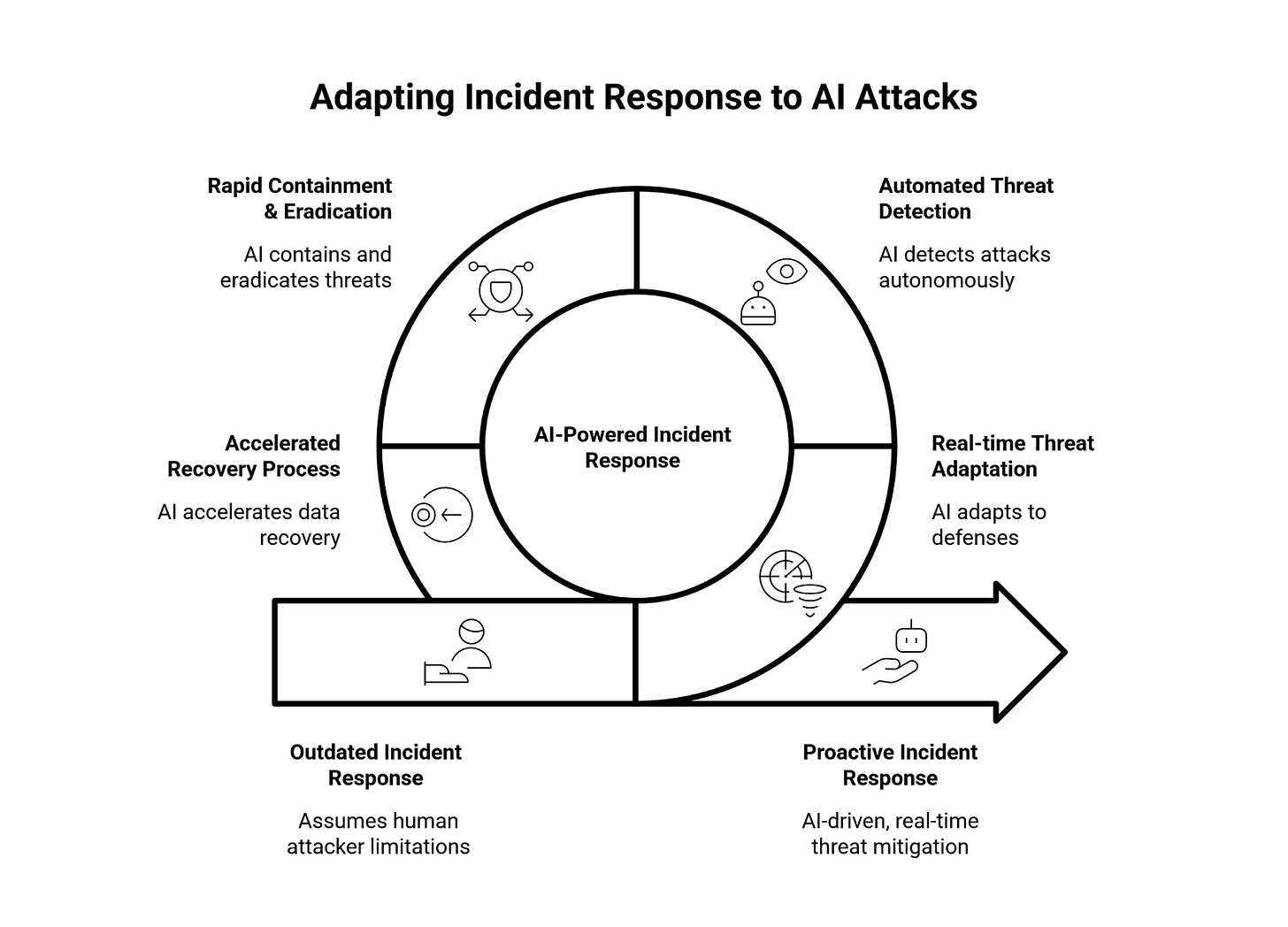
Incident response. Detection, containment, eradication, recovery. You know the phases, and you’ve probably run tabletops.
Here’s a question worth adding to those exercises: what happens when the attacker is a loop?
September 2025, Anthropic discloses they disrupted a state-sponsored campaign where AI agents executed cyberattacks autonomously with minimal human oversight. The AI didn’t advise the attack. The AI was the attack. Thirty global targets, machine speed, no breaks.
Your playbook assumes humans on the other end. Humans who sleep, make mistakes, and slow down.
AI doesn’t do any of that.
Breach timelines are compressing fast. Exfiltration in hours, sometimes faster. Your SOC is still triaging alerts while the adversary already left with the data.
Palo Alto Networks says by 2026, most advanced attacks will use AI that adapts in real-time to your defenses. Your incident response plan was written for an opponent that gets tired.
Does yours?
When Did “Check for Typos” Become Security Advice?
Social engineering, awareness training, phishing simulations. You know the drill.
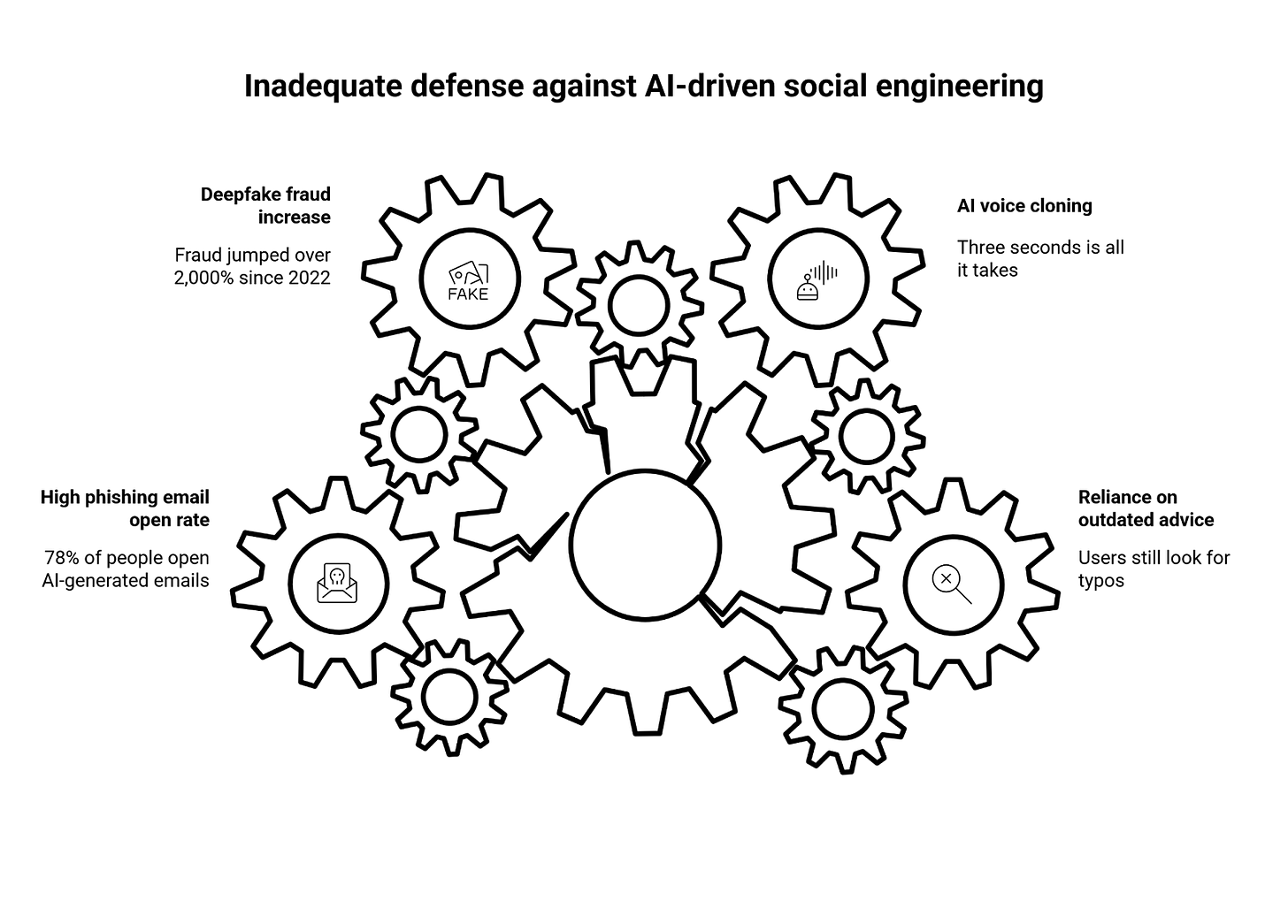
You also know what you tell users: look for misspellings, check the sender address, hover before you click.
That advice is dead. It just doesn’t know it yet.
Early 2024, a finance worker at Arup joins a video call with the CFO and senior leadership. Standard process, authorization for a $25.6 million transfer. Except everyone on that call was synthetic. AI-generated faces and AI-cloned voices, all scraped from LinkedIn and public footage.
Voice cloning takes three seconds of audio now. Three seconds is all it takes.
Deepfake fraud jumped over 2,000% since 2022, and vishing attacks were up 442% last year. Here’s the stat that should keep you up at night: 78% of people open AI-generated phishing emails. The grammar isn’t bad anymore, so don’t rely on those tells.
Your CISSP covered the human element. Good. Now what’s your answer when the human can’t tell human from machine?
Subscribe if you want the next breakdown. The gap between “that won’t fool anyone” and “we lost $25 million” is about one video call.
What Are You Going to Do About It?
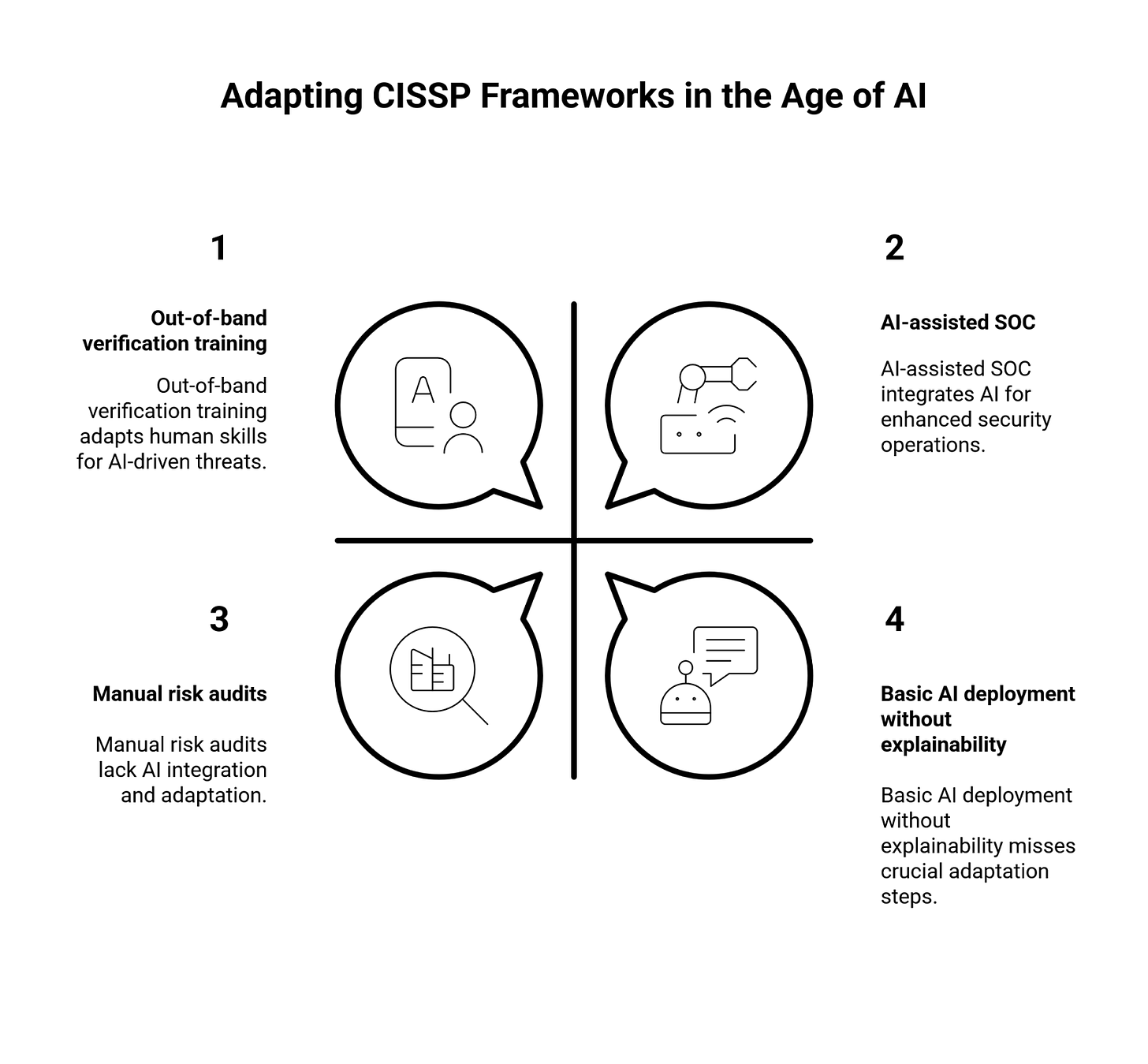
Your frameworks still matter. Risk management, security operations, the human factor. Those foundations don’t disappear just because AI showed up.
But they need new questions bolted on.
For risk: if you can’t audit the decision, you can’t own the risk. Demand explainability before deployment, and if the vendor can’t show you how the model thinks, that’s your answer right there.
For operations: AI-assisted defense is the floor now. Fighting automation with manual process is a losing bet, and if your SOC is still running at human-speed, you’re already behind.
For social engineering: stop training people to spot fakes and start training them to verify out-of-band. The Ferrari deepfake attack failed because an exec asked a question only the real CFO could answer. Process beats detection.
You don’t need to become an AI expert. You just need to know which of your assumptions stopped being true. That’s the work now.
Frequently Asked Questions
Q: Is CISSP still worth it if AI is changing everything? A: Absolutely. The frameworks are foundations, but foundations need updates when the ground shifts. AI is the earthquake. Your cert is valuable, and your next move is extending it.
Q: Will ISC² update the exam for AI threats? A: They will, since they update every three years. But AI moves fast, so get ahead of it now. When the exam catches up, you’ll already be there.
Q: What’s the single most important thing CISSP holders should learn about AI? A: Where your frameworks stop working. Not how AI works technically, but where your existing mental models break down. That’s the gap that gets exploited.
A final thank you
A big thank you to ToxSec for sharing this breakdown with all of us. Few people understand the AI/security intersection as clearly as he does.
If you want more insights like this, go follow his work. You won’t regret it.




Loved this line: "You don’t need to become an AI expert. You just need to know which of your assumptions stopped being true. That’s the work now." I think this applies across the board to every sector.
A great read, team!
Thanks both for this excellent article. I learned a lot in reading this. I think for me the key takeaway is that process beats detection. Ultimately we need to really be thinking about working with our employers and our employees to make sure that people are asking the right questions rather than trying to spot patterns, which themselves are becoming very difficult to tell apart.