CISSP Domain 3: Why Two Systems Using AES Can Be Completely Different in Security
Knowing ciphers isn’t enough. Not for the CISSP exam, and not in real life. Just because a system uses AES doesn’t mean it’s secure. Implementation matters!
Knowing 3DES and AES won’t get you far on the CISSP exam.
There’s a crucial concept in cryptography that is often overlooked, and without it, you won’t find it very difficult to answer the exam questions correctly.
CISSP note: Cryptography is only one part of Domain 3. Do not spend too much time on these topics. I will tell you what to focus on at the end of this post!
Both 3DES and AES are block ciphers.
That means they encrypt and decrypt data in fixed-size blocks.
But here’s the twist:
It’s not just about the cipher, it’s about how those blocks are processed.
And those different ways are called modes of operation.
Modes of operation
Let us take a look at the various modes of operation that you need to know for the exam, along with their advantages and disadvantages.
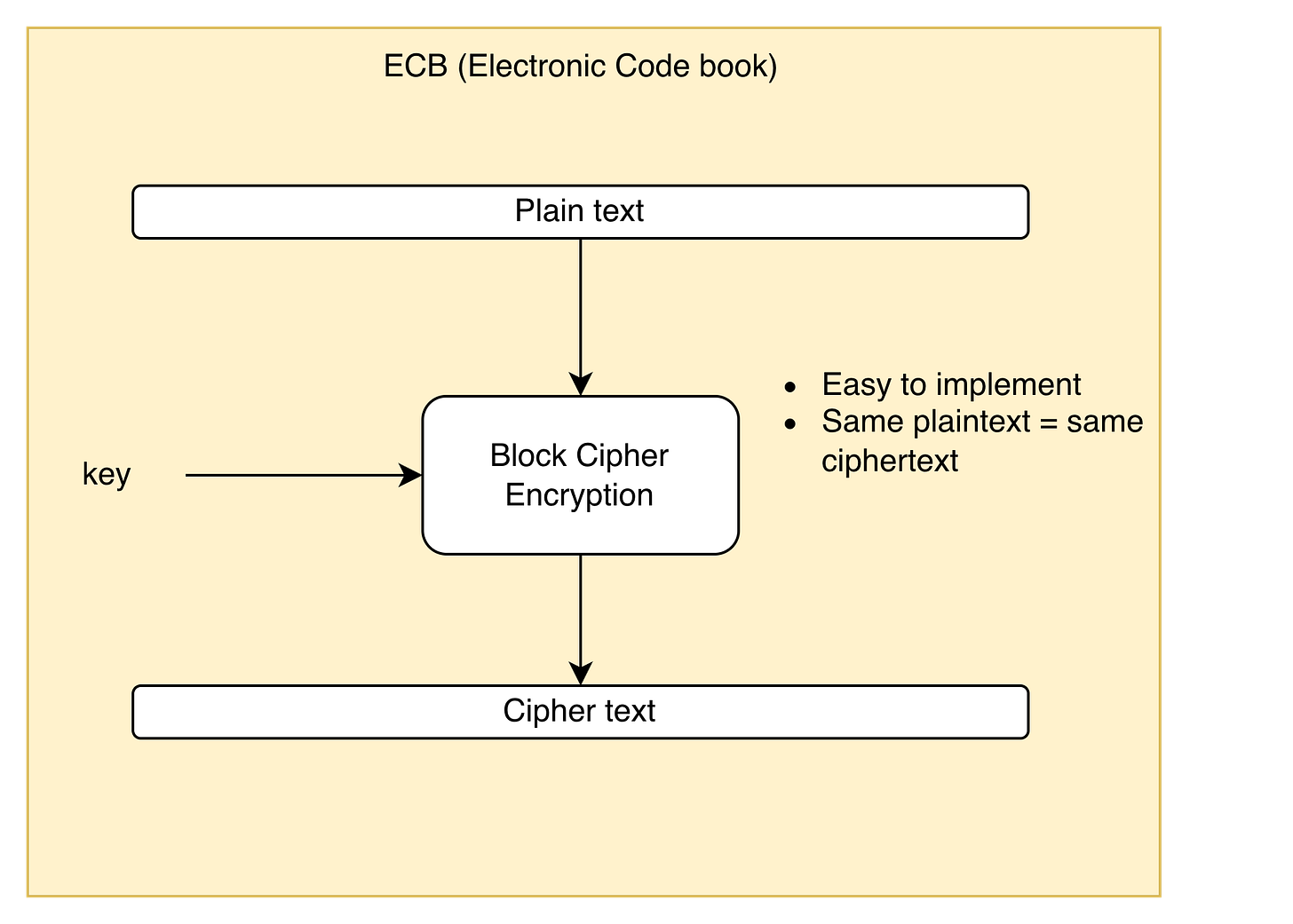
ECB (Electronic Codebook)
Description: Encrypts each block of plaintext independently using the same key.
Advantages: Simple to implement and very fast.
Disadvantages: Identical plaintext blocks produce identical ciphertext blocks, revealing patterns in the data. Offers the least security among block cipher modes and should never be used for sensitive information.
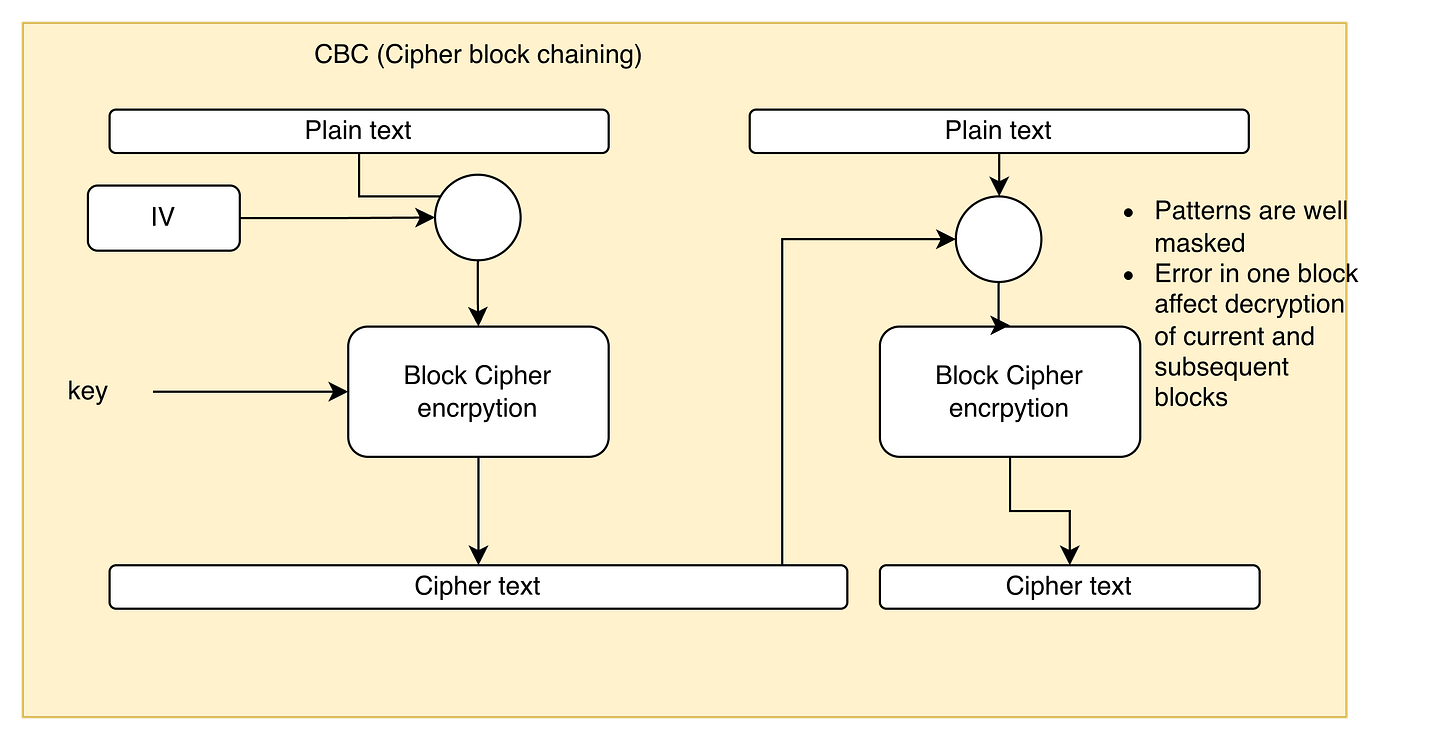
CBC (Cipher Block Chaining)
Description: Each block of plaintext is XORed with the previous ciphertext block before encryption.
Advantages: Patterns are well masked
Disadvantages:
Requires an Initialization Vector (IV)
Cannot be parallelized
An error in one block affects the decryption of the current and subsequent blocks
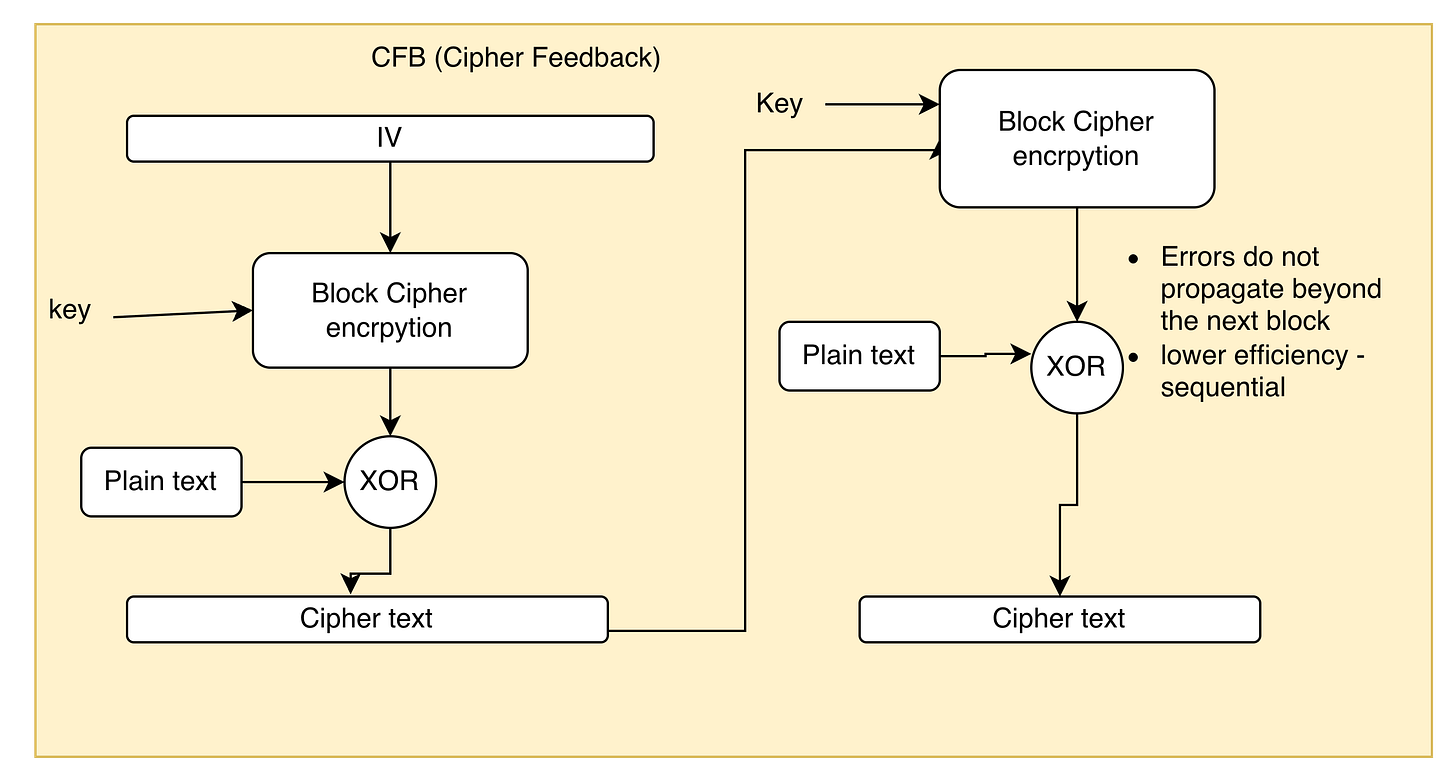
CFB (Cipher Feedback)
Description: Converts a block cipher into a self-synchronizing stream cipher by feeding ciphertext back into the encryption process.
Advantages: Errors do not propagate beyond the next block
Disadvantages: Low efficiency
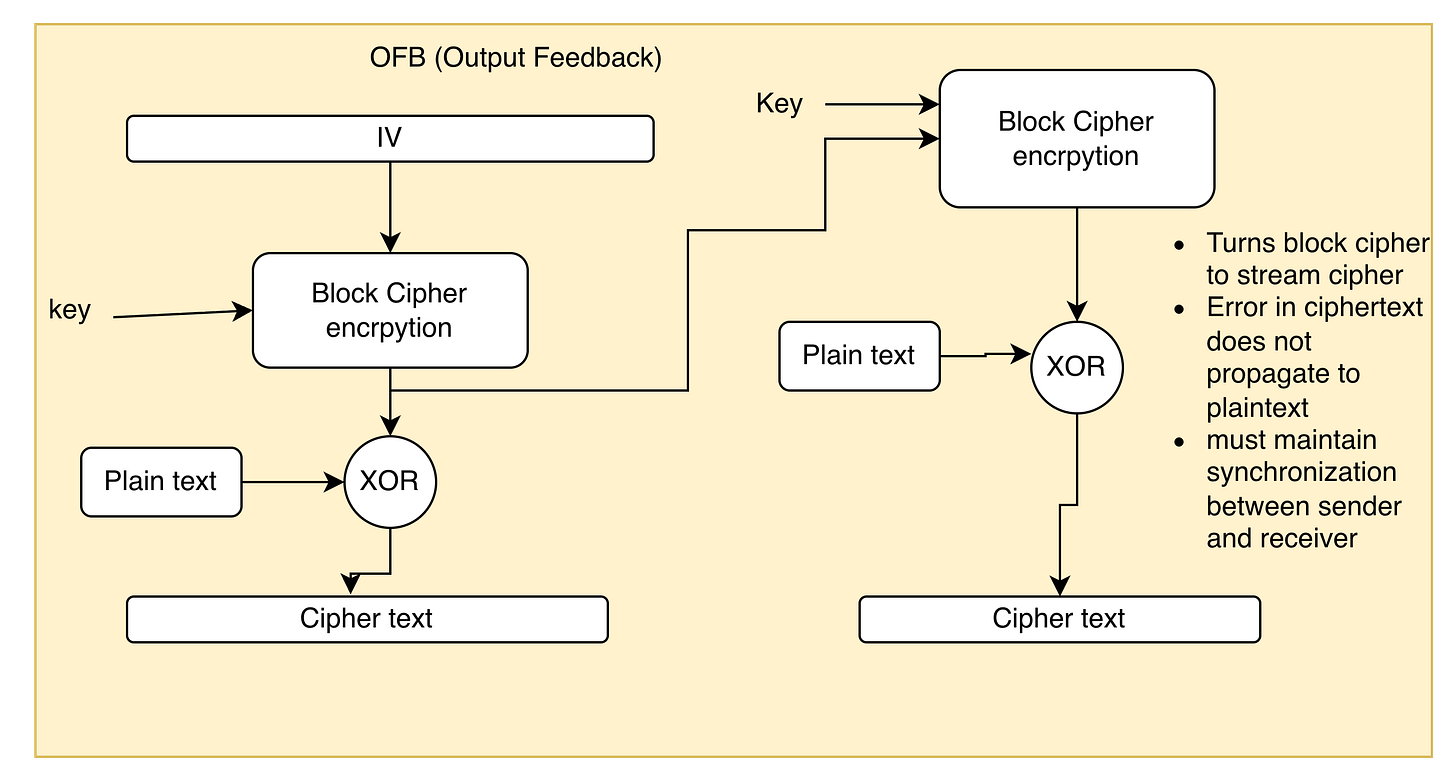
OFB (Output Feedback)
Description: Uses the output of encryption (not the ciphertext) to create a keystream for XOR with plaintext.
TURNS BLOCK CIPHER TO A STREAM CIPHER
Advantages: No error propagation. One corrupted bit affects only that bit
Disadvantages:
If the same IV is reused, identical keystreams appear.
It requires synchronization between the sender and the receiver
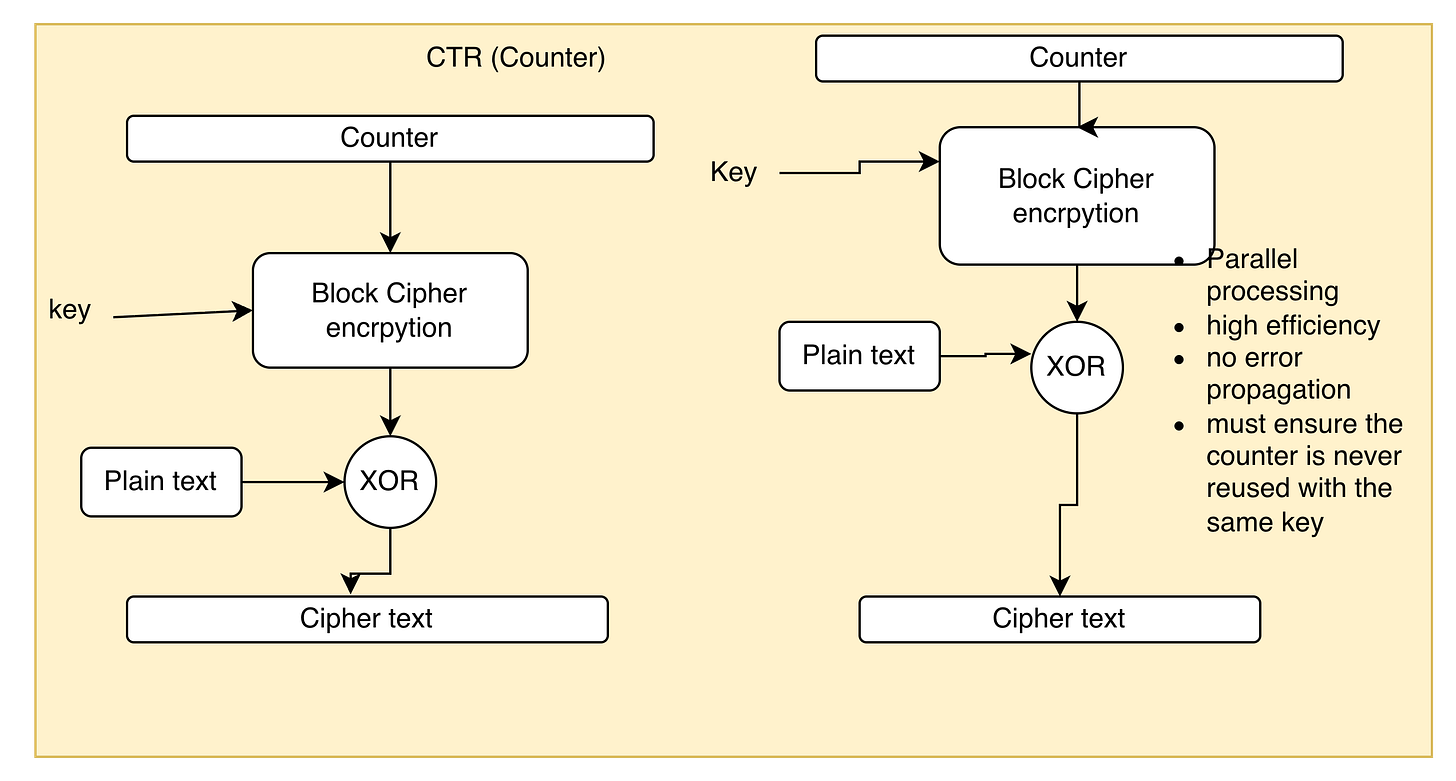
CTR (Counter Mode)
Description: Combines a nonce (unique value) with a continuously incrementing counter, encrypts that, and XORs the result with plaintext.
Advantages:
Very fast
Fully parallelizable
Disadvantages:
Reusing a nonce–key pair completely compromises security.
Proper implementation is critical.
REMEMBER: The counter cannot be reused with the same key
GCM (Galois/Counter Mode)
Description: Builds on CTR mode and adds built-in integrity via Galois field multiplication (creating an authentication tag).
CISSP note: Just remember, it provides integrity.
Advantages:
Provides both confidentiality and integrity
Fast
Widely supported (TLS, IPsec).
Disadvantages:
Slightly more complex
Nonce misuse again breaks security.
Things to remember for the exam
ECB is the least secure mode
Never use ECB for sensitive data
IV must be securely generated and unpredictable, otherwise the security of the cipher is compromised
CTR is considered the best balance of speed and security, and allows parallel processing.
OFB turns a block cipher into a stream cipher
Conclusion
Cryptography has always been one of my strongest topics. But truth be told, the CISSP exam doesn’t dive too deep into it. You’re not expected to memorize algorithms or do math.
You just need to understand the core concepts.
If you remember the five points from the previous section, you’ll be ready to answer almost any question about modes of operation that CISSP can throw at you.
In the end, it’s not about knowing all the details about each operating mode, it’s much more about understanding why each mode exists and what security property it provides.


I remember learning this, I called this Magic Maths, I can see the beauty in the math, factoring the product of two huge prime numbers, numbers large than Elon Musks bank account, my conclusion was if I could really understand it, I would be pretty lonely at a party..... solid article