Cybersecurity Controls from Zero to Hero
There are hundreds of ways to protect your assets, but without a clear way to categorize them, it all gets confusing very quickly. If you're serious about cybersecurity, read this!
Think firewalls are all you need to protect your business?
In reality, cybersecurity controls come in many shapes, from physical fences to awareness training.
But here’s the problem:
How do we make sense of it all?
How do we know which controls to use?
That’s where categorization comes in.
In cybersecurity, we don’t just throw tools at the wall. We organize them into types, based on their purpose and function.
Let’s break down the core types of security controls with simple examples you’ll actually remember.
But before we dive into the categorization, let me remind you that each security control exists only to support one of the three core cybersecurity objectives - CIA.
If you’re not familiar with them, I’d suggest stopping reading about controls and reading the following article about cybersecurity fundamentals!
Two Ways to Classify Security Controls
There are two main ways we categorize controls in cybersecurity:
By how they are implemented
By what purpose they serve
If you feel a little confused by now, don’t worry. Let’s take it step by step.
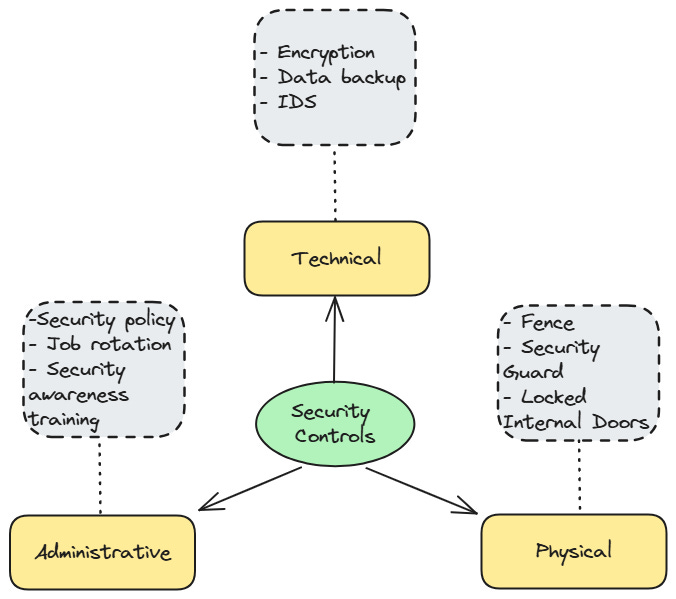
Classification #1: How the Control Works
Of course, there are many ways to categorize controls, but we will focus on the most common and important ones.
Warning: The categorization of security controls is crucial knowledge for most cybersecurity certificates, such as CC or CISSP.
The one that any cybersecurity specialist should be familiar with divides controls into three main categories:
Administrative Controls
Non-technical methods such as policies, procedures, and guidelines.
Think: security training, hiring practices, risk assessments.
Technical Controls (a.k.a. Logical Controls)
Implemented through technology. (HW and SW components)
Think: firewalls, antivirus software, encryption.
Physical Controls
Protect the physical environment.
Think: locks, cameras, fences, security guards.
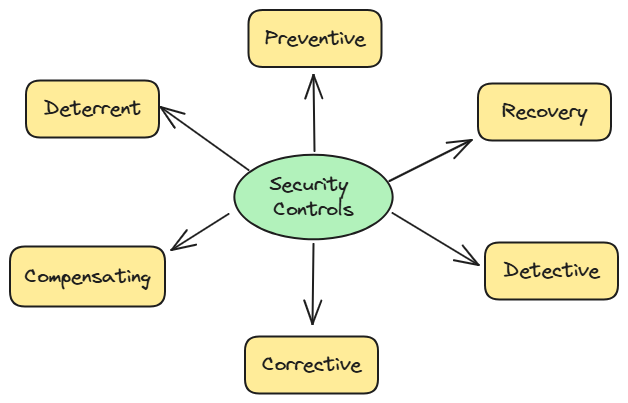
Classification #2: Why the Control Exists
While the previous categories tell us how a control is implemented (admin, technical, physical), this model tells us why the control exists and what purpose it serves.
By understanding the different types of controls, you'll be able to make more informed decisions about which ones are best suited for specific situations.
The six different control types are:
Preventive – Stops unwanted events before they happen.
Detective – Identifies and alerts when something happens.
Corrective – Responds and fixes issues after detection.
Deterrent – Discourages malicious actions through fear or consequence.
Recovery – Helps restore operations after an incident.
Compensating – Provides an alternative when primary controls aren't feasible.
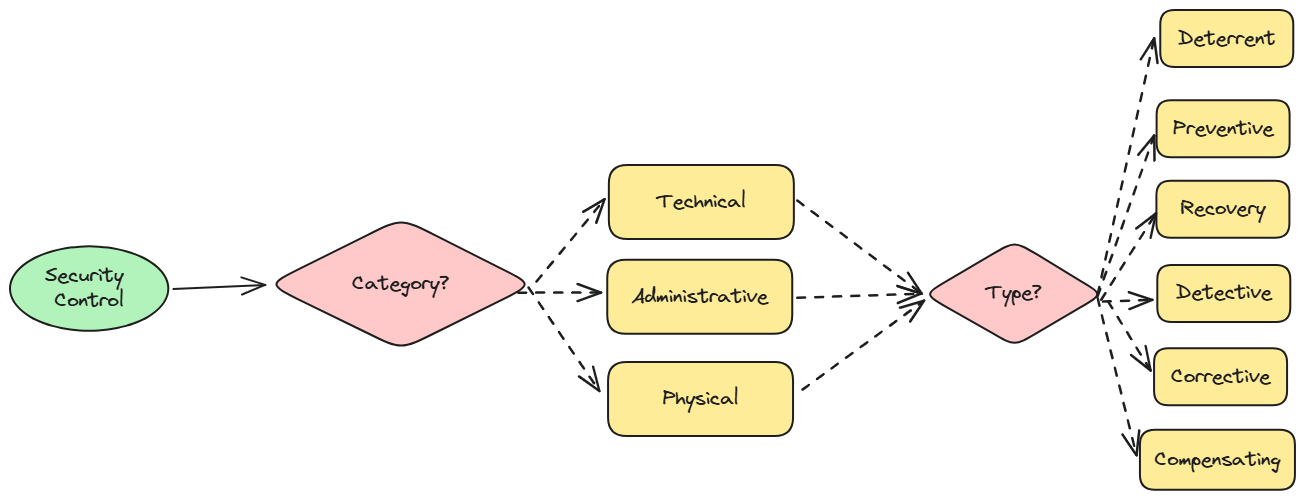
How does it all work together?
You might be asking yourself: How does this all work?
Two different ways to categorize controls, which one is better? Which one should we use?
The answer is: Both are equally valid and complement each other.
They simply view security controls from different perspectives. So don’t choose one over the other by default. Instead, use whichever classification makes the most sense for the situation you're dealing with, or use them both at the same time!
I think the best way to categorize tools is described in the following diagram:
Examples that will help you figure it out
Still a little confused?
Don’t worry. A few examples will clear it up.
Honestly, I never truly understand concepts until I see how they work in practice.
Let’s use the workflow described in the picture above and try it for a couple of security controls.
Encryption
Category: Technical (Achieved through technology)
Type: Preventive
Explanation: Encryption protects data by making it unreadable to unauthorized users. Therefore, it is preventive as it is implemented even before an incident occurs.
Security Awareness Training
Category: Administrative
Type: Deterrent
Explanation: Training helps employees recognize threats like phishing, prevent human error, and reduce risk.
Fences
Category: Physical
Type: Deterrent
Explanation: Fences physically restrict access and discourage unauthorized individuals from entering secure areas.
Summary
If you’re reading this, congratulations — most people don’t make it this far.
By now, you understand that cybersecurity isn’t just about buying the latest tools. It’s about knowing why you use them and how they work together.
And this isn’t just CISSP theory.
It’s a skill you’ll use every day as a cybersecurity professional.
If you understand both types of classifications, you’ll be able to:
Build more effective security programs
Spot gaps in your systems
Communicate clearly with decision-makers
Pass exams like the CISSP with confidence
I hope this article helped you understand how to categorize security controls and why it matters.
Do you really understand it?
Let’s find out.
As always, I’ve prepared a 10-question quiz to test your knowledge.
👇 Ready?
💬 Got 8/10 or more? Drop your score in the comments.
📤 Know someone who still doesn’t understand what security control is? Send this their way.
🧠 Curious where this journey leads? Subscribe here and join me on the path to CISSP. I’d love to have you on board. 👇


9 out of 10
Great post.